Weak Tls Cipher Suites
Weak Tls Cipher Suites Different cipher suites on the ssl tls connection model can vary widely when it comes to security and efficiency. better cipher suites provide a higher level of security against different types of attacks, however, they could cause increased load on the system and decrease its speed. Learn what weak ssl tls cipher suites are, how attackers exploit them (poodle, beast, sweet32), and how to secure your server configurations effectively.
Weak Tls Cipher Suites To reach this goal ssl based services should not offer the possibility to choose weak cipher suite. a cipher suite is specified by an encryption protocol (e.g. des, rc4, aes), the encryption key length (e.g. 40, 56, or 128 bits), and a hash algorithm (e.g. sha, md5) used for integrity checking. Check tls protocol version compatibility and cipher suite strength ratings against current best practices. supports iana and openssl cipher names — rates each suite as strong, weak, or deprecated and explains why. Without proper tls encryption and valid root certificates, unencrypted connections can be exploited by attackers to gain access to critical data, like sending an open postcard instead of a sealed letter. to mitigate these risks, it’s crucial to disable weak cipher suites and avoid outdated protocols in your server configuration. Search for a particular cipher suite by using iana, openssl or gnutls name format, e.g. "tls dhe dss with aes 256 cbc sha256", "dhe dss aes256 sha256", or "tls dhe dss aes 256 cbc sha256".

Weak Tls Cipher Suites Without proper tls encryption and valid root certificates, unencrypted connections can be exploited by attackers to gain access to critical data, like sending an open postcard instead of a sealed letter. to mitigate these risks, it’s crucial to disable weak cipher suites and avoid outdated protocols in your server configuration. Search for a particular cipher suite by using iana, openssl or gnutls name format, e.g. "tls dhe dss with aes 256 cbc sha256", "dhe dss aes256 sha256", or "tls dhe dss aes 256 cbc sha256". The cipher suite analyzer connects to a host and lists which tls cipher suites are supported and which are negotiated for a given connection. it flags weak or deprecated ciphers (e.g. rc4, 3des, null) and recommends modern suites (e.g. aes gcm with ecdhe). use it to harden tls configuration, meet compliance, or debug connection failures. combine with a tls version checker for a full picture of. This database is designed for sysadmins to understand in depth the strengths and weaknesses of each cipher suite and their constituent key exchange and authentication mechanisms, ciphers, and hashes. Track down old, vulnerable tls versions and cipher suites so that you can make informed decisions about whether to allow connections with servers and applications that may compromise your security posture. Why this is a problem suboptimal ciphers may provide inadequate encryption, making it easier for attackers to decrypt data. weak cipher suites allows attackers to exploit them through downgrade attacks or cryptographic weaknesses, this can result in sensitive data being leaked or for attackers to redirect users to malicious sites.
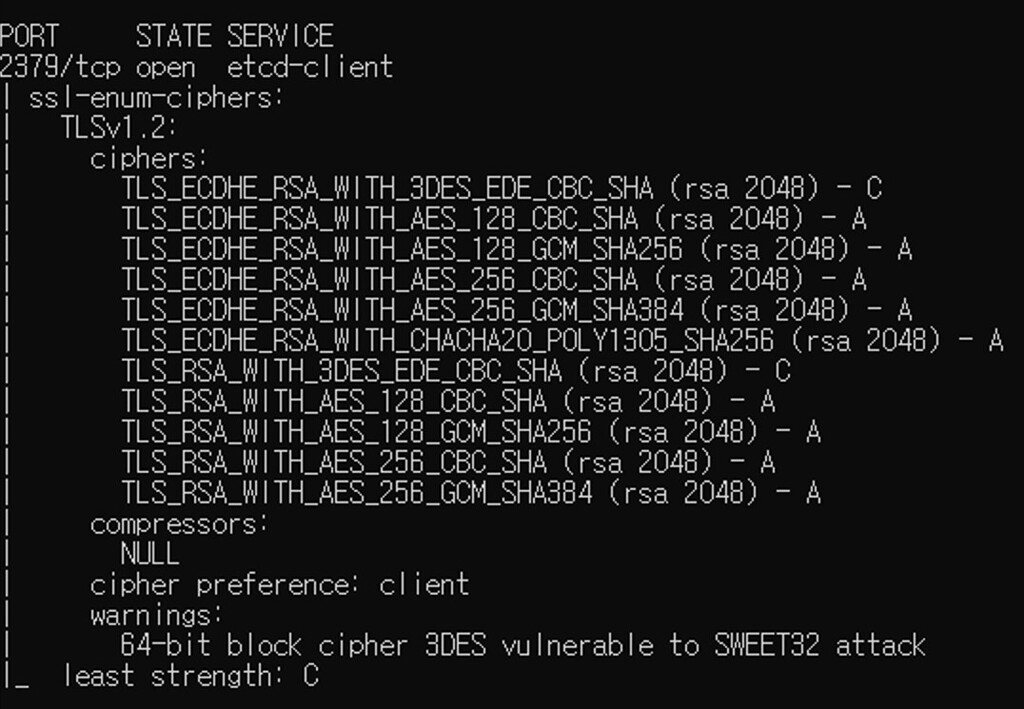
Rancher Rke K8s Using Tls Weak Cipher Suites Issue Suse The cipher suite analyzer connects to a host and lists which tls cipher suites are supported and which are negotiated for a given connection. it flags weak or deprecated ciphers (e.g. rc4, 3des, null) and recommends modern suites (e.g. aes gcm with ecdhe). use it to harden tls configuration, meet compliance, or debug connection failures. combine with a tls version checker for a full picture of. This database is designed for sysadmins to understand in depth the strengths and weaknesses of each cipher suite and their constituent key exchange and authentication mechanisms, ciphers, and hashes. Track down old, vulnerable tls versions and cipher suites so that you can make informed decisions about whether to allow connections with servers and applications that may compromise your security posture. Why this is a problem suboptimal ciphers may provide inadequate encryption, making it easier for attackers to decrypt data. weak cipher suites allows attackers to exploit them through downgrade attacks or cryptographic weaknesses, this can result in sensitive data being leaked or for attackers to redirect users to malicious sites.
Comments are closed.