Aws Key Leaked
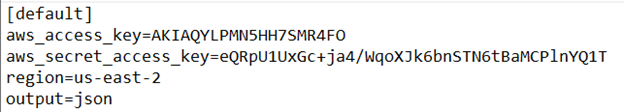
What Happens When You Accidentally Leak Your Aws Api Keys Guest Diary A massive database of over 1,200 unique amazon web services (aws) access keys has been amassed and exploited in a ransomware campaign. administrators of exposed aws s3 buckets are finding their files encrypted except for a ransom note demanding payment in bitcoin. Aws's own scanner will email you… right after someone else has already tried the keys. here's the 3 step fix (the order matters 👇): 1. rotate the secret first → revoke regenerate in aws.

Aws Access Key Scaler Topics In a significant security breach, numerous amazon web services (aws) customers fell victim to a sophisticated cyberattack that exposed sensitive data, including login credentials, api keys, and source code. Awskeylockdown is a security automation tool designed to enforce immediate deactivation of aws access keys associated with iam users flagged by the awscompromisedkeyquarantinev* policy. Your developers might be leaking secrets without even realizing it. onsec finds aws keys, session tokens, internal urls, and even production credentials… all publicly exposed in: 🔹 github. A massive database of over 1,200 unique amazon web services (aws) access keys has been amassed and exploited in a ransomware campaign. administrators of exposed aws s3 buckets are finding their files encrypted except for a ransom note demanding payment in bitcoin.
Leaked Bitcoin Private Keys From Github Your developers might be leaking secrets without even realizing it. onsec finds aws keys, session tokens, internal urls, and even production credentials… all publicly exposed in: 🔹 github. A massive database of over 1,200 unique amazon web services (aws) access keys has been amassed and exploited in a ransomware campaign. administrators of exposed aws s3 buckets are finding their files encrypted except for a ransom note demanding payment in bitcoin. The attackers are often fast enough to beat the alerts about exposed keys sent by aws (if the customer uses aws’s security hub and the trusted advisor service), the researchers discovered. More than 158 million aws secret key records, including 1,229 unique aws key pairs, have been discovered in an internet exposed server exploited by a still unknown threat actor to facilitate highly automated ransomware attacks, according to cybernews. A leaked aws key led to cloud intrusion using aws identity center for persistence. datadog reveals attacker’s use of lambda, iam, and telegram bots. How we leaked aws keys via a slack emoji reaction (a true postmortem) incident timeline: june 12, 2025, 3:14 pm developer reacts to a slack message containing aws access key id with 🚀 (celebrating ….
Incident Report Stolen Aws Access Keys Expel The attackers are often fast enough to beat the alerts about exposed keys sent by aws (if the customer uses aws’s security hub and the trusted advisor service), the researchers discovered. More than 158 million aws secret key records, including 1,229 unique aws key pairs, have been discovered in an internet exposed server exploited by a still unknown threat actor to facilitate highly automated ransomware attacks, according to cybernews. A leaked aws key led to cloud intrusion using aws identity center for persistence. datadog reveals attacker’s use of lambda, iam, and telegram bots. How we leaked aws keys via a slack emoji reaction (a true postmortem) incident timeline: june 12, 2025, 3:14 pm developer reacts to a slack message containing aws access key id with 🚀 (celebrating ….
Comments are closed.