Vulnerability Management Process Flow Chart Cyberix
Vulnerability Management Process Flow Chart Pdf Vulnerability Explore cyberix’s vulnerability management process flow chart to identify, assess, and remediate security risks effectively for stronger cyber resilience. This blog provides a comprehensive overview of the vulnerability management process, explaining its meaning and importance in protecting digital assets. we will walk through the key stages, from vulnerability assessment to remediation, mitigation, […].

Vulnerability Management Process Flow Chart Cyberix A 2026 guide to the vulnerability management lifecycle. learn how cyberix helps enterprises prioritize risk, remediate faster, and reduce exposure. What is vulnerability management? vulnerability management is the process of identifying, evaluating, prioritizing, and remediating security flaws within an organization’s network, systems, and applications. A vulnerability management process flow chart may help security professionals make the best decisions for the protection of their organizations. this powerpoint slide showcases a vulnerability management process flow chart for an enterprise. Vulnerability scanning is the process of identifying potential vulnerabilities through automated tools and manual checks, while vulnerability analysis involves understanding the root causes and assessing their potential impact on the organization.
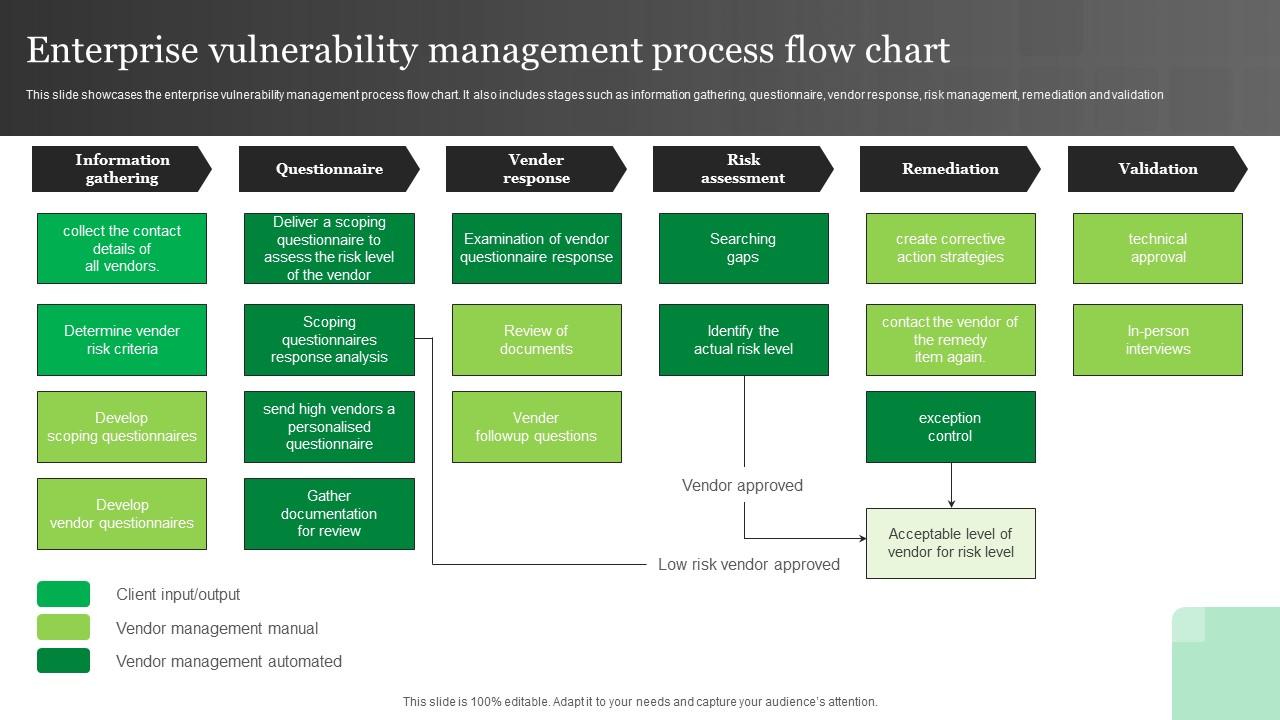
Enterprise Vulnerability Management Process Flow Chart Ppt Example A vulnerability management process flow chart may help security professionals make the best decisions for the protection of their organizations. this powerpoint slide showcases a vulnerability management process flow chart for an enterprise. Vulnerability scanning is the process of identifying potential vulnerabilities through automated tools and manual checks, while vulnerability analysis involves understanding the root causes and assessing their potential impact on the organization. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase. Learn what vulnerability management is, what steps are involved in the process, and how you can implement a robust vulnerability management program that leverages automation. There are five main stages in the vulnerability management lifecycle include: assess, prioritize, act, reassess, improve. learn more here. This procedure aims to define detailed step by step cybersecurity requirements to asses vulnerabilities and protect

Vulnerability Management Process Flow Chart Rootshell Security The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase. Learn what vulnerability management is, what steps are involved in the process, and how you can implement a robust vulnerability management program that leverages automation. There are five main stages in the vulnerability management lifecycle include: assess, prioritize, act, reassess, improve. learn more here. This procedure aims to define detailed step by step cybersecurity requirements to asses vulnerabilities and protect
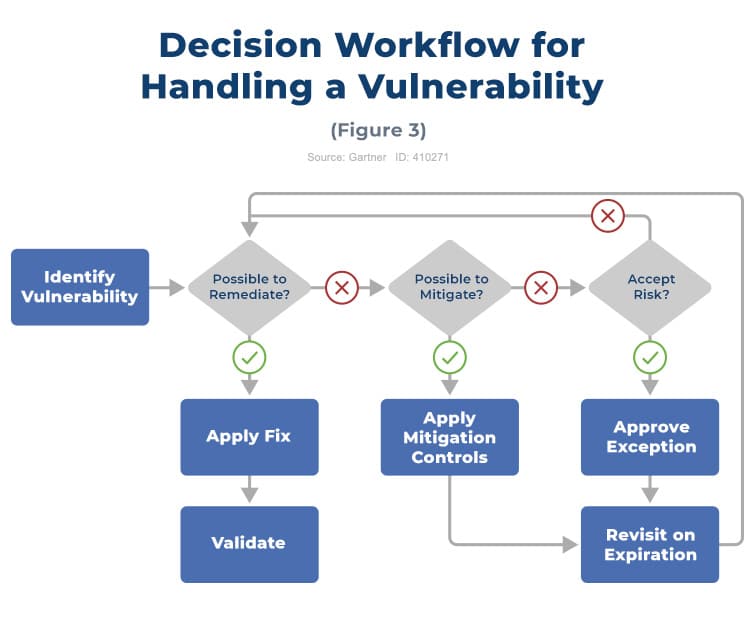
Vulnerability Management Process Flow Chart Rootshell Security There are five main stages in the vulnerability management lifecycle include: assess, prioritize, act, reassess, improve. learn more here. This procedure aims to define detailed step by step cybersecurity requirements to asses vulnerabilities and protect
Comments are closed.