What Really Happens To Your Data After A Breach

What Happens After A Data Breach Itfirm Com After a data breach, your stolen data gets sold, traded, and exploited in ways most people never think about. learn the full lifecycle of stolen information and how to protect yourself. Data breaches appear frequently in the news, but the immediate aftermath is often misunderstood. beyond the public statements and emails of apology are the concerted efforts of digital.

What Happens After A Data Breach A Timeline Dataleaks Us Articles Where does your data go after a breach? once your data is compromised in a breach, it turns into a commodity—something to be bought, sold, or traded. it might be sold on its own, but. This guide covers the six steps your company should take right after a breach. for building a response plan before a breach happens, see our data breach response plan guide. In this blog we’ll look at what happens to personal data after a breach, the value of stolen data, and ways that you can protect your personal information and take back control. Whether you’ve been involved in a data breach or want to proactively protect yourself from potential disaster, read on for steps you can take to regain control of your accounts and protect.
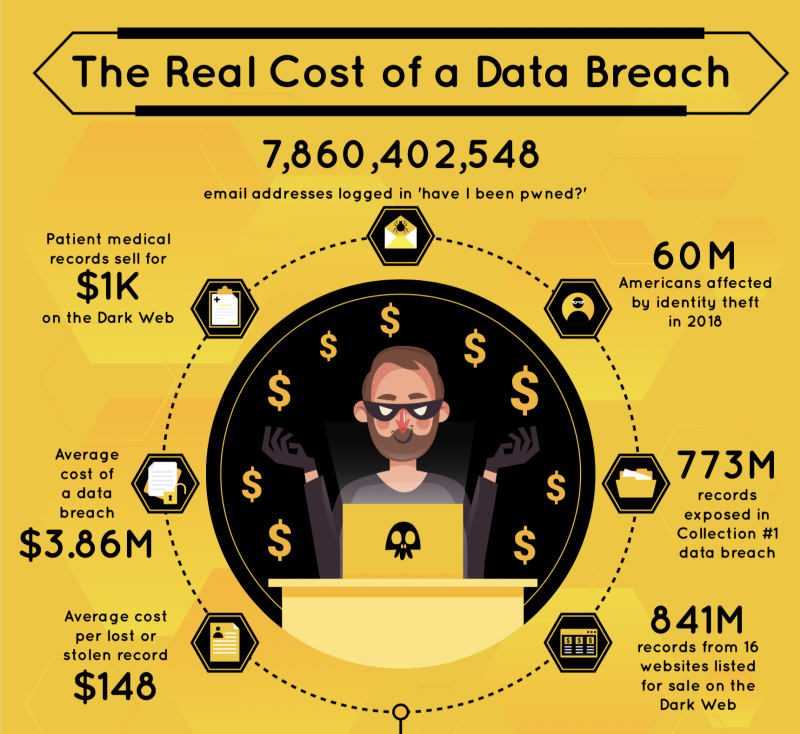
After The Data Breach What Happens To Your Data Blackfog In this blog we’ll look at what happens to personal data after a breach, the value of stolen data, and ways that you can protect your personal information and take back control. Whether you’ve been involved in a data breach or want to proactively protect yourself from potential disaster, read on for steps you can take to regain control of your accounts and protect. Here’s a no nonsense guide to understanding and navigating every type of data breach. If you are a victim of a data breach, you can suffer a wide range of consequences depending on the exact data leaked, as well as the measures taken to protect yourself. What really happens after a breach? we walk through what happens minute by minute, hour by hour, day by day, from the moment of discovery through the end of the third day. In this guide, i’ll walk you through what happens to stolen data after a breach, how underground markets really operate, why hackers bundle and resell leaked credentials, and what you can do—right now—to lower your risk.

After The Data Breach What Happens To Your Data Blackfog Here’s a no nonsense guide to understanding and navigating every type of data breach. If you are a victim of a data breach, you can suffer a wide range of consequences depending on the exact data leaked, as well as the measures taken to protect yourself. What really happens after a breach? we walk through what happens minute by minute, hour by hour, day by day, from the moment of discovery through the end of the third day. In this guide, i’ll walk you through what happens to stolen data after a breach, how underground markets really operate, why hackers bundle and resell leaked credentials, and what you can do—right now—to lower your risk.

After The Data Breach What Happens To Your Data Blackfog What really happens after a breach? we walk through what happens minute by minute, hour by hour, day by day, from the moment of discovery through the end of the third day. In this guide, i’ll walk you through what happens to stolen data after a breach, how underground markets really operate, why hackers bundle and resell leaked credentials, and what you can do—right now—to lower your risk.
Comments are closed.