What Are Stack Cookies Software Mitigations For Stack Buffer Overflows

Github B1rby Stack Based Buffer Overflows Stack Based Buffer In this video, we'll explore the basics of the stack guard stack cookie, how to identify them in ida pro, and then see them disrupt our buffer overflow in windbg. Retguard is only a small improvement over stack cookies: it adds cookies diversity, and makes the cookies read only. otherwise, it is roughly subject to the same limitations.

Github B1rby Stack Based Buffer Overflows Stack Based Buffer Stack canaries, also known as stack cookies, are a defense mechanism used to detect buffer overflow attacks that overwrite function return addresses on the stack. the technique involves placing a small, random value (the canary) between the buffer and the control data on the stack. Stack canaries or security cookies are tell tale values added to binaries during compilation to protect critical stack values like the return pointer against buffer overflow attacks. We'll explore this early anti exploit technique as a way to help prevent, or at least detect, buffer overflows 👇 lnkd.in gketggyy you'll see how they work, how the stack can be. Cookies are likely one of your favorite sugary snacks, however in the context of cyber security this is normally a term used by exploit developers in regard to a security mitigation designed to prevent buffer overflows (also known as stack overflows).

Stack Based Buffer Overflows We'll explore this early anti exploit technique as a way to help prevent, or at least detect, buffer overflows 👇 lnkd.in gketggyy you'll see how they work, how the stack can be. Cookies are likely one of your favorite sugary snacks, however in the context of cyber security this is normally a term used by exploit developers in regard to a security mitigation designed to prevent buffer overflows (also known as stack overflows). Stack canaries are security measures used to prevent buffer overflow attacks by placing a random value in the stack before the return address, making it harder for attackers to overwrite it. In a typical buffer overflow attack, the attacker's data is used to try to overwrite the saved eip (extended instruction pointer) on the stack. however, before this can happen, the cookie is also overwritten, rendering the exploit ineffective (though it may still cause a denial of service). Canaries or canary words or stack cookies are known values that are placed between a buffer and control data on the stack to monitor buffer overflows. In the next section, i’ll provide an introduction to control flow attacks with particular focus on stack buffer overflows. i’ll discuss how they occur and how an attacker can exploit them.
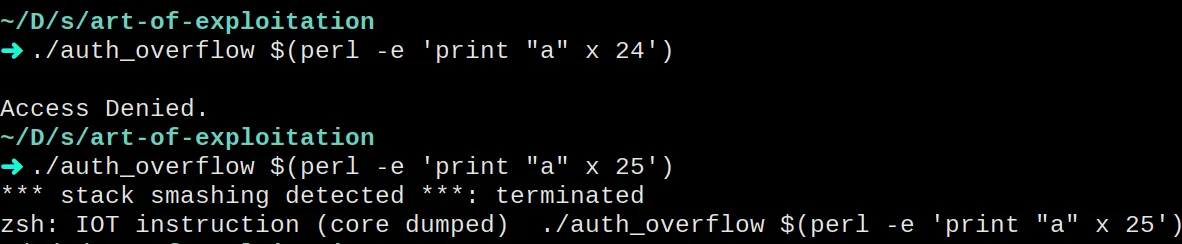
Stack Based Buffer Overflows Stack canaries are security measures used to prevent buffer overflow attacks by placing a random value in the stack before the return address, making it harder for attackers to overwrite it. In a typical buffer overflow attack, the attacker's data is used to try to overwrite the saved eip (extended instruction pointer) on the stack. however, before this can happen, the cookie is also overwritten, rendering the exploit ineffective (though it may still cause a denial of service). Canaries or canary words or stack cookies are known values that are placed between a buffer and control data on the stack to monitor buffer overflows. In the next section, i’ll provide an introduction to control flow attacks with particular focus on stack buffer overflows. i’ll discuss how they occur and how an attacker can exploit them.
Comments are closed.