Zerotrust Identitysecurity Preventing Attacks Identity Defined

Identity Defined Security Alliance On Linkedin Identitysprawl The cybersecurity landscape of 2026 is defined by ai accelerated attacks, expanding hybrid infrastructures, and unprecedented regulatory pressure. these forces have made the zero trust model a best practice as well as an essential architecture for cyber resilience. organizations worldwide are prioritizing zero trust to reduce breach impact, secure identity driven ecosystems, and improve. Identities, representing people, services, or devices, are the common denominator across today’s many networks, endpoints, and applications. in the zero trust security model, they function as a powerful, flexible, and granular way to control access to data.

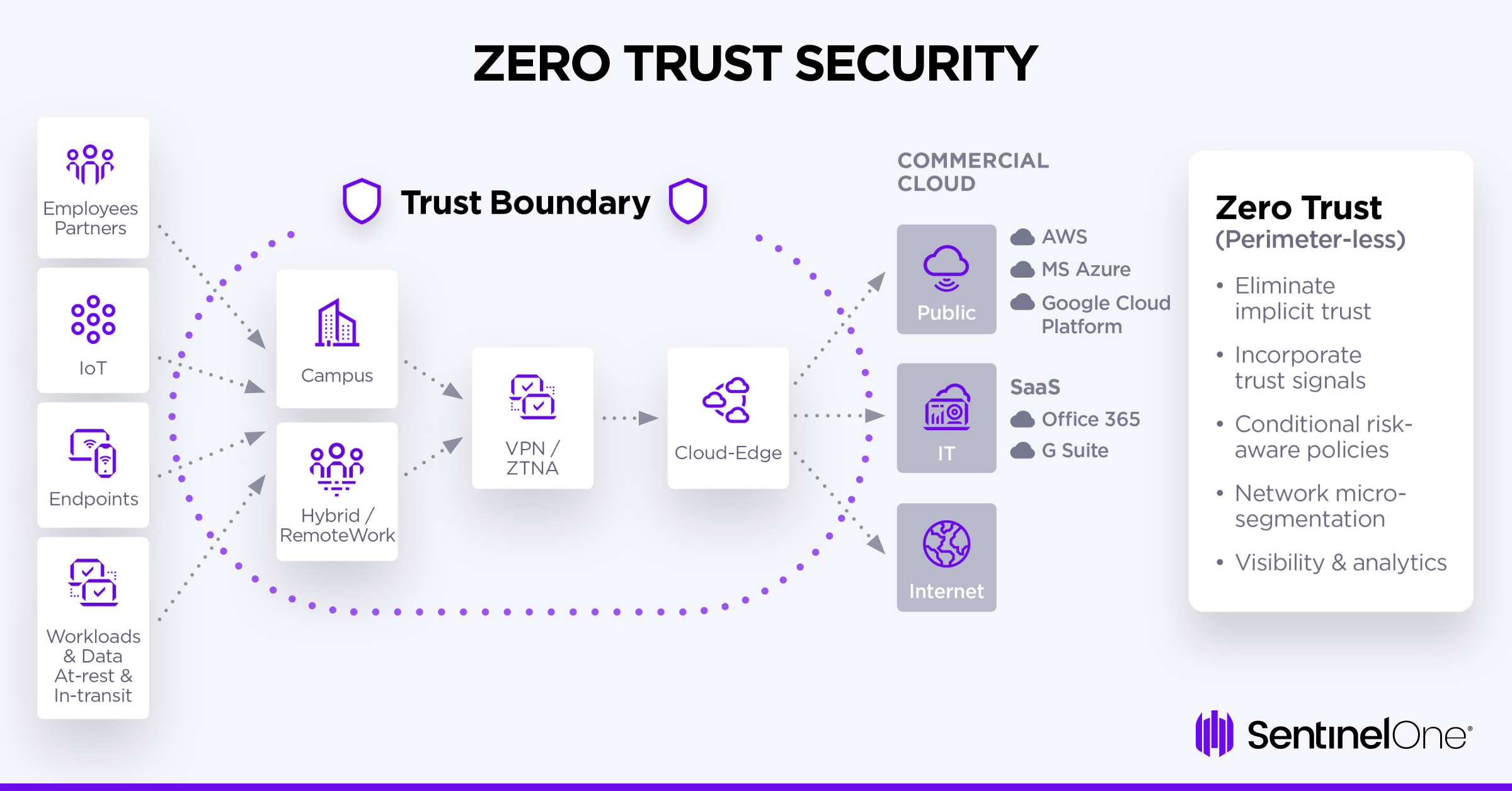
Identity Based Attacks Why Zero Trust Is The Future Of Cybersecurity More and more organizations are on the road to a zero trust security model, an architecture that treats all users as potential threats by preventing access until they’re properly authenticated. Learn how to protect your enterprise from identity based attacks by implementing iam fundamentals, zero trust, ai driven detection, and continuous monitoring. Zero trust is a strategic approach to cybersecurity that assumes all network traffic, both external and internal, may be hostile. this model enforces strict identity verification, limited. What is zero trust security? zero trust security is a security model that removes implicit trust from access decisions and treats identity as the anchor for policy decisions, working in concert with device, workload, data, and behavioral context.

Zerotrust Identitysecurity Preventing Attacks Identity Defined Zero trust is a strategic approach to cybersecurity that assumes all network traffic, both external and internal, may be hostile. this model enforces strict identity verification, limited. What is zero trust security? zero trust security is a security model that removes implicit trust from access decisions and treats identity as the anchor for policy decisions, working in concert with device, workload, data, and behavioral context. Zero trust identity is a security framework where every individual or device seeking access to a private network must go through identification and authorization checks, regardless of whether they are inside or outside the network. A zero trust framework is a security model that acts on the principle of "never trust, always verify," requiring strict identity confirmation for every human and device trying to access resources on a private network, regardless of their location. This paper explores the zero trust architecture (zta) as a contemporary cybersecurity framework that addresses the challenges posed by increasingly interconnected systems. In this post, we’ll review what zero trust is, explain the types of identities that are at the heart of it, and review the steps and best practices for building an effective zero trust identity strategy.

Implementing Zero Trust Identity Strategies And Benefits Zero trust identity is a security framework where every individual or device seeking access to a private network must go through identification and authorization checks, regardless of whether they are inside or outside the network. A zero trust framework is a security model that acts on the principle of "never trust, always verify," requiring strict identity confirmation for every human and device trying to access resources on a private network, regardless of their location. This paper explores the zero trust architecture (zta) as a contemporary cybersecurity framework that addresses the challenges posed by increasingly interconnected systems. In this post, we’ll review what zero trust is, explain the types of identities that are at the heart of it, and review the steps and best practices for building an effective zero trust identity strategy.
What Is Identity Security This paper explores the zero trust architecture (zta) as a contemporary cybersecurity framework that addresses the challenges posed by increasingly interconnected systems. In this post, we’ll review what zero trust is, explain the types of identities that are at the heart of it, and review the steps and best practices for building an effective zero trust identity strategy.
Comments are closed.