Vulnerable Java Hacking Java Bytecode Encryption Hackmag
Critical Java Vulnerability Due To Incomplete Earlier Patch Cnn Business At first glance, hacking a java app looks like an easy task due to a large number of available decompilers. but if the code is protected by bytecode encryption, the problem becomes much more complicated. At first glance, hacking a java app looks like an easy task due to a large number of available decompilers. but if the code is protected by bytecode encryption, the problem becomes much more complicated.
All You Need To Know About Encryption In Java Edureka This article provides examples of hacking techniques that can help java developers avoid vulnerabilities in their programs. At first glance, hacking a java app looks like an easy task due to a large number of available decompilers. but if the code is protected by bytecode encryption, the problem becomes much more complicated. Insecure deserialization is a type of vulnerability that arises when an attacker is able to manipulate the serialized object and cause unintended consequences in the program’s flow. this can cause dos, authentication bypass or even rce. However, this portability comes with a tradeoff: java bytecode (stored in .jar files) is designed to be interpreted by the jvm, making it inherently readable and vulnerable to decompilation.

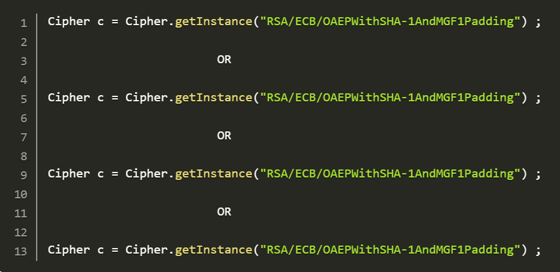
Java Cryptography Hashing Encryption And Signatures A Practical Insecure deserialization is a type of vulnerability that arises when an attacker is able to manipulate the serialized object and cause unintended consequences in the program’s flow. this can cause dos, authentication bypass or even rce. However, this portability comes with a tradeoff: java bytecode (stored in .jar files) is designed to be interpreted by the jvm, making it inherently readable and vulnerable to decompilation. Classcloak aims to be the best free, robust, and powerful obfuscator for your java programs. why put your code through a java obfuscator? can't you distribute your software as is? the short answer: no! java code, in its raw, compiled form, is inherently insecure and easy to reverse engineer. Every java .class file must start with hex magic number cafebabe in the bytecode. let’s change magic number cafebabe to cafe dead using any hex editor and see what happens. Core application security for java developers: covers internal java application security measures after receiving external requests, focusing on securing resource access, input validation, encryption, hashing, secrets management, logging, and deserialization vulnerabilities. In this tutorial, we’ll explore how an attacker can use deserialization in java code to exploit a system. we’ll start by looking at some different approaches an attacker might use to exploit a system.
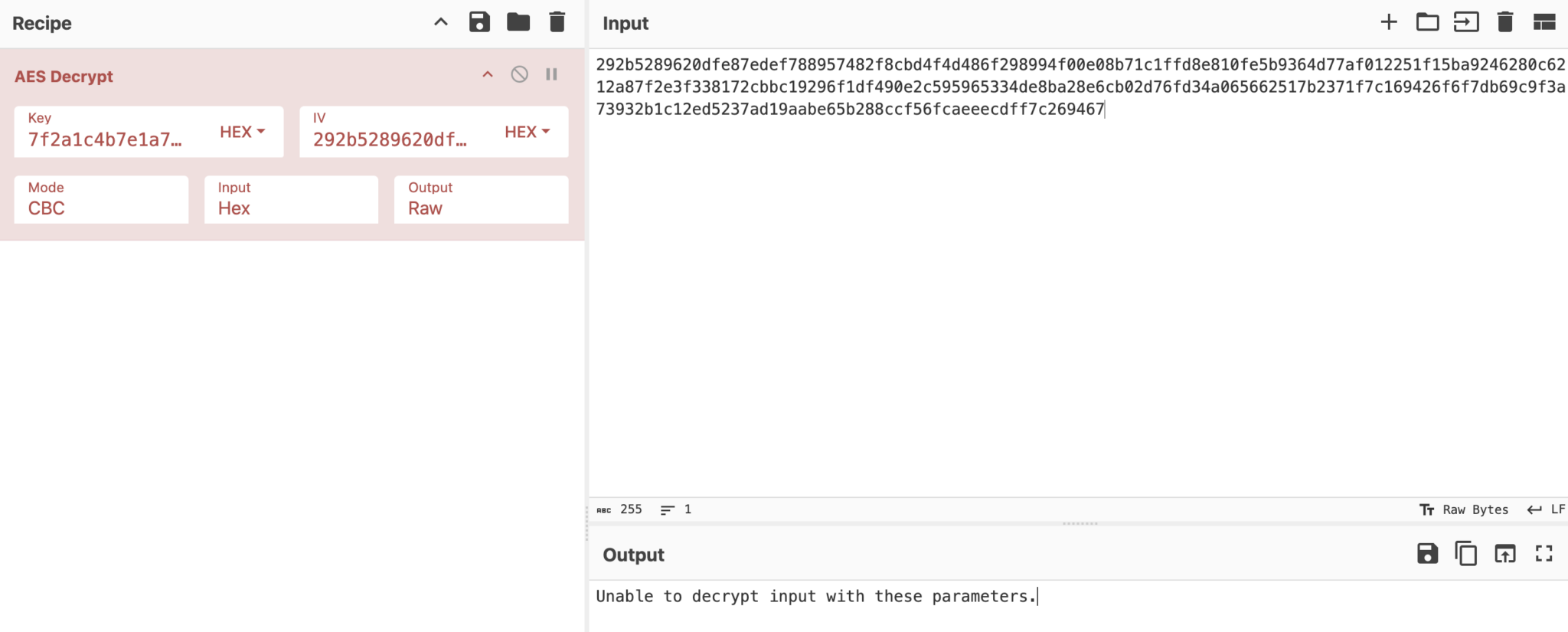
A Guide To Common Encryption Algorithms In Modern Malware Any Run S Classcloak aims to be the best free, robust, and powerful obfuscator for your java programs. why put your code through a java obfuscator? can't you distribute your software as is? the short answer: no! java code, in its raw, compiled form, is inherently insecure and easy to reverse engineer. Every java .class file must start with hex magic number cafebabe in the bytecode. let’s change magic number cafebabe to cafe dead using any hex editor and see what happens. Core application security for java developers: covers internal java application security measures after receiving external requests, focusing on securing resource access, input validation, encryption, hashing, secrets management, logging, and deserialization vulnerabilities. In this tutorial, we’ll explore how an attacker can use deserialization in java code to exploit a system. we’ll start by looking at some different approaches an attacker might use to exploit a system.
 (1)-2.png?width=768&name=Blog header (300 x 175 px) (1)-2.png)
The 10 Major Java Vulnerability Types That Threaten Your Software Core application security for java developers: covers internal java application security measures after receiving external requests, focusing on securing resource access, input validation, encryption, hashing, secrets management, logging, and deserialization vulnerabilities. In this tutorial, we’ll explore how an attacker can use deserialization in java code to exploit a system. we’ll start by looking at some different approaches an attacker might use to exploit a system.
Comments are closed.