Webinar Analyzing Clickfix

Clik On Linkedin Webinar Softwareupdate Niceic Register for the webinar to learn about how users interacting with malicious scripts in their web browser is a fast growing source of security breaches. Clickfix, filefix, fake captcha — whatever you call it, attacks where users interact with malicious scripts in their web browser are a fast growing source of security breaches.
Webinar Recording Critical Analysis You Can Do Today That This webinar examined how modern phishing attacks use evasive delivery chains and infostealers to bypass traditional defenses, with a focus on detecting clickfix attacks, analyzing metastealer configurations, and automating phishing analysis using knowbe4 phisher. Threat actors leveraging clickfix rely on a variety of methods to lure unwitting users. we’ve observed three primary avenues where a user could encounter a clickfix prompt: by receiving phishing emails, encountering a malicious ad, or by visiting a compromised or malicious website. The way attackers are getting users to trigger these commands especially through compromised websites and search engine results is what makes clickfix stand out today. Join us as we break down the entire clickfix attack chain, from the initial access phase to the execution phase.
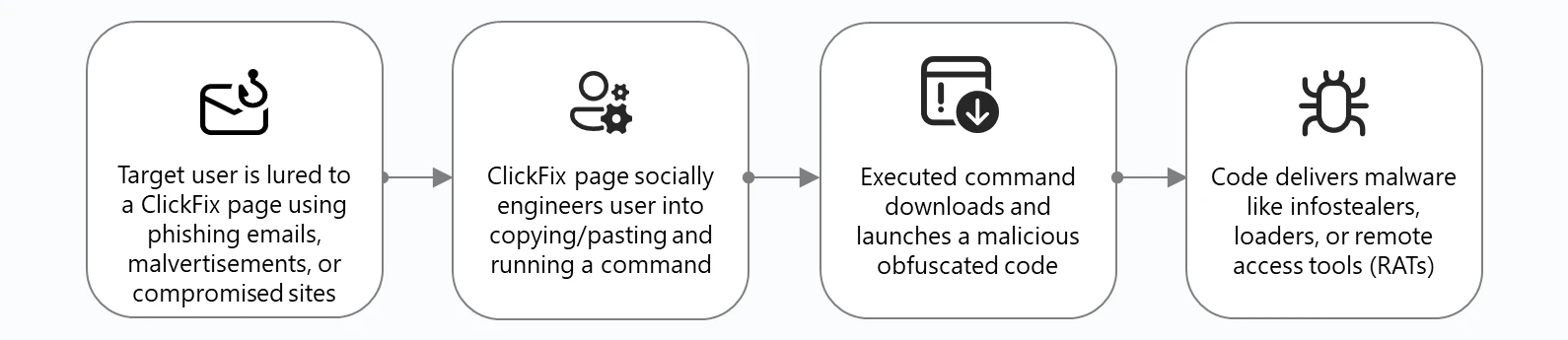
Think Before You Click Fix Analyzing The Clickfix Social Engineering The way attackers are getting users to trigger these commands especially through compromised websites and search engine results is what makes clickfix stand out today. Join us as we break down the entire clickfix attack chain, from the initial access phase to the execution phase. Learn how clickfix techniques like filefix, terminalfix, and downloadfix trick users into compromising. then, learn proven detection methods using chokepoint strategies and behavioral analytics. This clickfix variant underscores how attackers increasingly rely on native windows utilities and carefully constructed command chains to execute payloads and establish persistence. by shifting execution into trusted binaries and remote infrastructure, adversaries reduce detection visibility while increasing the likelihood of successful compromise. This table demonstrates how clickfix social engineering tactics systematically exploit fundamental human psychological traits and behavioral patterns, making it one of the most effective cybersecurity threats in the current landscape. Insikt group reveals five clickfix social engineering clusters (quickbooks, booking , birdeye) targeting windows and macos. learn how threat actors exploit native system tools with malicious, obfuscated commands to gain initial access, and get key mitigations for defense.
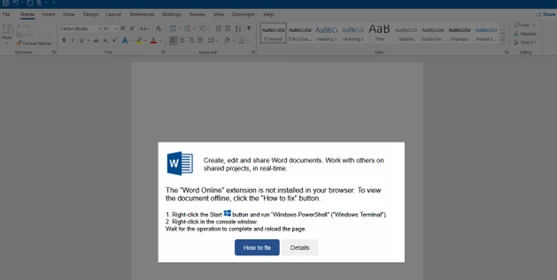
Think Before You Click Fix Analyzing The Clickfix Social Engineering Learn how clickfix techniques like filefix, terminalfix, and downloadfix trick users into compromising. then, learn proven detection methods using chokepoint strategies and behavioral analytics. This clickfix variant underscores how attackers increasingly rely on native windows utilities and carefully constructed command chains to execute payloads and establish persistence. by shifting execution into trusted binaries and remote infrastructure, adversaries reduce detection visibility while increasing the likelihood of successful compromise. This table demonstrates how clickfix social engineering tactics systematically exploit fundamental human psychological traits and behavioral patterns, making it one of the most effective cybersecurity threats in the current landscape. Insikt group reveals five clickfix social engineering clusters (quickbooks, booking , birdeye) targeting windows and macos. learn how threat actors exploit native system tools with malicious, obfuscated commands to gain initial access, and get key mitigations for defense.
Comments are closed.