Zphisher 2 2 Phishing Attack On Linkedin Thecyberdelta

New Linkedin Impersonated Phishing Attack Uses Bad Sign In Attempts To Practical. This hands on exploration with zphisher highlights the ease with which attackers can execute phishing campaigns and emphasizes the importance of cybersecurity awareness.

What Is A Phishing Attack And How To Prevent It Ssl Dragon In this video, we're going to demonstrate a real time phishing attack using zphisher, a popular tool for creating phishing links. the goal of this video is to raise cybersecurity. Zphisher is an advanced open source phishing tool for educational and penetration testing purposes. it provides a simple interface for launching phishing attacks by cloning login pages of popular websites. Zphisher is an open source phishing tool that can be used to retrieve personal information from unsuspecting individuals like their login credentials. the zphisher tool has templates for popular websites like gmail, instagram, snapchat, etc., and these templates are used to phish victims. Hey there, fellow security enthusiast! if you‘ve been exploring the cybersecurity landscape, you‘ve probably heard about phishing simulation tools. today, i‘m going to walk you through one of the most powerful yet user friendly options out there: zphisher.

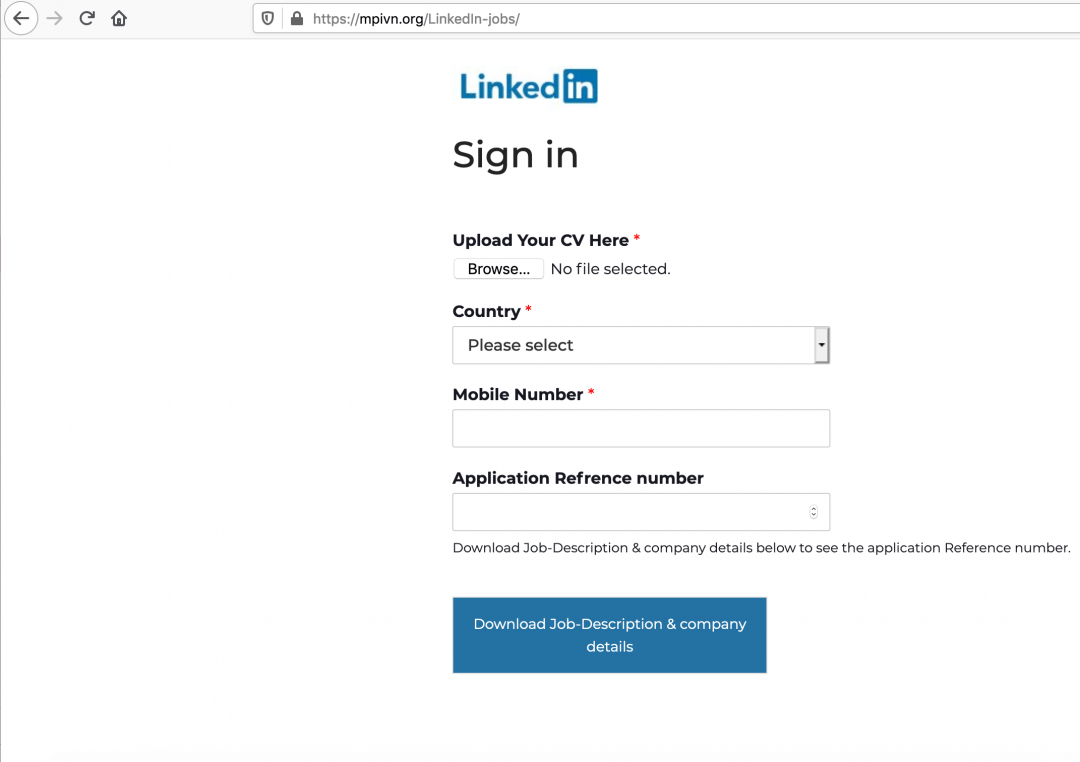
Phishing Linkedin Zphisher is an open source phishing tool that can be used to retrieve personal information from unsuspecting individuals like their login credentials. the zphisher tool has templates for popular websites like gmail, instagram, snapchat, etc., and these templates are used to phish victims. Hey there, fellow security enthusiast! if you‘ve been exploring the cybersecurity landscape, you‘ve probably heard about phishing simulation tools. today, i‘m going to walk you through one of the most powerful yet user friendly options out there: zphisher. Using the zphisher tool—an automated phishing framework from github—deployed within a vmware virtualized kali linux environment, this research simulates the creation of deceptive job application portals. Something went wrong while getting the release details. released version 2.1 new port forwarding option (cloudflared) added. Zphisher allows security professionals and penetration testers to demonstrate how phishing attacks work by creating realistic simulations of popular website login pages. Any actions and or activities related to zphisher is solely your responsibility. the misuse of this toolkit can result in criminal charges brought against the persons in question.

Intro To Phishing Simulating Attacks To Build Resiliency Cybernews Using the zphisher tool—an automated phishing framework from github—deployed within a vmware virtualized kali linux environment, this research simulates the creation of deceptive job application portals. Something went wrong while getting the release details. released version 2.1 new port forwarding option (cloudflared) added. Zphisher allows security professionals and penetration testers to demonstrate how phishing attacks work by creating realistic simulations of popular website login pages. Any actions and or activities related to zphisher is solely your responsibility. the misuse of this toolkit can result in criminal charges brought against the persons in question.
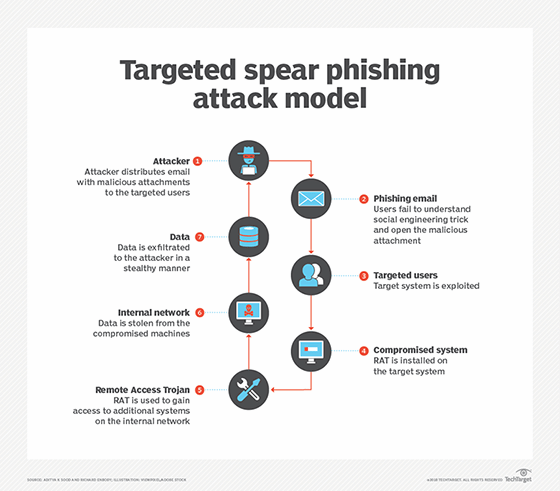
How To Avoid Linkedin Phishing Attacks In The Enterprise Techtarget Zphisher allows security professionals and penetration testers to demonstrate how phishing attacks work by creating realistic simulations of popular website login pages. Any actions and or activities related to zphisher is solely your responsibility. the misuse of this toolkit can result in criminal charges brought against the persons in question.
Linkedin Phishing Campaign Spread Agent Tesla Zscaler Blog
Comments are closed.