What Is A Zero Day Exploit Cybersecurity Vulnerabilities Explained
What Is A Zero Day Exploit Cybersecurity Vulnerabilities Explained Zero day exploits exploit a precise, unpatched security weakness in a system or product. attackers often conduct rigorous reconnaissance, scouring software, firmware, and hardware for overlooked bugs or architectural weaknesses that can be exploited. Learn what a zero day exploit is, why it poses such a severe risk, and how organizations can detect and mitigate zero day attacks using proactive threat intelligence.
Zero Day Vulnerabilities Explained Appcheck Zero day exploit refers to a security vulnerability that is unknown to the software vendor or the public, allowing attackers to exploit it before it can be patched. A zero day exploit is a cyberattack vector or technique that takes advantage of an unknown or unaddressed security flaw in computer software, hardware or firmware. A zero day exploit is a cyber vulnerability unknown to those needing to fix it, including product vendors. it represents a risk as developers have no time to patch it once exposed, leaving systems open to stealthy malicious activities until a solution is found. A zero day vulnerability is a software flaw that is unknown to the vendor, or is known but does not yet have a patch available to defenders. attackers can exploit it before reliable fixes.

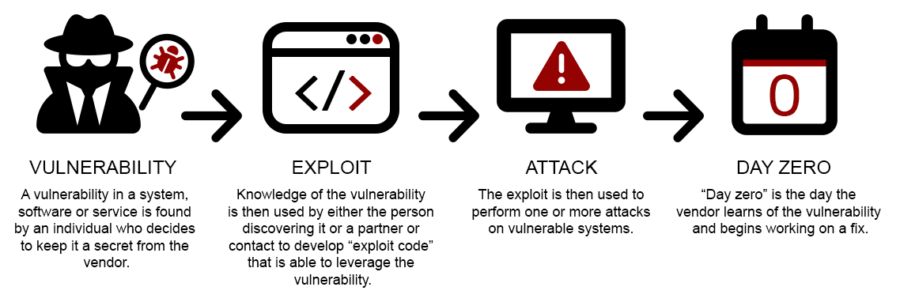
What Is A Zero Day 0day Exploit Attacks Vulnerabilities Explained A zero day exploit is a cyber vulnerability unknown to those needing to fix it, including product vendors. it represents a risk as developers have no time to patch it once exposed, leaving systems open to stealthy malicious activities until a solution is found. A zero day vulnerability is a software flaw that is unknown to the vendor, or is known but does not yet have a patch available to defenders. attackers can exploit it before reliable fixes. This guide explains what zero day vulnerabilities are, how they are discovered and leveraged, and what proactive steps your organization can take to mitigate the associated risks. Zero day exploit: once attackers identify a zero day vulnerability, they develop a method or technique, known as an exploit, to exploit it. these exploits can be malicious code, phishing emails, or other tactics to bypass security measures and gain unauthorized system access. A zero day attack occurs when a cybercriminal exploits a zero day vulnerability. they do this by taking advantage of the security flaw before the vendor releases a patch or fix for it, often through tactics such as launching malware attacks. It refers to the code or method the attacker deploys to exploit the zero day vulnerability for malicious purposes. these tightened attacks aim directly at the particular flaw the corresponding software provider has not yet fixed or mitigated.
What Is A Zero Day 0day Exploit Attacks Vulnerabilities Explained This guide explains what zero day vulnerabilities are, how they are discovered and leveraged, and what proactive steps your organization can take to mitigate the associated risks. Zero day exploit: once attackers identify a zero day vulnerability, they develop a method or technique, known as an exploit, to exploit it. these exploits can be malicious code, phishing emails, or other tactics to bypass security measures and gain unauthorized system access. A zero day attack occurs when a cybercriminal exploits a zero day vulnerability. they do this by taking advantage of the security flaw before the vendor releases a patch or fix for it, often through tactics such as launching malware attacks. It refers to the code or method the attacker deploys to exploit the zero day vulnerability for malicious purposes. these tightened attacks aim directly at the particular flaw the corresponding software provider has not yet fixed or mitigated.
Comments are closed.