What Are Three Secrets About Tetra Radios That Virtually No One Knows About

Tetra Radios In Dubai Uae Mechgen Technologies We talked about who was behind the decision to keep the algorithms secret, why they weakened one of the cryptographic keys, and why the group plans to keep the new algorithms it created secret as well. Although not all tetra radio users are using tea1, those who do are likely at risk of having their communications intercepted and decrypted. tea1 is primarily intended for commercial users. the.

Tetra Radios In Dubai Uae Mechgen Technologies Security researchers jos wetzels, carlo meijer, and wouter bokslag shared their research on tetra technology by reverse engineering motorola mbts and mtm5400 radios and extracting the secrets from them. tetra is a radio technology patented in 1995 and based on proprietary cryptography. The standard has been used in radios since the ’90s, but the flaws remained unknown because encryption algorithms used in tetra were kept secret until now. Ewa włodarzyc from airbus reveals three secrets about tetra radios. she also reveals one brilliant way to use a special tetra radio accessory. intelligence shared. To provide confidentiality the tetra air interface is encrypted using one of the tetra encryption algorithm (tea) ciphers. the encryption provides confidentiality (protect against eavesdropping) as well as protection of signalling.
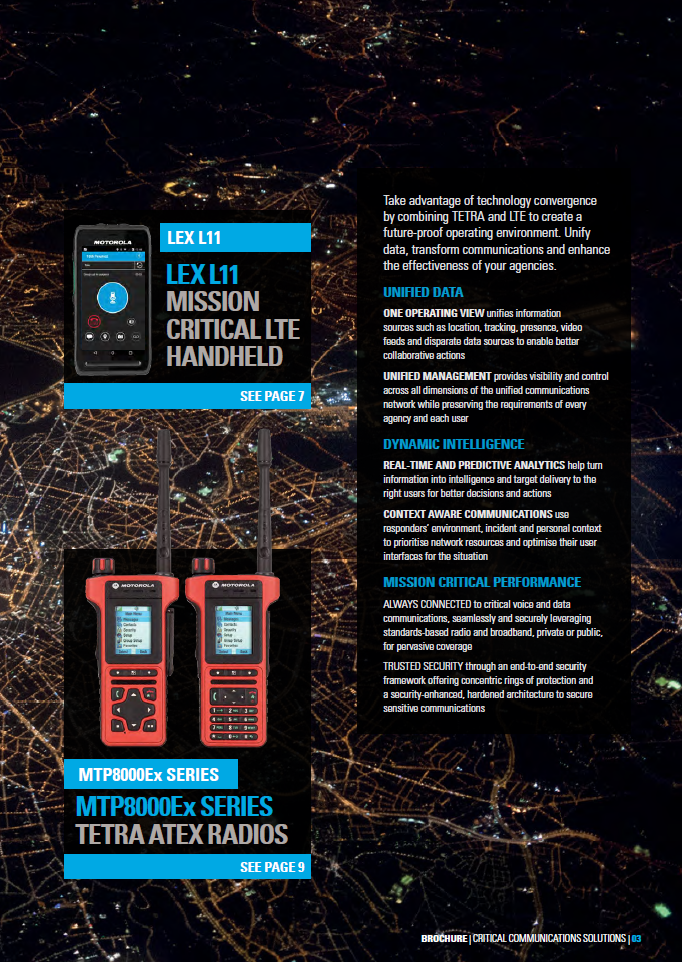
Tetra Radios In Dubai Uae Mechgen Technologies Ewa włodarzyc from airbus reveals three secrets about tetra radios. she also reveals one brilliant way to use a special tetra radio accessory. intelligence shared. To provide confidentiality the tetra air interface is encrypted using one of the tetra encryption algorithm (tea) ciphers. the encryption provides confidentiality (protect against eavesdropping) as well as protection of signalling. Three dutch security analysts discovered five vulnerabilities in a european radio standard called tetra (terrestrial trunked radio), which is used in radios made by motorola, damm, hytera, and others. Here’s the story: three dutch security analysts discovered the vulnerabilities—five in total—in a european radio standard called tetra (terrestrial trunked radio), which is used in radios made by motorola, damm, hytera, and others. As such, tetra was one of the last bastions of widely deployed secret proprietary cryptography. we will discuss in detail how we managed to obtain the primitives and remain legally at liberty to publish our findings. In this talk, we will make public the tetra cipher suites (tea and taa1 to be precise), one of the last bastions of widely deployed secret crypto, and discuss in depth how we managed to obtain them.

Tetra Professional Digital Radios Aikom International Three dutch security analysts discovered five vulnerabilities in a european radio standard called tetra (terrestrial trunked radio), which is used in radios made by motorola, damm, hytera, and others. Here’s the story: three dutch security analysts discovered the vulnerabilities—five in total—in a european radio standard called tetra (terrestrial trunked radio), which is used in radios made by motorola, damm, hytera, and others. As such, tetra was one of the last bastions of widely deployed secret proprietary cryptography. we will discuss in detail how we managed to obtain the primitives and remain legally at liberty to publish our findings. In this talk, we will make public the tetra cipher suites (tea and taa1 to be precise), one of the last bastions of widely deployed secret crypto, and discuss in depth how we managed to obtain them.

Understanding Tetra Radios A Complete Guide For Industrial As such, tetra was one of the last bastions of widely deployed secret proprietary cryptography. we will discuss in detail how we managed to obtain the primitives and remain legally at liberty to publish our findings. In this talk, we will make public the tetra cipher suites (tea and taa1 to be precise), one of the last bastions of widely deployed secret crypto, and discuss in depth how we managed to obtain them.
Comments are closed.