Why Does Rsa Work
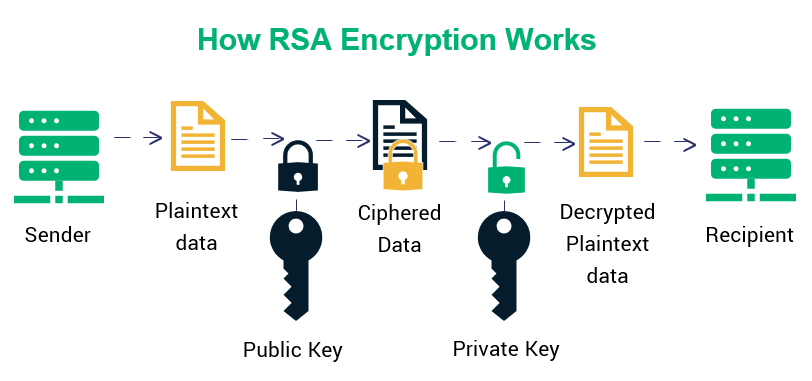
Rsa Cryptosystem The rsa algorithm involves four steps: key generation, key distribution, public key operation (used for encryption or verifying a signature), and private key operation (used for decryption or signing a message). Digital signatures: rsa algorithm can be used for digital signatures, which means that a sender can sign a message using their private key, and the receiver can verify the signature using the sender's public key.

Why Choose Rsa Rsa Learn what rsa encryption is, how it works with public and private keys, and why it's still crucial for securing websites and digital communications. Rsa encryption may sound complex at first glance, but its underlying mechanisms are actually quite straightforward once broken down. this extensive guide aims to make rsa fully accessible to readers of all technical levels – no advanced math or cryptography expertise required!. With rsa, either the private or public key can encrypt the data, while the other key decrypts it. this is one of the reasons rsa is the most used asymmetric encryption algorithm. Rsa encryption, type of public key cryptography widely used for data encryption of e mail and other digital transactions over the internet. a user secretly chooses a pair of prime numbers p and q so large that factoring their product is well beyond projected computing capabilities.

Why Choose Rsa Rsa With rsa, either the private or public key can encrypt the data, while the other key decrypts it. this is one of the reasons rsa is the most used asymmetric encryption algorithm. Rsa encryption, type of public key cryptography widely used for data encryption of e mail and other digital transactions over the internet. a user secretly chooses a pair of prime numbers p and q so large that factoring their product is well beyond projected computing capabilities. Rsa encryption is one of the most widespread encryption techniques in the world, used to ensure the security of digital communications. thanks to its public and private key system, it allows for the protection of sensitive information and reliable user authentication. This article describes rsa algorithm, how it works, and its major applications in cryptography. it also explains the vulnerabilities of rsa. Discover how rsa works, the key algorithm for encrypting data and digital signatures. learn how to use and apply it. Rsa allows you to secure messages before you send them. and the technique also lets you certify your notes, so recipients know they haven't been adjusted or altered while in transit. the rsa algorithm is one of the most widely used encryption tools in use today.
Comments are closed.