Vulnerability Remediation Process Best Practices
Vulnerability Remediation How To Automate Your Process Learn what vulnerability remediation is, key steps, tools, metrics, and best practices to secure systems and manage cloud security risks. Learn vulnerability remediation best practices from risk based prioritization to patch management and automation.

How To Plan And Automate Your Vulnerability Remediation Process Explore 15 vulnerability remediation best practices, from timelines to real world strategies, to reduce cyber risk and strengthen security resilience. Vulnerabilities in your it environment should be addressed promptly. here are 7 best practices to meet your vulnerability remediation timelines. The essential vulnerability management best practices that every organization should start with are: establish a vulnerability management program and put it into use, secure your cloud native applications with end to end views, configure policies, assess vulnerabilities in build time and deployment time, leverage vulnerability management tools. In this guide, we’ll walk through the entire vulnerability remediation process from discovery to validation and show how modern teams overcome the challenges of scale, complexity, and resource constraints.
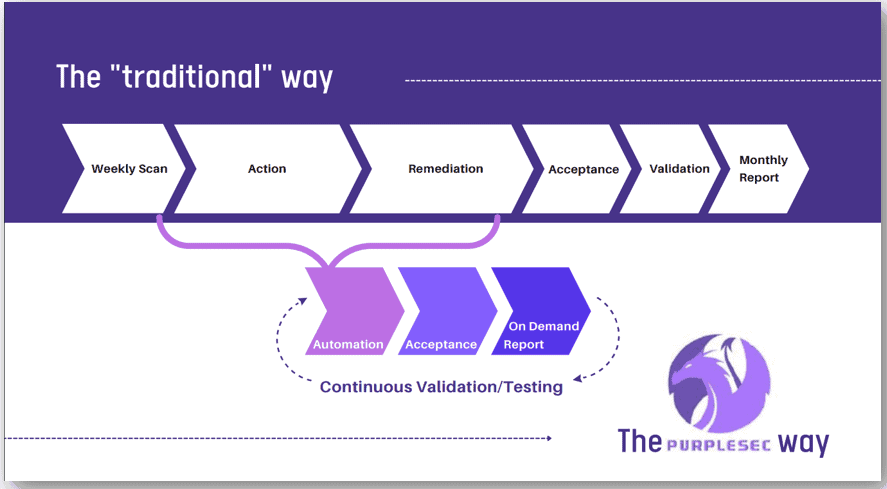
Continuous Vulnerability Management Scanning Remediation Monitoring The essential vulnerability management best practices that every organization should start with are: establish a vulnerability management program and put it into use, secure your cloud native applications with end to end views, configure policies, assess vulnerabilities in build time and deployment time, leverage vulnerability management tools. In this guide, we’ll walk through the entire vulnerability remediation process from discovery to validation and show how modern teams overcome the challenges of scale, complexity, and resource constraints. Vulnerability remediation is not just patching. it includes triage, risk based prioritization, assignment, patching, compensating controls, verification, and continuous tracking across the entire it environment. Learn what vulnerability remediation is, how it differs from vulnerability management, and how to prioritize and fix security flaws effectively. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase. By understanding the core components of vulnerability remediation — identification, prioritization, remediation, and verification — you can see the importance of this continuous process.
Comments are closed.