A Guide To Authentication Protocols

Authentication Protocols Discover different types of authentication protocols and their use cases to better understand their role in secure and convenient user login. For a detailed technical comparison of these protocols, i've written an in depth guide on jwt, oauth, oidc, and saml that covers the strengths and tradeoffs of each approach.
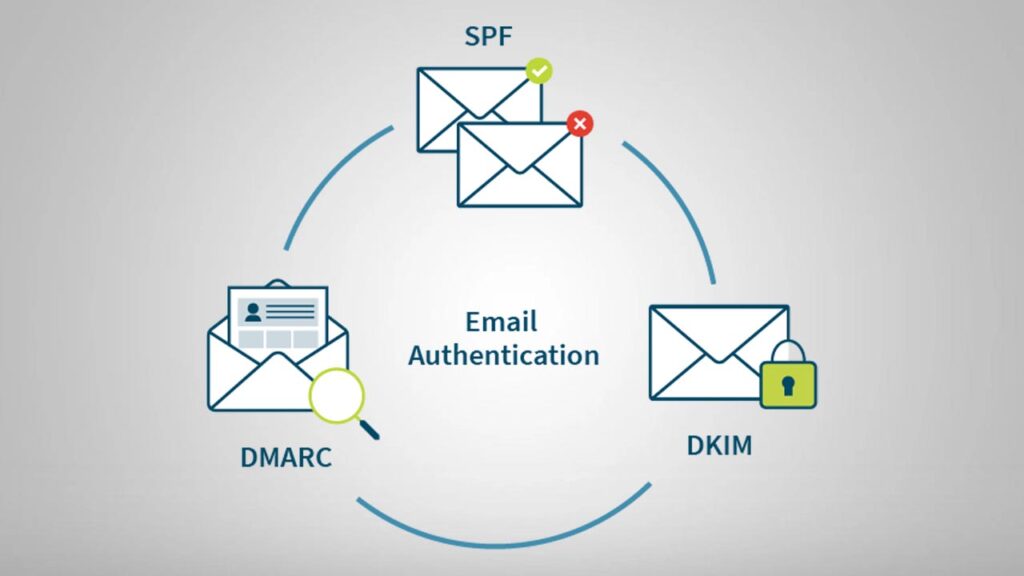
Intro To Email Authentication Protocols Spf Dkim Dmarc The fast identity online (fido) alliance has created two protocols to facilitate online authentication: the universal authentication framework (uaf) protocol and the universal second factor (u2f) protocol. Explore various authentication protocols, their types, and delve into email authentication methods like spf, dkim, and dmarc to enhance security. In this blog, we will explore the most common authentication protocols and will try to explore their merits and demerits. 1. kerberos : kerberos is a protocol that aids in network authentication. this is used for validating clients servers during a network employing a cryptographic key. A comprehensive developer guide to implementing secure authentication in modern applications. covers oauth 2.0, oidc, passwordless authentication, passkeys, and enterprise sso with production ready code examples.
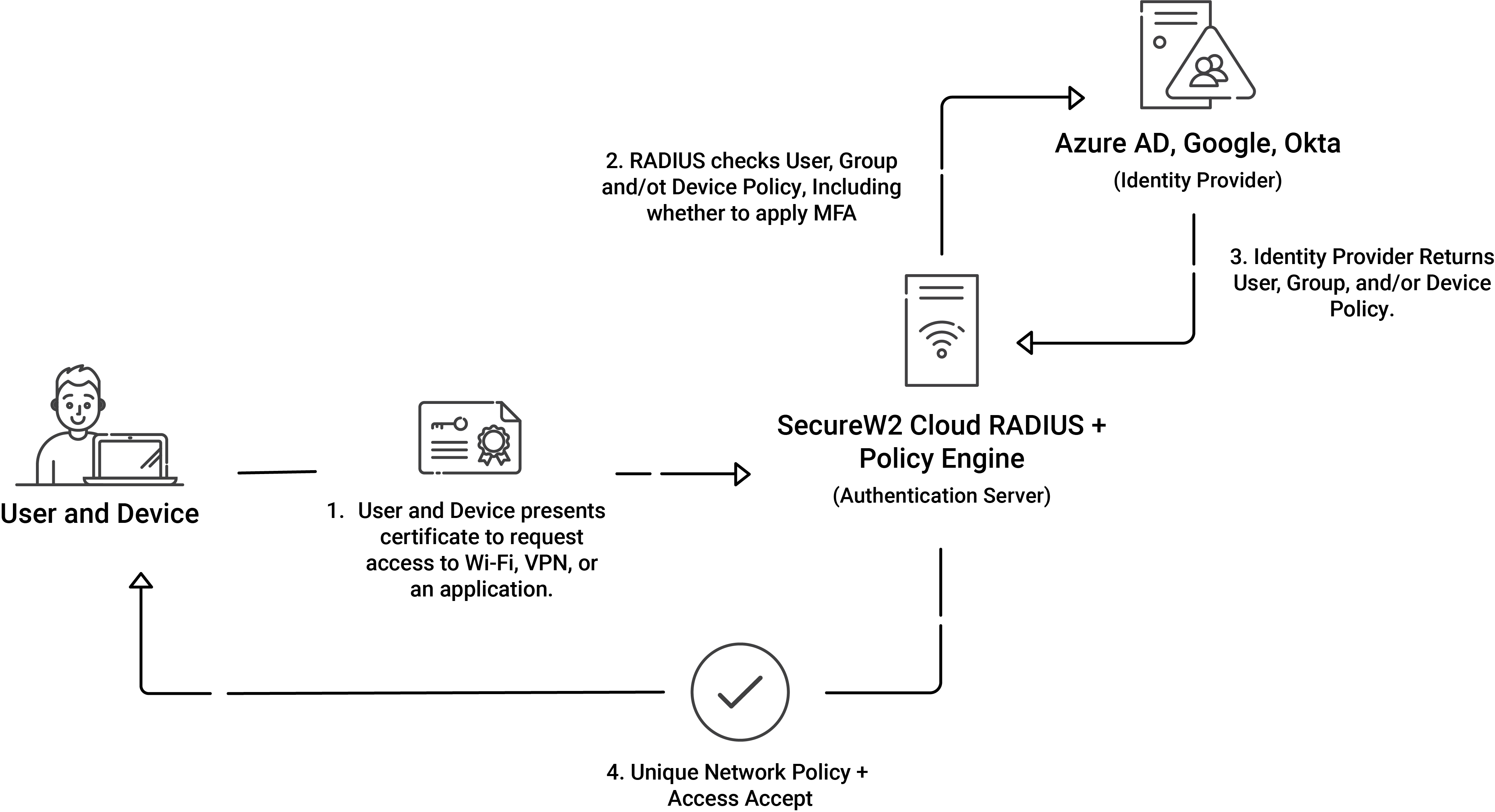
Wep Wpa2 And Wpa3 What These Wi Fi Settings Mean Cloud Radius In this blog, we will explore the most common authentication protocols and will try to explore their merits and demerits. 1. kerberos : kerberos is a protocol that aids in network authentication. this is used for validating clients servers during a network employing a cryptographic key. A comprehensive developer guide to implementing secure authentication in modern applications. covers oauth 2.0, oidc, passwordless authentication, passkeys, and enterprise sso with production ready code examples. Authentication protocols play a vital role in ensuring the integrity and confidentiality of data exchanged over networks. in this article, we will explore the fundamentals of authentication protocols, their types, and their significance in securing network communications. In this post i’ll walk through the most common authentication protocols you’ll encounter, how they actually work in practice, where they shine, and when i avoid them. These standardized frameworks verify identity before granting access to resources. organizations use protocols like oauth, saml, and kerberos across different environments. this guide explains how protocols work, their benefits, and practical implementation strategies for enterprises. Here, you’ll learn all authentication protocols, their main functionalities, and how they can impact your business. by the end, you’ll know how to choose the best protocol for your specific use case. what are authentication protocols, and why do they matter?.
Authentication Protocols Perfmatrix Authentication protocols play a vital role in ensuring the integrity and confidentiality of data exchanged over networks. in this article, we will explore the fundamentals of authentication protocols, their types, and their significance in securing network communications. In this post i’ll walk through the most common authentication protocols you’ll encounter, how they actually work in practice, where they shine, and when i avoid them. These standardized frameworks verify identity before granting access to resources. organizations use protocols like oauth, saml, and kerberos across different environments. this guide explains how protocols work, their benefits, and practical implementation strategies for enterprises. Here, you’ll learn all authentication protocols, their main functionalities, and how they can impact your business. by the end, you’ll know how to choose the best protocol for your specific use case. what are authentication protocols, and why do they matter?.
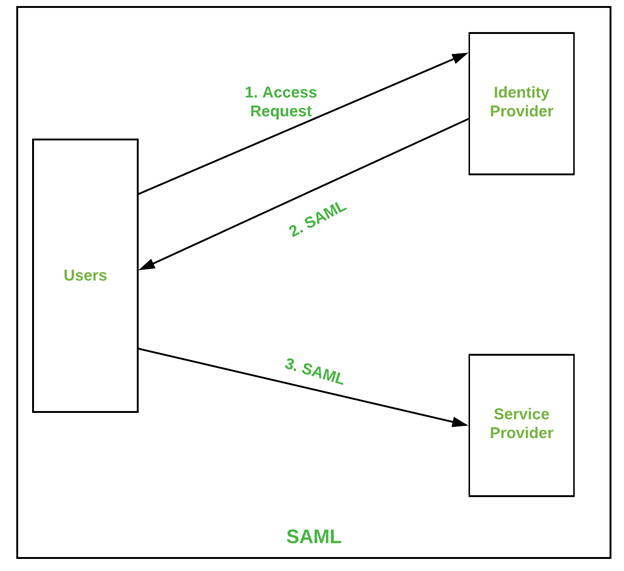
Authentication Protocols Perfmatrix These standardized frameworks verify identity before granting access to resources. organizations use protocols like oauth, saml, and kerberos across different environments. this guide explains how protocols work, their benefits, and practical implementation strategies for enterprises. Here, you’ll learn all authentication protocols, their main functionalities, and how they can impact your business. by the end, you’ll know how to choose the best protocol for your specific use case. what are authentication protocols, and why do they matter?.

Authentication Protocols Types Examples And How They Work Oloid
Comments are closed.