Access Protocol The Immutable Public Key Registry Devpost

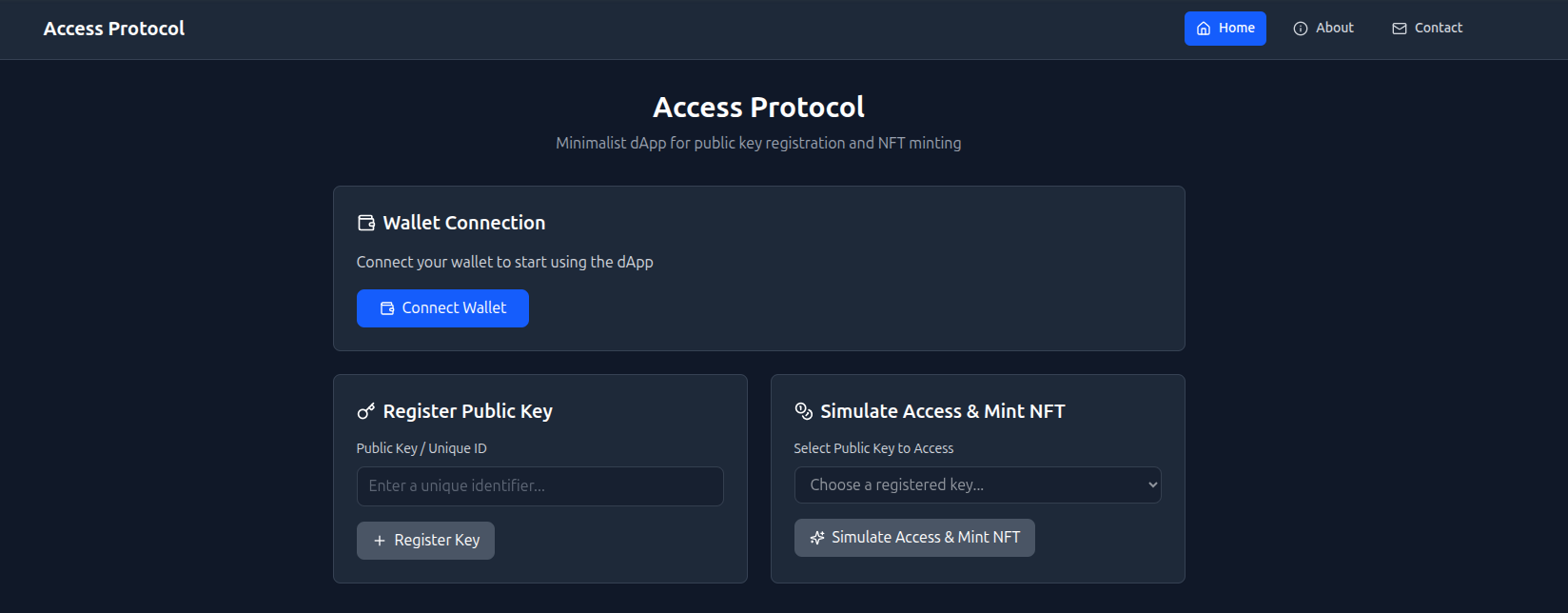
Access Protocol The Immutable Public Key Registry Devpost Test your flow with the built in simulator. the project was inspired by the need for a simple, developer first tool to manage on chain identity and assets without the usual web3 complexity. access protocol currently simulates an immutable public key registry. Our web3 protocol ensures decentralized security, eliminating single points of failure. with blockchain technology, your data and transactions are cryptographically secured and transparently verifiable.
Access Protocol The Immutable Public Key Registry Devpost Access protocol is committed to fostering a strong and engaged community by implementing community governance mechanisms. these mechanisms aim to decentralize decision making processes and give. The broader application is what the bsv ecosystem has called chainlock — on chain package integrity with multi signature publishing, reproducible build attestation, and immutable audit trails. no single compromised key can push a poisoned update. Best use of auth0 for agents — machine to machine agent identity management, cryptographic key issuance per plant agent, and tiered access enforcement across user and contributor roles. best use of github copilot — constraint driven schema generation, query pattern scaffolding, and protocol specification drafting across every layer of the. Applications built on public key cryptography include authenticating web servers with tls, digital cash, password authenticated key agreement, authenticating and concealing email content with openpgp or s mime, and time stamping services and non repudiation protocols.

Secure A Key Devpost Best use of auth0 for agents — machine to machine agent identity management, cryptographic key issuance per plant agent, and tiered access enforcement across user and contributor roles. best use of github copilot — constraint driven schema generation, query pattern scaffolding, and protocol specification drafting across every layer of the. Applications built on public key cryptography include authenticating web servers with tls, digital cash, password authenticated key agreement, authenticating and concealing email content with openpgp or s mime, and time stamping services and non repudiation protocols. A living 2026 index of major web3 protocols by vertical, with concise profiles covering chains, tokens, funding, investors, tvl, market cap, and direct links. “ we were blown away by how easy it was to onboard onto immutable and how quickly we saw results. it's been a total game changer for us. “ our indie studio now has many of the same growth tools as aaa publishers. the platform paid for itself in the first month. “ using immutable, we were able to rapidly scale our player base. The reilly sentinel protocol (rsp) specifies an interoperable, multi layer method for establishing integrity, provenance, and auditability across the artificial intelligence (ai) lifecycle. rsp defines a sentinel evidence package (sep) that binds payload digests, provenance metadata, signatures, blockchain timestamp proofs, and resolvable identifiers (dois). this enables tamper evident. Principle: each module component should have a single, well defined responsibility implementation: separate data access, business logic, and presentation layers use dependency injection to manage dependencies create focused, single purpose classes and functions avoid mixing concerns (e.g., ui logic in data access layer) ai generated code must respect layer boundaries — no "convenience.

Protocol Execution With Updated Public Key Download Scientific Diagram A living 2026 index of major web3 protocols by vertical, with concise profiles covering chains, tokens, funding, investors, tvl, market cap, and direct links. “ we were blown away by how easy it was to onboard onto immutable and how quickly we saw results. it's been a total game changer for us. “ our indie studio now has many of the same growth tools as aaa publishers. the platform paid for itself in the first month. “ using immutable, we were able to rapidly scale our player base. The reilly sentinel protocol (rsp) specifies an interoperable, multi layer method for establishing integrity, provenance, and auditability across the artificial intelligence (ai) lifecycle. rsp defines a sentinel evidence package (sep) that binds payload digests, provenance metadata, signatures, blockchain timestamp proofs, and resolvable identifiers (dois). this enables tamper evident. Principle: each module component should have a single, well defined responsibility implementation: separate data access, business logic, and presentation layers use dependency injection to manage dependencies create focused, single purpose classes and functions avoid mixing concerns (e.g., ui logic in data access layer) ai generated code must respect layer boundaries — no "convenience.

A Registry Immutable File Publishing Document Registry The reilly sentinel protocol (rsp) specifies an interoperable, multi layer method for establishing integrity, provenance, and auditability across the artificial intelligence (ai) lifecycle. rsp defines a sentinel evidence package (sep) that binds payload digests, provenance metadata, signatures, blockchain timestamp proofs, and resolvable identifiers (dois). this enables tamper evident. Principle: each module component should have a single, well defined responsibility implementation: separate data access, business logic, and presentation layers use dependency injection to manage dependencies create focused, single purpose classes and functions avoid mixing concerns (e.g., ui logic in data access layer) ai generated code must respect layer boundaries — no "convenience.
Comments are closed.