Vulnerability Sources
10 Most Common Cybersecurity Vulnerabilities Cyberghost Vpn Identify, define, and catalog publicly disclosed cybersecurity vulnerabilities. there are currently over 324,000 cve records accessible via download or keyword search above. the cve program partners with community members worldwide to grow cve content and expand its usage. This article highlights the critical significance of vulnerability database sources in tracing emerging vulnerabilities within software, hardware, and systems. we will investigate the role of these datasets in the larger cybersecurity ecosystem, where they come from, and what effect they have.
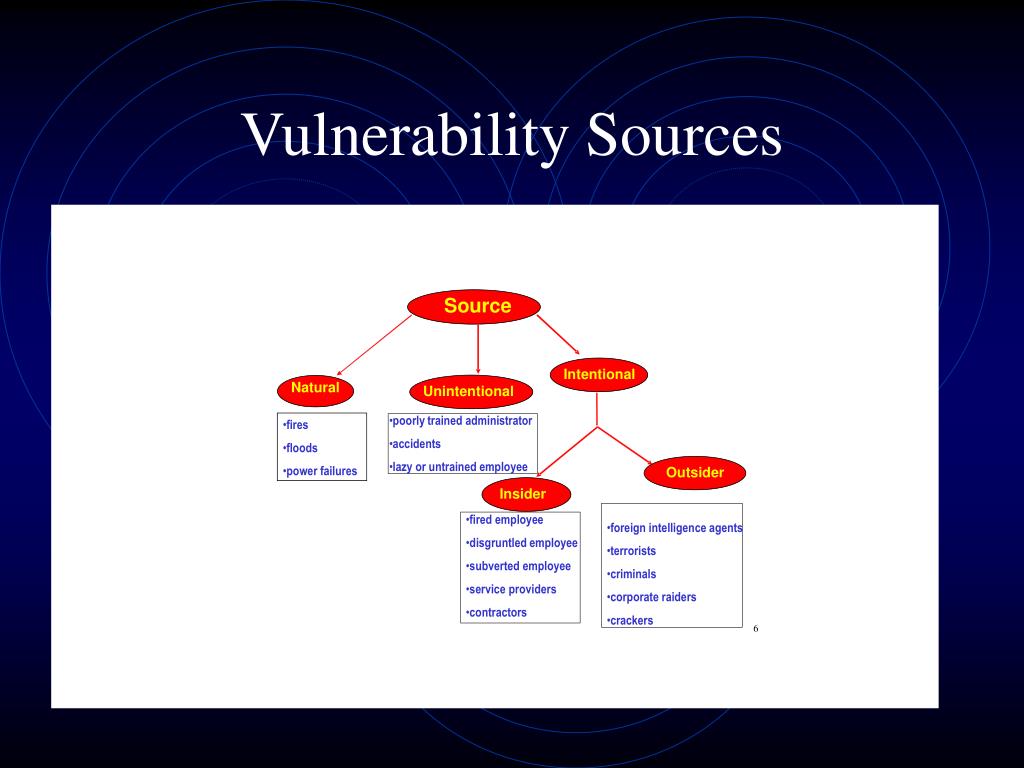
Ppt Is3513 Information Assurance And Security Powerpoint Presentation The nvd is the u.s. government repository of standards based vulnerability management data represented using the security content automation protocol (scap). this data enables automation of vulnerability management, security measurement, and compliance. You can view cve vulnerability details, exploits, references, metasploit modules, full list of vulnerable products and cvss score reports and vulnerability trends over time. Cve find is a cybersecurity vulnerability search engine that aggregates and indexes cve (common vulnerabilities and exposures), cwe, capec and cpe data from mitre, nvd and cisa. Vulnerability sources overview explore the vastness of our vulnerability database. sourced from trusted platforms like android, npm, maven, and github, we ensure detailed security insights. stay informed about open source vulnerabilities and software threats with our extensive and timely data.

Examples Of Cyber Security Vulnerabilities And Their Impact Cve find is a cybersecurity vulnerability search engine that aggregates and indexes cve (common vulnerabilities and exposures), cwe, capec and cpe data from mitre, nvd and cisa. Vulnerability sources overview explore the vastness of our vulnerability database. sourced from trusted platforms like android, npm, maven, and github, we ensure detailed security insights. stay informed about open source vulnerabilities and software threats with our extensive and timely data. Vulnerability database enriched with millions cve, exploits, articles, varied tools and services for vulnerability management against cybersecurity threats. Browse the latest discovered cve vulnerabilities with risk scoring, exploit data, and real time security analytics from cvefeed. Vulnerability lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability ids, and streamlines the management of coordinated vulnerability disclosure (cvd). A curated repository of over 180,000 exploitable vulnerabilities and vetted computer software exploits. exploits are all included in the metasploit framework. this database is updated frequently and contains the most recent security research.

Examples Of Vulnerability Sources And Multihazards Download Vulnerability database enriched with millions cve, exploits, articles, varied tools and services for vulnerability management against cybersecurity threats. Browse the latest discovered cve vulnerabilities with risk scoring, exploit data, and real time security analytics from cvefeed. Vulnerability lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability ids, and streamlines the management of coordinated vulnerability disclosure (cvd). A curated repository of over 180,000 exploitable vulnerabilities and vetted computer software exploits. exploits are all included in the metasploit framework. this database is updated frequently and contains the most recent security research.

3 Risk As A Function Of Hazard Exposure And Vulnerability Sources Vulnerability lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability ids, and streamlines the management of coordinated vulnerability disclosure (cvd). A curated repository of over 180,000 exploitable vulnerabilities and vetted computer software exploits. exploits are all included in the metasploit framework. this database is updated frequently and contains the most recent security research.
What Is Vulnerability In Cyber Security With Example
Comments are closed.