Vulnerability Scanning Cyber Security
How To Scan A Web Application For Vulnerabilities Vulnerability scanning, also called “vulnerability assessment,” is the process of evaluating networks or it assets for security vulnerabilities, flaws or weaknesses that external or internal threat actors can exploit. Vulnerability scanning is the practice of detecting, identifying, and assessing cybersecurity vulnerabilities within an organization’s it infrastructure.

Vulnerability Scanning Cyber Security Vulnerability scanning is the automated process of identifying security weaknesses across systems, applications, and cloud environments. it detects issues such as known vulnerabilities, missing patches, misconfigurations, and exposed components that attackers could exploit. Vulnerability scanning is an automated process to identify security flaws in networks, systems and applications, enabling remediation and enhancing security posture. What is vulnerability scanning? vulnerability scanning is the systematic process of automatically identifying security weaknesses, misconfigurations, and known vulnerabilities in systems, networks, applications, and devices. Vulnerability scanning is the process of discovering, analysing, and reporting security flaws and vulnerabilities. alongside vulnerability assessment, vulnerability scanning is an essential step in the vulnerability management lifecycle.
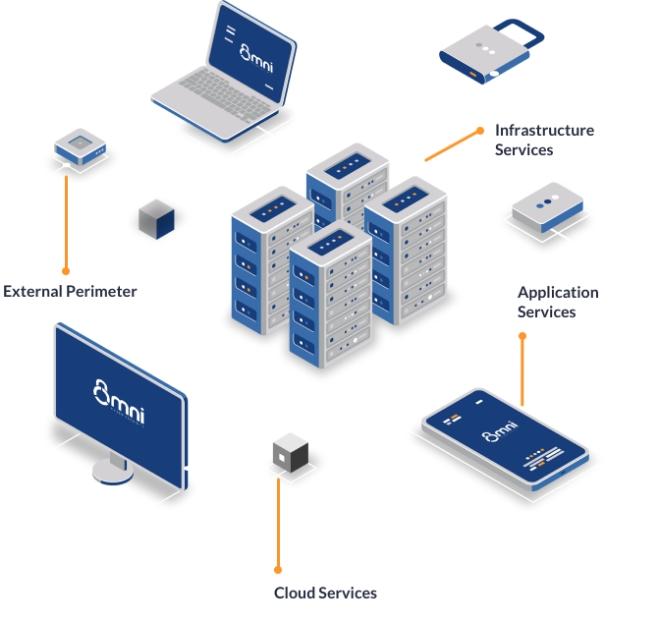
Vulnerability Scanning Omnicyber Security What is vulnerability scanning? vulnerability scanning is the systematic process of automatically identifying security weaknesses, misconfigurations, and known vulnerabilities in systems, networks, applications, and devices. Vulnerability scanning is the process of discovering, analysing, and reporting security flaws and vulnerabilities. alongside vulnerability assessment, vulnerability scanning is an essential step in the vulnerability management lifecycle. Vulnerability scanning scans your systems for known security weaknesses. it’s an automated and non intrusive approach, using approved tools to assess risks and generate reports for remediation. Vulnerability scanning can be an effective way to reduce downtime, avoid compliance headaches, and keep growth on track, all while fitting neatly into a risk based security strategy. for more insights that can help you build a resilient cyber defense. Learn what a vulnerability assessment is, its types, tools, and process, and how it helps find security gaps and reduce risk. Vulnerability scanning is a crucial process within any comprehensive cybersecurity program. it involves the automated detection of security weaknesses in software, systems, and networks, allowing organizations to identify and address potential threats before attackers can exploit them.
Comprehensive Guide To Vulnerability Scanning For Cybersecurity Vulnerability scanning scans your systems for known security weaknesses. it’s an automated and non intrusive approach, using approved tools to assess risks and generate reports for remediation. Vulnerability scanning can be an effective way to reduce downtime, avoid compliance headaches, and keep growth on track, all while fitting neatly into a risk based security strategy. for more insights that can help you build a resilient cyber defense. Learn what a vulnerability assessment is, its types, tools, and process, and how it helps find security gaps and reduce risk. Vulnerability scanning is a crucial process within any comprehensive cybersecurity program. it involves the automated detection of security weaknesses in software, systems, and networks, allowing organizations to identify and address potential threats before attackers can exploit them.

What Is Vulnerability Scanning In Cybersecurity Learn what a vulnerability assessment is, its types, tools, and process, and how it helps find security gaps and reduce risk. Vulnerability scanning is a crucial process within any comprehensive cybersecurity program. it involves the automated detection of security weaknesses in software, systems, and networks, allowing organizations to identify and address potential threats before attackers can exploit them.

5 Types Of Vulnerability Scanning Tools For Cyber Security Best Practices
Comments are closed.