Why Quantum Computing Will Change Cybersecurity Forever Techy
Why Quantum Computing Will Change Cybersecurity Forever Techy We are living in a time of rapid tech breakthroughs — but few are as fascinating and game changing as quantum computing. it’s not just a flashy term; indeed a real shift in how we solve problems that today’s computers can’t handle. Sometime around 2035 quantum computers are expected to become sufficiently powerful to compromise current widely used cryptographic standards, the foundation for online security. fortunately, there is a clear path for the transition to post quantum cryptography.

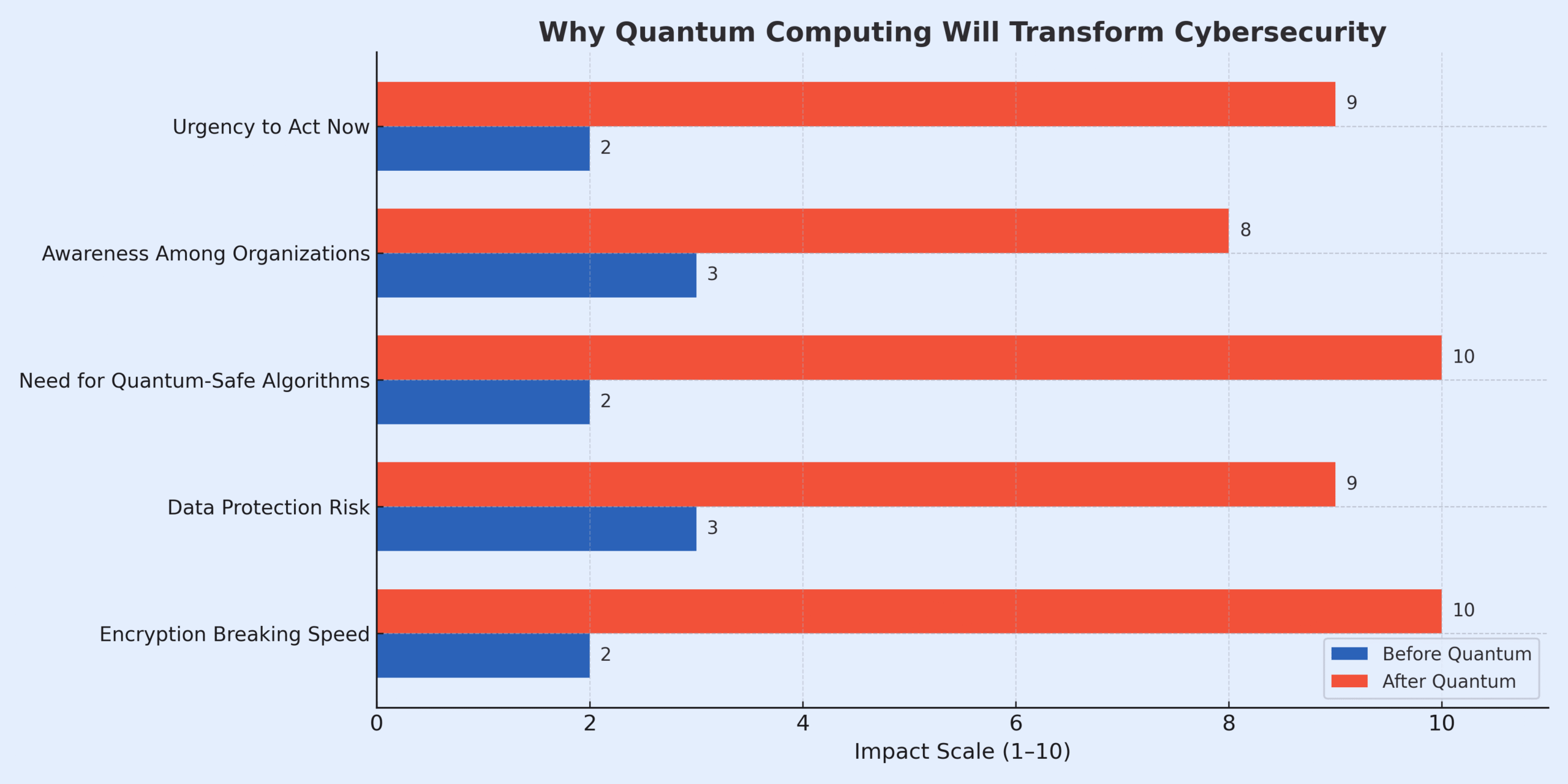
How Quantum Computing Could Change Cybersecurity Forever This systematic review examines the transformative impact of quantum computing (qc) on cybersecurity by analysing peer reviewed literature published between 2019 and 2024. Quantum computing's impact on cybersecurity is a game changer, but not necessarily for the better. as quantum computers become increasingly powerful, they'll break even the most secure encryption algorithms currently in use, compromising public key cryptography and data protection. As cyber threats evolve, the use of quantum key distribution (qkd), quantum random number generators (qrngs), and post quantum cryptography (pqc) can protect data from both classical and quantum computing attacks. This review paper comprehensively examines the transformative impact of quantum computing on cybersecurity, highlighting vulnerabilities introduced by algorithms like shor’s and grover’s, which can break widely used encryption methods such as rsa, ecc, and aes.

How Quantum Computing Could Change Cybersecurity Forever As cyber threats evolve, the use of quantum key distribution (qkd), quantum random number generators (qrngs), and post quantum cryptography (pqc) can protect data from both classical and quantum computing attacks. This review paper comprehensively examines the transformative impact of quantum computing on cybersecurity, highlighting vulnerabilities introduced by algorithms like shor’s and grover’s, which can break widely used encryption methods such as rsa, ecc, and aes. As this technology advances, understanding its impact on cybersecurity is crucial for businesses and governments alike. here are five reasons why quantum computing will change. Quantum computing isn’t just a weapon for attackers—it also offers defenders powerful new tools. one key area is quantum enhanced optimization and machine learning. This article will explore how quantum computing will impact cybersecurity, why current encryption methods will no longer be secure, and how quantum technology can introduce new opportunities. Although state of the art computer security heavily relies on cryptography, it can indeed transcend beyond encryption. this paper analyzes an encryption agnostic approach that can potentially render computers quantum resistant.

How Quantum Computing Could Change Cybersecurity Forever As this technology advances, understanding its impact on cybersecurity is crucial for businesses and governments alike. here are five reasons why quantum computing will change. Quantum computing isn’t just a weapon for attackers—it also offers defenders powerful new tools. one key area is quantum enhanced optimization and machine learning. This article will explore how quantum computing will impact cybersecurity, why current encryption methods will no longer be secure, and how quantum technology can introduce new opportunities. Although state of the art computer security heavily relies on cryptography, it can indeed transcend beyond encryption. this paper analyzes an encryption agnostic approach that can potentially render computers quantum resistant.
Comments are closed.