Vulnerability Assessment Cs Computer Systems

Vulnerability Assessment Cs Computer Systems Vulnerability assessment is a pivotal proactive measure in establishing a resilient and secure it environment for businesses. it serves as the foundation for pinpointing and resolving irregularities and vulnerabilities within the network. A vulnerability assessment is the process of defining, identifying, classifying and prioritizing vulnerabilities in computer systems, applications and network infrastructures.

Vulnerability Assessment Clickcontrol It Cybersecurity The process of finding vulnerabilities and risks in computer networks, systems, hardware, applications, and other aspects of the it ecosystem is known as vulnerability assessment. Discover the top vulnerability assessment tools that simplify your cs networking and cybersecurity assignments fast. learn how these tools detect thousands of flaws in networks, web apps, and operating systems. Ility management. this paper presents a comprehensive comparative analysis of three widely used tools: nessus, acunetix, and nikto. each tool is assessed based on its detection accuracy, risk scoring using the common v. A vulnerability assessment—sometimes referred to as vulnerability testing—is a systematic process used to identify, evaluate and report on security weaknesses across an organization’s digital environment.
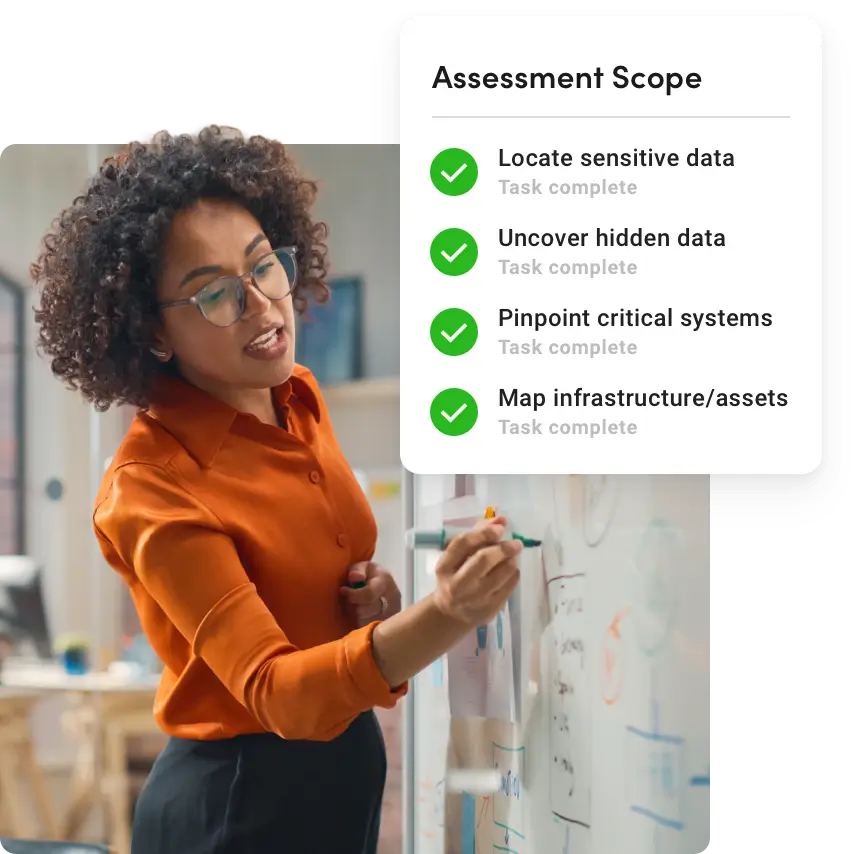
Vulnerability Assessment Identify Remediate Network Risks Ility management. this paper presents a comprehensive comparative analysis of three widely used tools: nessus, acunetix, and nikto. each tool is assessed based on its detection accuracy, risk scoring using the common v. A vulnerability assessment—sometimes referred to as vulnerability testing—is a systematic process used to identify, evaluate and report on security weaknesses across an organization’s digital environment. Learn about the top 10 vulnerability assessment best practices, essential strategies, and proven methods. discover how to minimize risks, improve compliance, and protect your data from new risks now!. Discover how vulnerability assessment methodology helps identify and mitigate security risks effectively to protect your systems from potential cyber threats. Vulnerability assessment is a process that identifies security weaknesses of any it system, network, application, or cloud environment. it is a proactive approach to detect and fix security gaps before any cyber criminals exploit them. Learn what vulnerability analysis is, how it works, key tools, and why it is critical for cybersecurity. a complete beginner to advanced guide by ec council.

Vulnerability Assessment Software And Solutions Ibm Learn about the top 10 vulnerability assessment best practices, essential strategies, and proven methods. discover how to minimize risks, improve compliance, and protect your data from new risks now!. Discover how vulnerability assessment methodology helps identify and mitigate security risks effectively to protect your systems from potential cyber threats. Vulnerability assessment is a process that identifies security weaknesses of any it system, network, application, or cloud environment. it is a proactive approach to detect and fix security gaps before any cyber criminals exploit them. Learn what vulnerability analysis is, how it works, key tools, and why it is critical for cybersecurity. a complete beginner to advanced guide by ec council.

Cyber Security Vulnerability Assessment Ict Byte Vulnerability assessment is a process that identifies security weaknesses of any it system, network, application, or cloud environment. it is a proactive approach to detect and fix security gaps before any cyber criminals exploit them. Learn what vulnerability analysis is, how it works, key tools, and why it is critical for cybersecurity. a complete beginner to advanced guide by ec council.

Vulnerability Assessment Cybersecurity Penetration Testing
Comments are closed.