What Is Cip Security

Cpwe Cip Security Pdf Transport Layer Security Computer Network Cip security™ encompasses security related requirements and capabilities for cip™ devices, specifically ethernet ip™ devices. a defense in depth security architecture is an important part of control system security. Common industrial protocol (cip™) security is an open standard secure communication protocol developed by odva for ethernet ip™ communications, providing the final layer of defense against malicious communication attacks commonly carried out over large organizational networks.

Cip Overview Pdf Security Computer Security Cip security is the secure extension of cip over the well known standard transport layer security (tls). the concept is like hypertext transfer protocol (http) over tls, also known as https. it uses proven standard technology to minimize potential vulnerabilities that may impact iacs applications. Cip security™ enabled devices can play an important part in a defense in depth strategy. watch this overview showing how cip security works to make products and systems more secure. What is the cip security specification? the cip security specification defines a set of well defined processes, mechanisms, and behaviors that use off the shelf technology to secure ethernet ip networks from the threats described by the stride model. Cip security is a software architecture designed to protect cip technology networks (ethernet ip ™, devicenet ®, componet®, controlnet®) in this sort of hostile environment.

What Is Cip Security What is the cip security specification? the cip security specification defines a set of well defined processes, mechanisms, and behaviors that use off the shelf technology to secure ethernet ip networks from the threats described by the stride model. Cip security is a software architecture designed to protect cip technology networks (ethernet ip ™, devicenet ®, componet®, controlnet®) in this sort of hostile environment. The standards, cip 002 through cip 013 think of each cip standard as a chapter in a comprehensive security handbook. cip 002 starts with identifying critical assets. cip 013 closes things out with supply chain risk management. each chapter builds on the last, creating a layered security posture rather than a checklist you knock out once and forget. Our course covers all aspects of nerc cip, from the fundamentals to advanced topics, including bes cyber asset identification, cip specific cybersecurity approaches, physical security, incident and recovery planning, as well as regulatory perspectives and what to expect in your audit. This course will provide an understanding of supply chain security risks relevant in the electric sector and mitigation strategies. the cip supply chain standards will be covered in detail as well as presidential executive orders, nerc supply chain risk mitigation program documents, and more. Cip security’s ability to authenticate via the device or through a central server allows for simplicity in smaller, simple systems and efficiency in large, complicated installations.
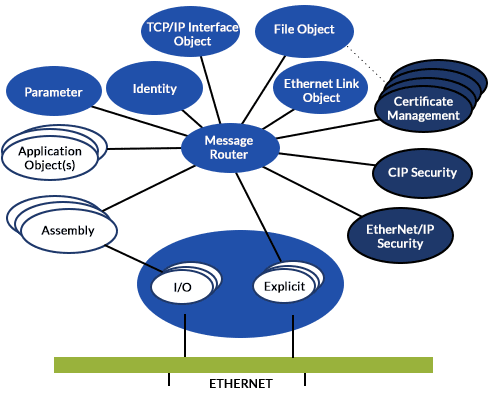
Cip Security Tech Step Integration The standards, cip 002 through cip 013 think of each cip standard as a chapter in a comprehensive security handbook. cip 002 starts with identifying critical assets. cip 013 closes things out with supply chain risk management. each chapter builds on the last, creating a layered security posture rather than a checklist you knock out once and forget. Our course covers all aspects of nerc cip, from the fundamentals to advanced topics, including bes cyber asset identification, cip specific cybersecurity approaches, physical security, incident and recovery planning, as well as regulatory perspectives and what to expect in your audit. This course will provide an understanding of supply chain security risks relevant in the electric sector and mitigation strategies. the cip supply chain standards will be covered in detail as well as presidential executive orders, nerc supply chain risk mitigation program documents, and more. Cip security’s ability to authenticate via the device or through a central server allows for simplicity in smaller, simple systems and efficiency in large, complicated installations.

Understanding Cip Security Rockwell Automation This course will provide an understanding of supply chain security risks relevant in the electric sector and mitigation strategies. the cip supply chain standards will be covered in detail as well as presidential executive orders, nerc supply chain risk mitigation program documents, and more. Cip security’s ability to authenticate via the device or through a central server allows for simplicity in smaller, simple systems and efficiency in large, complicated installations.

Advanced Cip Training Bundle Opswat Academy
Comments are closed.