Web Crypto Tutorial Digest Hashing Example
Cryptography Message Digest Checksum Hash Sha1 Md5 The digest() method of the subtlecrypto interface generates a digest of the given data, using the specified hash function. a digest is a short fixed length value derived from some variable length input. Reference : 8gwifi.org docs window crypto web crypto api tutorial the subtlecrypto.digest () method returns a promise of a digest generated from the hash function and text.

Free Video Cryptography Lab Introduction To Hashing Techniques From The subtlecrypto.digest () method returns a promise of a digest generated from the hash function and text given as parameters. I couldn't find anywhere that had clear examples of webcryptoapi, so i wrote examples and made a live table with them. pull requests welcome!. The web crypto api provides built in cryptographic operations that let you compute secure hash values directly in the browser. this post explores how to implement client side file hashing to detect data tampering or corruption during file transfers. This sample chapter extracted from the book, cryptography for javascript developers. the crypto interface represents an interface to general purpose cryptographic functionality including a cryptographically strong pseudo random number generator seeded with truly random values.

Cryptography Encryption And Hashing Information Technology The web crypto api provides built in cryptographic operations that let you compute secure hash values directly in the browser. this post explores how to implement client side file hashing to detect data tampering or corruption during file transfers. This sample chapter extracted from the book, cryptography for javascript developers. the crypto interface represents an interface to general purpose cryptographic functionality including a cryptographically strong pseudo random number generator seeded with truly random values. Digest algorithms, also known as cryptographic hash functions, transform an arbitrarily large block of data into a fixed size output, usually much shorter than the input. Message digest is used to ensure the integrity of a message transmitted over an insecure channel (where the content of the message can be changed). it refers to a fixed size numerical representation (hash value) of a message or data, created by a hash function. Computes a cryptographic hash (digest) of the given data. this method is commonly used for verifying data integrity. Convert string to arraybuffer. this step is only necessary if you wish to hash a string, not if you aready got an arraybuffer such as an uint8array. var input = new textencoder('utf 8').encode('hello world!'); digest is an arraybuffer. there are multiple ways to proceed.
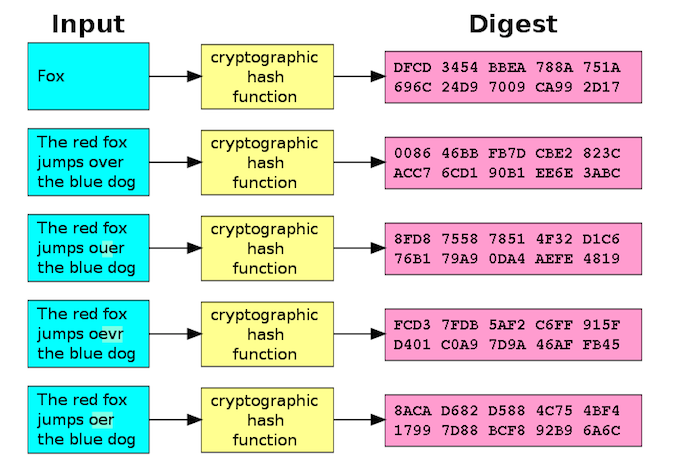
Cryptographic Hashes Used To Store Passwords Detect Malware Digest algorithms, also known as cryptographic hash functions, transform an arbitrarily large block of data into a fixed size output, usually much shorter than the input. Message digest is used to ensure the integrity of a message transmitted over an insecure channel (where the content of the message can be changed). it refers to a fixed size numerical representation (hash value) of a message or data, created by a hash function. Computes a cryptographic hash (digest) of the given data. this method is commonly used for verifying data integrity. Convert string to arraybuffer. this step is only necessary if you wish to hash a string, not if you aready got an arraybuffer such as an uint8array. var input = new textencoder('utf 8').encode('hello world!'); digest is an arraybuffer. there are multiple ways to proceed.

The Difference Between Encryption Hashing And Salting Computes a cryptographic hash (digest) of the given data. this method is commonly used for verifying data integrity. Convert string to arraybuffer. this step is only necessary if you wish to hash a string, not if you aready got an arraybuffer such as an uint8array. var input = new textencoder('utf 8').encode('hello world!'); digest is an arraybuffer. there are multiple ways to proceed.
Comments are closed.