What Is Vulnerability Scanning About
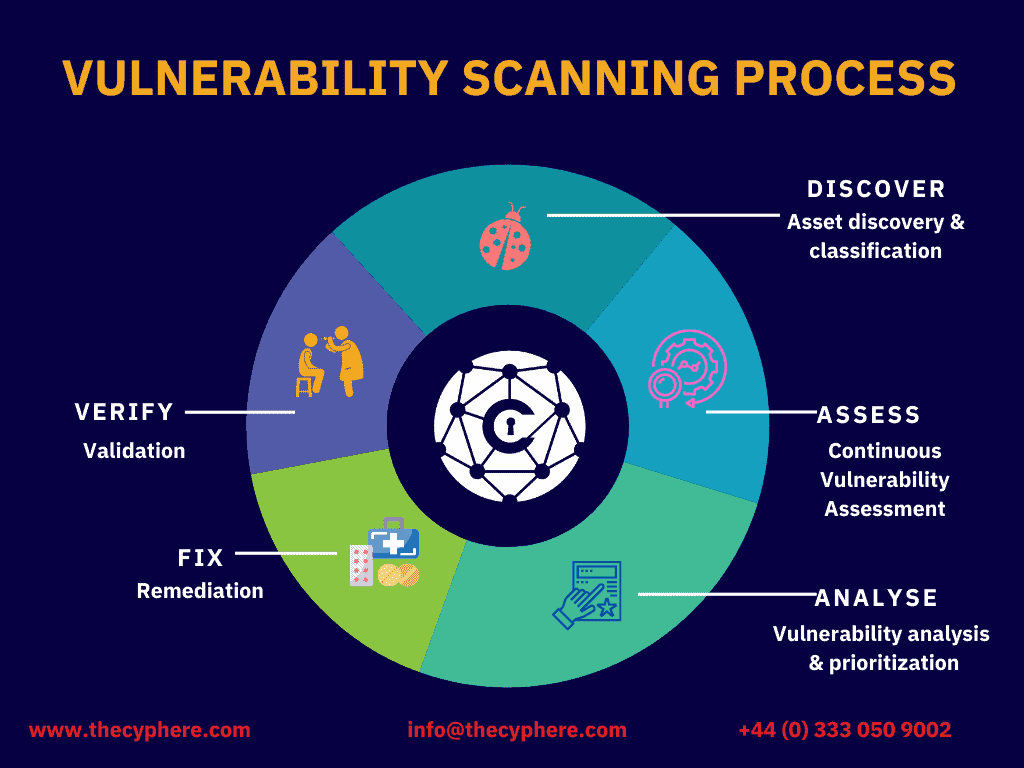
What Is Vulnerability Scanning And How Does It Work Vulnerability scanning, also called “vulnerability assessment,” is the process of evaluating networks or it assets for security vulnerabilities, flaws or weaknesses that external or internal threat actors can exploit. Vulnerability scanning is the systematic process of automatically identifying security weaknesses, misconfigurations, and known vulnerabilities in systems, networks, applications, and devices.

Vulnerability Scanning Webcheck Security Vulnerability scanning is an automated process to identify security flaws in networks, systems and applications, enabling remediation and enhancing security posture. What is vulnerability scanning? vulnerability scanning identifies weaknesses across systems, applications, and networks to help organizations reduce exposure and stay ahead of threats. Vulnerability scanning is the process of discovering, analysing, and reporting security flaws and vulnerabilities. alongside vulnerability assessment, vulnerability scanning is an essential step in the vulnerability management lifecycle. Detecting and mitigating vulnerabilities in different systems, applications, or network devices is done step by step through vulnerability scanning, one of the security scan domains.

Vulnerability Scanning Sysgroup Vulnerability scanning is the process of discovering, analysing, and reporting security flaws and vulnerabilities. alongside vulnerability assessment, vulnerability scanning is an essential step in the vulnerability management lifecycle. Detecting and mitigating vulnerabilities in different systems, applications, or network devices is done step by step through vulnerability scanning, one of the security scan domains. Vulnerability scanning is the process of scanning it networks to identify and assess security flaws and vulnerabilities in the network, systems, and applications, and mitigate them before threat actors can exploit them. What is vulnerability scanning? vulnerability scanning is an automated, repeatable process that inspects systems, containers, code dependencies, configurations, and cloud resources to detect known vulnerabilities, misconfigurations, or missing updates. Vulnerability scanning is a crucial process within any comprehensive cybersecurity program. it involves the automated detection of security weaknesses in software, systems, and networks, allowing organizations to identify and address potential threats before attackers can exploit them. Vulnerability scanning is an automated security process that systematically evaluates it assets, including networks and software applications, to identify weaknesses and flaws before they can be exploited.

Vulnerability Scanning Pennyrile Technologies Vulnerability scanning is the process of scanning it networks to identify and assess security flaws and vulnerabilities in the network, systems, and applications, and mitigate them before threat actors can exploit them. What is vulnerability scanning? vulnerability scanning is an automated, repeatable process that inspects systems, containers, code dependencies, configurations, and cloud resources to detect known vulnerabilities, misconfigurations, or missing updates. Vulnerability scanning is a crucial process within any comprehensive cybersecurity program. it involves the automated detection of security weaknesses in software, systems, and networks, allowing organizations to identify and address potential threats before attackers can exploit them. Vulnerability scanning is an automated security process that systematically evaluates it assets, including networks and software applications, to identify weaknesses and flaws before they can be exploited.

Vulnerability Scanning Unity Metrix Vulnerability scanning is a crucial process within any comprehensive cybersecurity program. it involves the automated detection of security weaknesses in software, systems, and networks, allowing organizations to identify and address potential threats before attackers can exploit them. Vulnerability scanning is an automated security process that systematically evaluates it assets, including networks and software applications, to identify weaknesses and flaws before they can be exploited.
Managed Vulnerability Scanning Cyphere
Comments are closed.