Web Application Penetration Testing Input Validation
Web Application Penetration Testing Steps Methods Tools Purplesec Data from all potentially untrusted sources should be subject to input validation, including not only internet facing web clients but also backend feeds over extranets, from suppliers, partners, vendors or regulators, each of which may be compromised on their own and start sending malformed data. Input validation is a fundamental concept of penetration testing. this guide is written for new pentesters and developers looking to bolster these core skills.

A Comprehensive Guide To Web Application Penetration Testing Steps In this course, you’ll learn how to test for input validation in web applications. the majority of attacks on web applications are related to improper input validation and that’s the reason why this subject is interesting for penetration testers. Input validation is performed by websites to ensure that data entered into the website is valid. if input validation is inadequate, an attacker may be able to use http requests to inject malicious data into the vulnerable website. Data from all potentially untrusted sources should be subject to input validation, including not only internet facing web clients but also backend feeds over extranets, from suppliers, partners, vendors or regulators, each of which may be compromised on their own and start sending malformed data. User input fields such as search boxes, comment sections, and signup forms can be exploited if not properly validated, leading to attacks like sql injection or cross site scripting (xss).

Web Penetration Testing Web Application Reconnaissance Techniques For Data from all potentially untrusted sources should be subject to input validation, including not only internet facing web clients but also backend feeds over extranets, from suppliers, partners, vendors or regulators, each of which may be compromised on their own and start sending malformed data. User input fields such as search boxes, comment sections, and signup forms can be exploited if not properly validated, leading to attacks like sql injection or cross site scripting (xss). This page details methodologies for identifying and exploiting vulnerabilities that arise from improper input validation, which can lead to various injection attacks, data manipulation, and unauthorized access to systems. Assess the input they accept and the encoding that gets applied on return (if any). A core part of a penetration test is to assess how well an application validates input. during a pentest, attempts are made with all available inputs to access unauthorized data, tamper with database queries, and inject javascript. Input validation: ensure robust input validation to reject unexpected or malformed parameters. implement strict validation rules and use whitelists rather than blacklists.
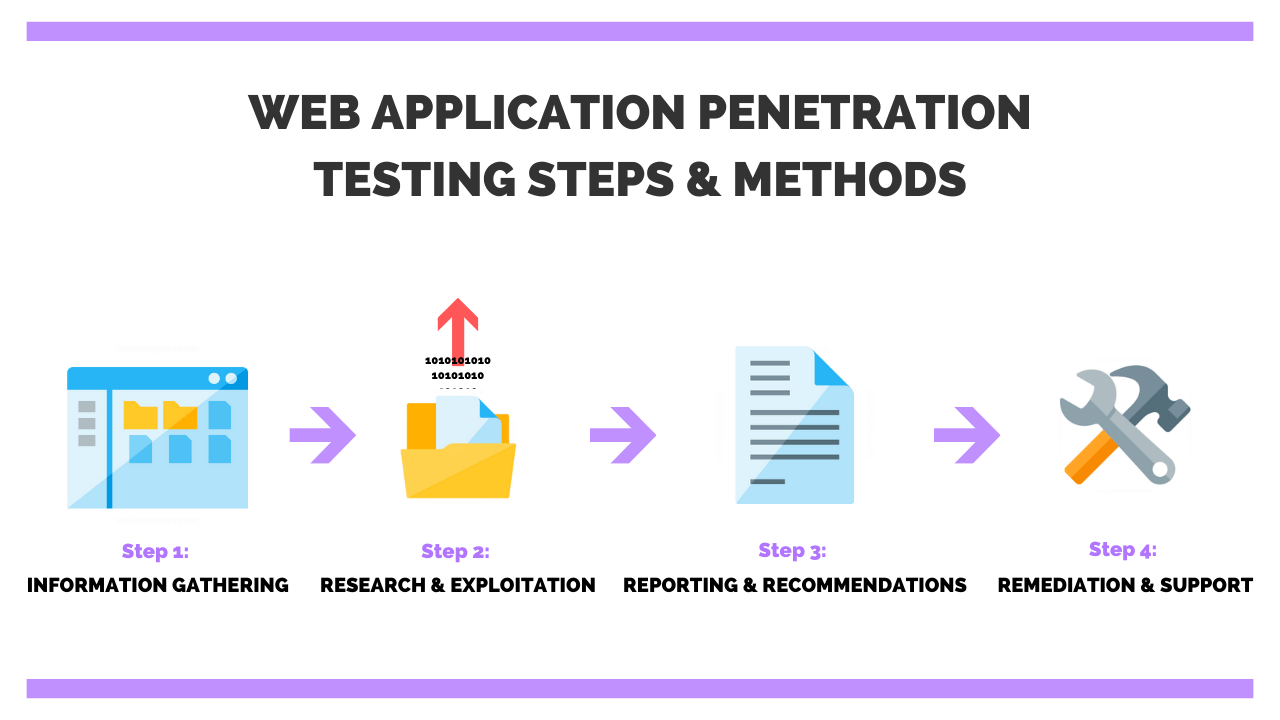
What Is Web Application Penetration Testing This page details methodologies for identifying and exploiting vulnerabilities that arise from improper input validation, which can lead to various injection attacks, data manipulation, and unauthorized access to systems. Assess the input they accept and the encoding that gets applied on return (if any). A core part of a penetration test is to assess how well an application validates input. during a pentest, attempts are made with all available inputs to access unauthorized data, tamper with database queries, and inject javascript. Input validation: ensure robust input validation to reject unexpected or malformed parameters. implement strict validation rules and use whitelists rather than blacklists.

Web Application Penetration Testing Protect Sensitive Data A core part of a penetration test is to assess how well an application validates input. during a pentest, attempts are made with all available inputs to access unauthorized data, tamper with database queries, and inject javascript. Input validation: ensure robust input validation to reject unexpected or malformed parameters. implement strict validation rules and use whitelists rather than blacklists.
Comments are closed.