Vulnerability Scanning Sysgroup

What Is Vulnerability Scanning How It Works Types Benefits Tenable’s vulnerability management & cyber exposure platform, delivered by sysgroup, provides full visibility into your security posture by identifying, managing, and mitigating vulnerabilities across your on premises, cloud, and operational technology (ot) environments. How to turn risk into resilience with sysgroup's vulnerability management solutions.
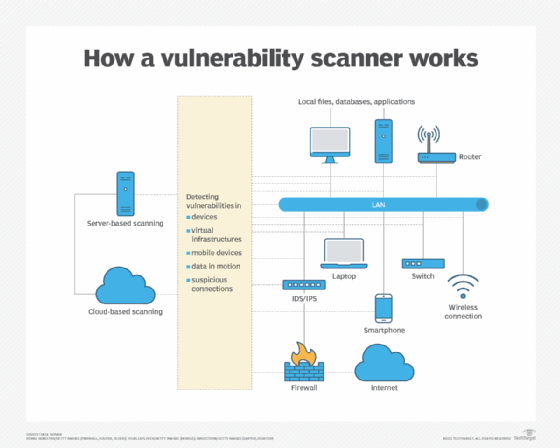
Types Of Vulnerability Scanning And When To Use Each Techtarget Vulnerability scanning tools description web application vulnerability scanners are automated tools that scan web applications, normally from the outside, to look for security vulnerabilities such as cross site scripting, sql injection, command injection, path traversal and insecure server configuration. Unauthorized hackers may exploit these flaws to obtain access to the system and abuse it in their ways. detecting and mitigating vulnerabilities in different systems, applications, or network devices is done step by step through vulnerability scanning, one of the security scan domains. Learn what vulnerability scanning is, how it works, the main types, tools, internal vs external approaches, cloud and ci cd support, best practices, challenges, and faqs to strengthen your security posture and reduce cyber risk. Learn what vulnerability scanning is, why it matters, how it works, types, benefits, challenges, and best practices with faq and compliance tips.
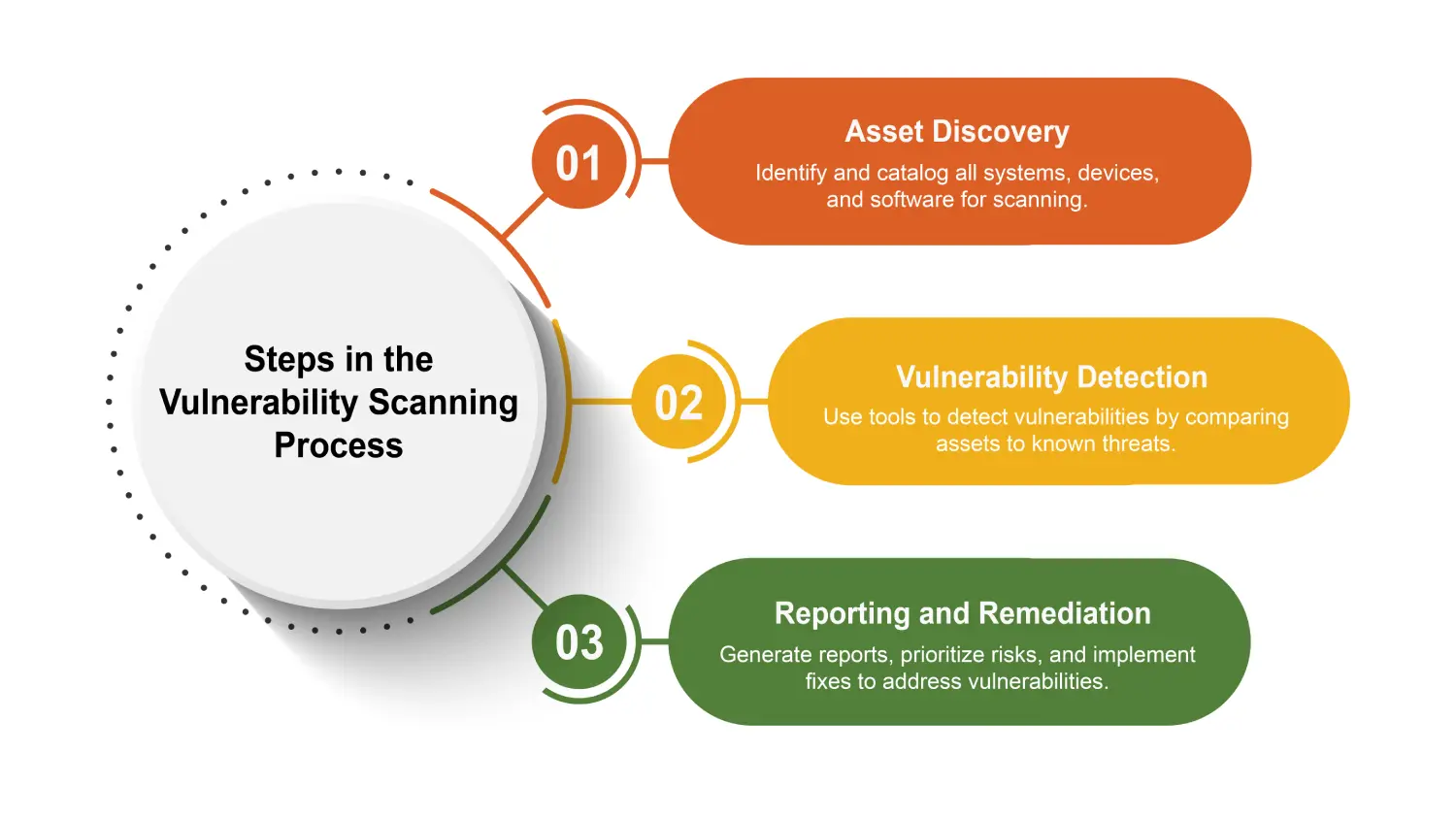
What Is Vulnerability Scanning Essential Insights And Best Practices Learn what vulnerability scanning is, how it works, the main types, tools, internal vs external approaches, cloud and ci cd support, best practices, challenges, and faqs to strengthen your security posture and reduce cyber risk. Learn what vulnerability scanning is, why it matters, how it works, types, benefits, challenges, and best practices with faq and compliance tips. Protect your business from cyber threats with managed vulnerability management. prioritise real risks, meet compliance requirements, and get live dashboards in 30 days. Vulnerability scanning uses automated tools to identify known software vulnerabilities in an organization’s environment. Vulnerability scanning is the process of discovering, analysing, and reporting security flaws and vulnerabilities. alongside vulnerability assessment, vulnerability scanning is an essential step in the vulnerability management lifecycle. Discover what vulnerability scanning is, types, tools, and best practices to enhance your security posture and protect your systems.

Automated Vulnerability Scanning To Map Compliance Frameworks Protect your business from cyber threats with managed vulnerability management. prioritise real risks, meet compliance requirements, and get live dashboards in 30 days. Vulnerability scanning uses automated tools to identify known software vulnerabilities in an organization’s environment. Vulnerability scanning is the process of discovering, analysing, and reporting security flaws and vulnerabilities. alongside vulnerability assessment, vulnerability scanning is an essential step in the vulnerability management lifecycle. Discover what vulnerability scanning is, types, tools, and best practices to enhance your security posture and protect your systems.

How To Scan For Vulnerabilities At John Heidt Blog Vulnerability scanning is the process of discovering, analysing, and reporting security flaws and vulnerabilities. alongside vulnerability assessment, vulnerability scanning is an essential step in the vulnerability management lifecycle. Discover what vulnerability scanning is, types, tools, and best practices to enhance your security posture and protect your systems.
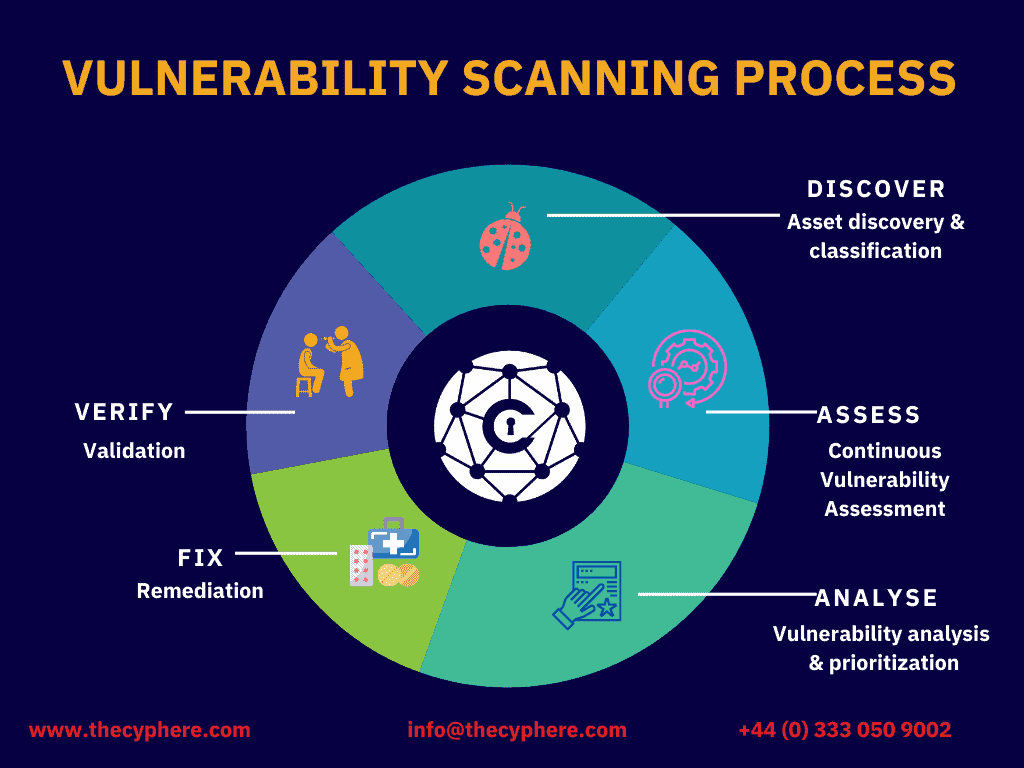
Managed Vulnerability Scanning Cyphere
Comments are closed.