Authentication Protocols

Authentication Protocol Overview Oauth2 Saml Ldap Radius Kerberos In this blog, we will explore the most common authentication protocols and will try to explore their merits and demerits. 1. kerberos : kerberos is a protocol that aids in network authentication. this is used for validating clients servers during a network employing a cryptographic key. Learn about the purpose, types and examples of authentication protocols, which are computer communications protocols or cryptographic protocols for transfer of authentication data. compare different authentication protocols such as pap, chap, eap, aaa, kerberos and more.

Authentication Protocol Overview Oauth2 Saml Ldap Radius Kerberos What are authentication protocols? an authentication protocol allows the receiving party (such as a server) to verify the identity of another party (such as a person using a mobile device to log in). Learn about five common authentication protocols: ldap, kerberos, oauth2, saml, and radius. see how they work, their benefits, and how to choose the best one for your application needs. Authentication protocols are structured sets of rules that verify the identity of a user, device, or system before granting access. they function like a digital handshake—confirming credentials through cryptographic checks, challenge response mechanisms, or biometric validation. Authentication protocols are methods or procedures used to verify the identity of a user, device, or system. these protocols are designed to ensure that only authorized users or devices can access protected resources, preventing unauthorized access or tampering.
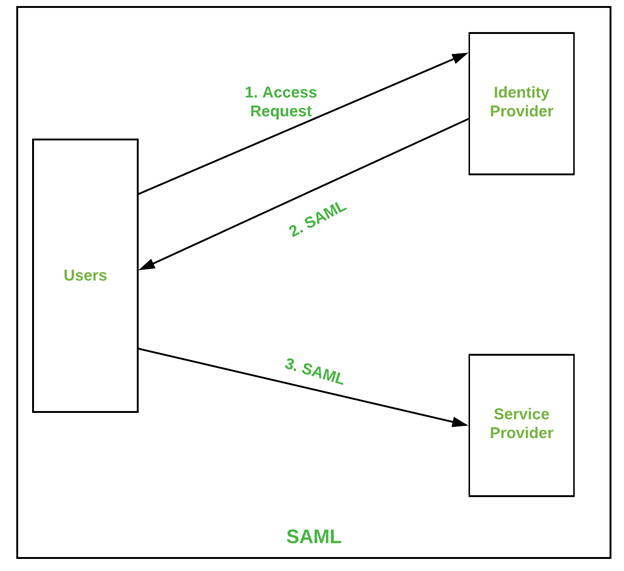
Authentication Protocols Perfmatrix Authentication protocols are structured sets of rules that verify the identity of a user, device, or system before granting access. they function like a digital handshake—confirming credentials through cryptographic checks, challenge response mechanisms, or biometric validation. Authentication protocols are methods or procedures used to verify the identity of a user, device, or system. these protocols are designed to ensure that only authorized users or devices can access protected resources, preventing unauthorized access or tampering. Authentication protocols are standardized procedures that govern the process of verifying the identity of entities (users, devices, or systems) before allowing them to access a particular resource or network. Authentication protocols are a set of rules and mechanisms that define how users, devices, or systems prove their identity before accessing resources. they’re essential and foundational if you want secure communication across networks, applications, and services. Authentication protocols are standardized methods that define how users, devices, or systems prove their identity before accessing a network, application, or online service. Establishing the right authentication protocol for your business is one way to achieve better security, but the process can be overwhelming. we’ll walk you through some common authentication protocols and how they work.
Authentication Protocol Overview Oauth2 Saml Ldap Radius Kerberos Authentication protocols are standardized procedures that govern the process of verifying the identity of entities (users, devices, or systems) before allowing them to access a particular resource or network. Authentication protocols are a set of rules and mechanisms that define how users, devices, or systems prove their identity before accessing resources. they’re essential and foundational if you want secure communication across networks, applications, and services. Authentication protocols are standardized methods that define how users, devices, or systems prove their identity before accessing a network, application, or online service. Establishing the right authentication protocol for your business is one way to achieve better security, but the process can be overwhelming. we’ll walk you through some common authentication protocols and how they work.

Authentication Protocol Overview Oauth2 Saml Ldap Radius Kerberos Authentication protocols are standardized methods that define how users, devices, or systems prove their identity before accessing a network, application, or online service. Establishing the right authentication protocol for your business is one way to achieve better security, but the process can be overwhelming. we’ll walk you through some common authentication protocols and how they work.

Authentication Protocols Types Examples And How They Work Oloid
Comments are closed.