What Is Ai Cloud Security Definition Benefits Challenges

Cloud Ai Security The Biggest Challenges For Businesses And Operations Learn how ai cloud security enhances threat detection, automates defense, and safeguards sensitive data across cloud infrastructures. Explore how ai cloud security transforms cloud environments with enhanced capabilities and understand best practices to secure ai in the cloud.

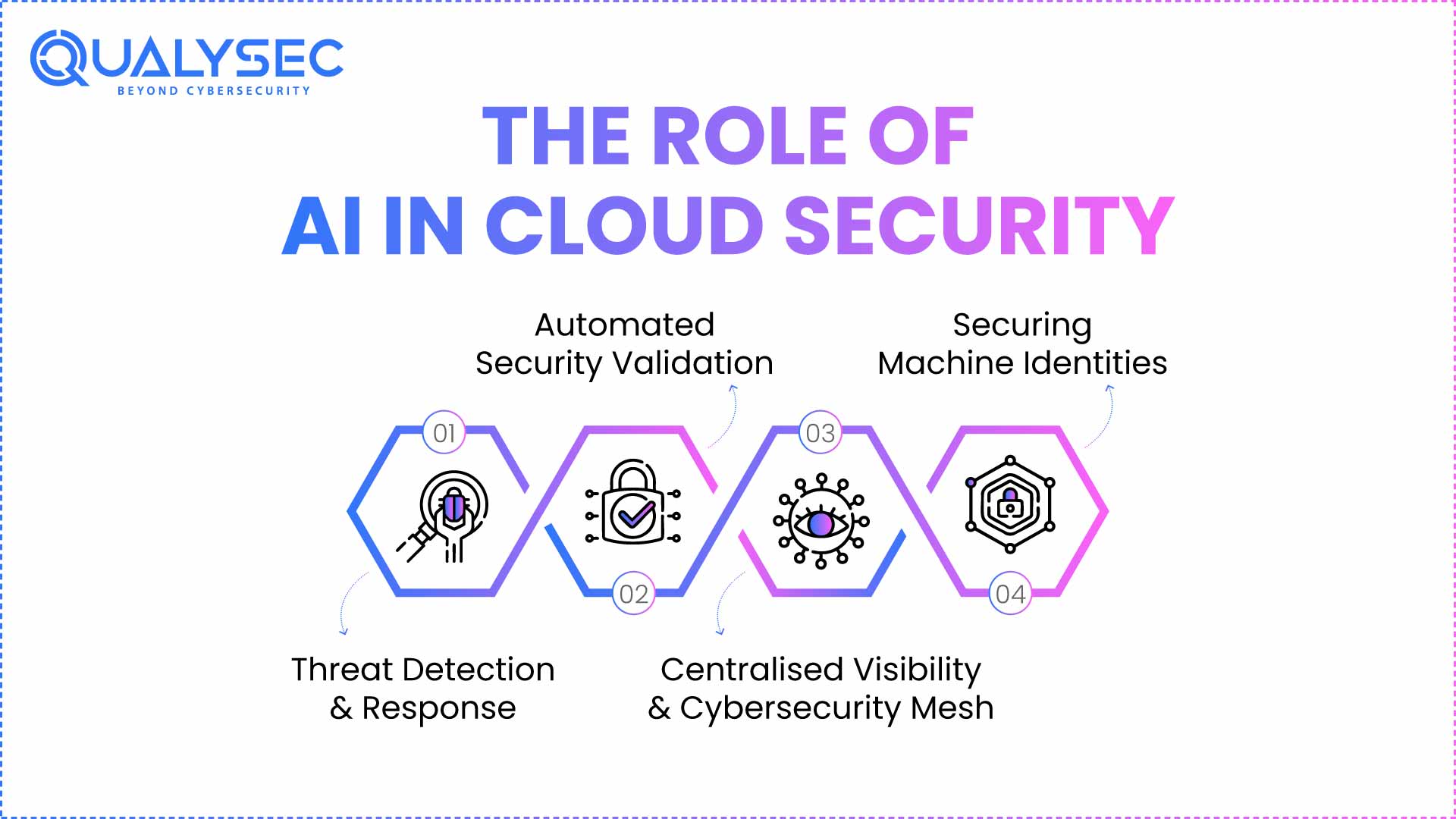
Ai Workloads Driving New Cloud Security Challenges Cyber Risk Leaders Discover how ai is transforming cloud security, from automated threat detection to real time response, aiding protection and operational efficiency. This article explores how ai is integrated into cloud security, discussing key use cases such as threat detection, anomaly detection, automated response, and identity management. In the end, what’s needed is cloud security that leverages the best of ai while providing robust encryption and continuous monitoring. in this article, we’ll examine how ai technology impacts multiple areas of cloud security. Ai security refers to the strategic process of leveraging artificial intelligence to strengthen an organization's security infrastructure. this approach enables the automation of threat detection, prevention, and remediation workflows, allowing for more effective combat of sophisticated cyberattacks and data breaches.

Government Ai Cloud Security In the end, what’s needed is cloud security that leverages the best of ai while providing robust encryption and continuous monitoring. in this article, we’ll examine how ai technology impacts multiple areas of cloud security. Ai security refers to the strategic process of leveraging artificial intelligence to strengthen an organization's security infrastructure. this approach enables the automation of threat detection, prevention, and remediation workflows, allowing for more effective combat of sophisticated cyberattacks and data breaches. Learn about cloud computing security threats, the benefits of ai in cloud security, cloud security examples with and without ai, and get a glossary of terms. Learn how ai solves cloud security challenges, get examples of using ai in cloud security vs traditional methods, and learn how to protect ai in the cloud. This guide explains what is ai security in practice, why the threat environment has changed significantly in 2025 and 2026, the specific security risks enterprises face today, and what effective protection actually looks like when ai moves from experiment to production infrastructure. This article explores how ai is transforming cloud security from the ground up: the new threat landscape it’s responding to, the capabilities it brings to defenders, and the practical steps organizations need to take to stay protected.
What Is Ai Cloud Security Definition Benefits Challenges Learn about cloud computing security threats, the benefits of ai in cloud security, cloud security examples with and without ai, and get a glossary of terms. Learn how ai solves cloud security challenges, get examples of using ai in cloud security vs traditional methods, and learn how to protect ai in the cloud. This guide explains what is ai security in practice, why the threat environment has changed significantly in 2025 and 2026, the specific security risks enterprises face today, and what effective protection actually looks like when ai moves from experiment to production infrastructure. This article explores how ai is transforming cloud security from the ground up: the new threat landscape it’s responding to, the capabilities it brings to defenders, and the practical steps organizations need to take to stay protected.
Comments are closed.