What Are Cryptographic Protocols Next Lvl Programming

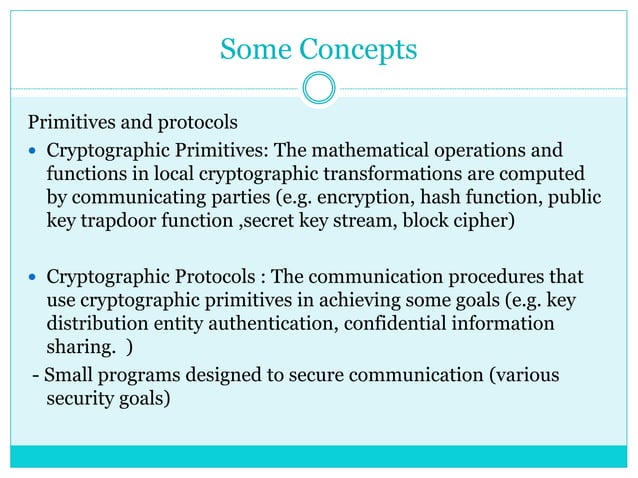
4 2 Cryptographic Coding Part 2 Pdf Cryptography Public Key What are cryptographic protocols? in this informative video, we’ll break down the concept of cryptographic protocols and their importance in securing online communications and. A cryptographic protocol is an abstract or concrete protocol that performs a security related function and applies cryptographic methods, often as sequences of cryptographic primitives.
What Are Cryptographic Protocols Types And More Learn about cryptographic protocols, the essential rules and procedures that secure data and communication online. discover how protocols like ssl tls, ssh, and pgp protect confidentiality, integrity, and authentication in digital transactions and interactions. Cryptography is a process of hiding transmitted information by the sender such that it may be read only by the intended recipient. in this article, we will learn more about various cryptographic algorithms. In order to provide a secure virtual private network style connection, authentication and encryption are needed. while the ah and esp protocols can provide authentication, for the ip packet and the payload respectively, only the esp protocol can provide encryption. Mpatible with its own trust policy. we embody these ideas in a cryptographic protocol pro gramming language cppl at the dolev yao level of abstraction. a strand space semantics for cppl shaped a protocol designer to prove that a protocol is sound.

Cryptographic Protocols Key Components Types Applications All To Buzz In order to provide a secure virtual private network style connection, authentication and encryption are needed. while the ah and esp protocols can provide authentication, for the ip packet and the payload respectively, only the esp protocol can provide encryption. Mpatible with its own trust policy. we embody these ideas in a cryptographic protocol pro gramming language cppl at the dolev yao level of abstraction. a strand space semantics for cppl shaped a protocol designer to prove that a protocol is sound. Cryptographic protocols are structured procedures or rules that govern the secure exchange of information between parties in a digital environment. they utilize cryptographic algorithms to ensure confidentiality, integrity, authentication, and non repudiation of data. Cryptography is fundamental to the confidentiality and integrity of applications and systems. the owasp cheat sheet series describes the use of cryptography and some of these are listed in the further reading at the end of this section. Nist has a full cryptographic standards portfolio covering the essential cryptographic primitives (low level, established cryptographic algorithms often used in developing cryptographic protocols) and guidelines on how to use the primitives in different applications. Cryptographic protocols are a set of rules and procedures that are used to secure the transfer of sensitive information across a network. these protocols use encryption to protect the confidentiality, integrity, and authenticity of the data during transmission.
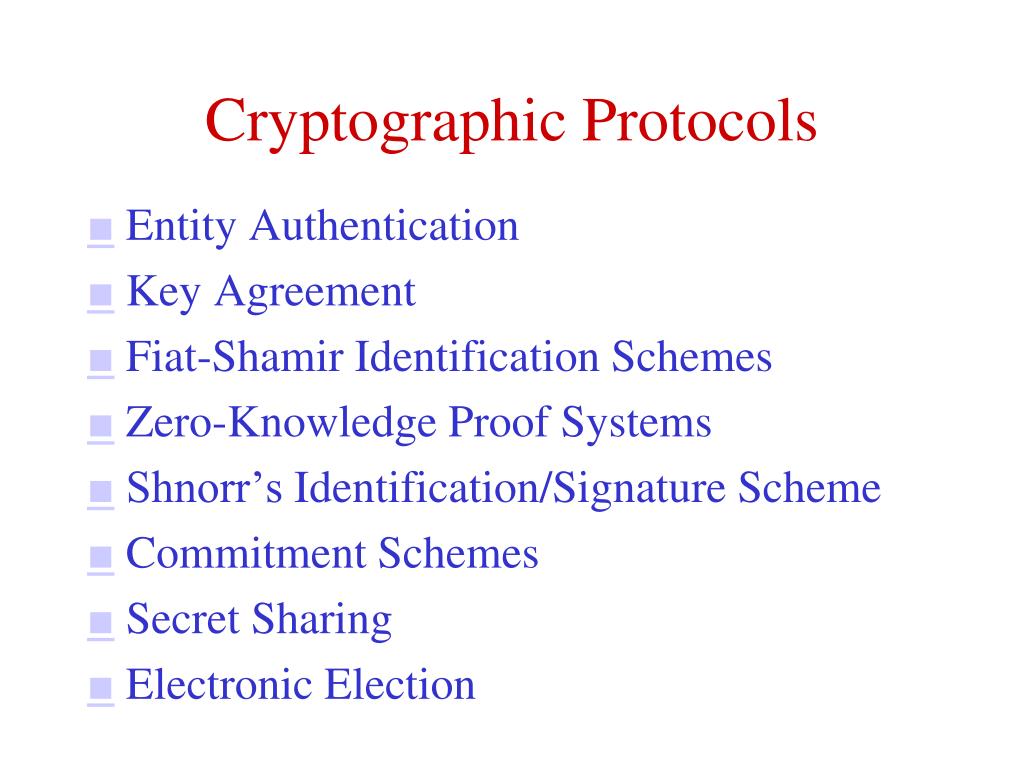
Ppt Cryptographic Protocols Powerpoint Presentation Free Download Cryptographic protocols are structured procedures or rules that govern the secure exchange of information between parties in a digital environment. they utilize cryptographic algorithms to ensure confidentiality, integrity, authentication, and non repudiation of data. Cryptography is fundamental to the confidentiality and integrity of applications and systems. the owasp cheat sheet series describes the use of cryptography and some of these are listed in the further reading at the end of this section. Nist has a full cryptographic standards portfolio covering the essential cryptographic primitives (low level, established cryptographic algorithms often used in developing cryptographic protocols) and guidelines on how to use the primitives in different applications. Cryptographic protocols are a set of rules and procedures that are used to secure the transfer of sensitive information across a network. these protocols use encryption to protect the confidentiality, integrity, and authenticity of the data during transmission.

Pdf Programming Cryptographic Protocols Nist has a full cryptographic standards portfolio covering the essential cryptographic primitives (low level, established cryptographic algorithms often used in developing cryptographic protocols) and guidelines on how to use the primitives in different applications. Cryptographic protocols are a set of rules and procedures that are used to secure the transfer of sensitive information across a network. these protocols use encryption to protect the confidentiality, integrity, and authenticity of the data during transmission.
Cryptographic Protocols Pptx Information And Network Security
Comments are closed.