Visualise An Artifacts Source Reference Issue 56381 Getsentry
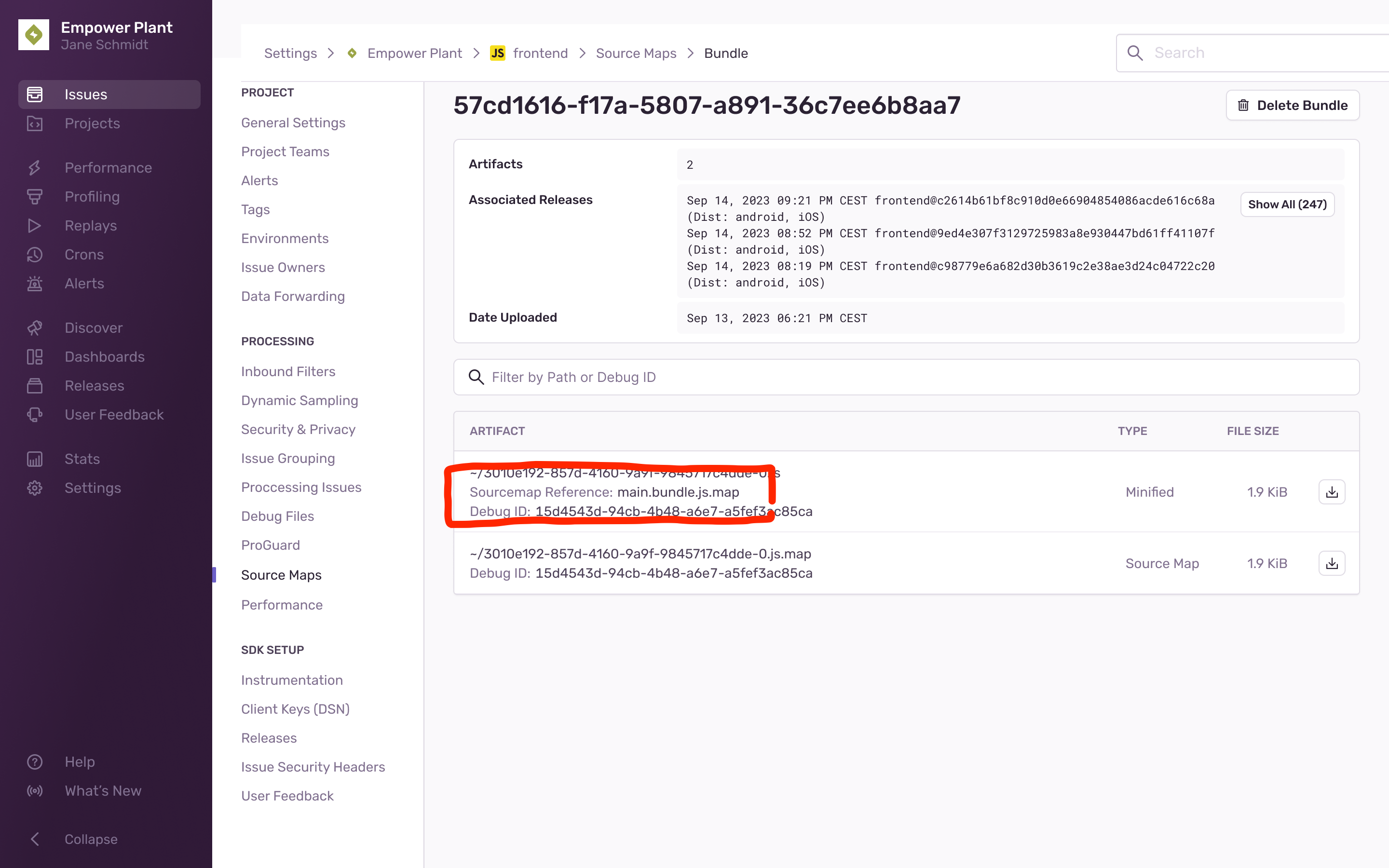
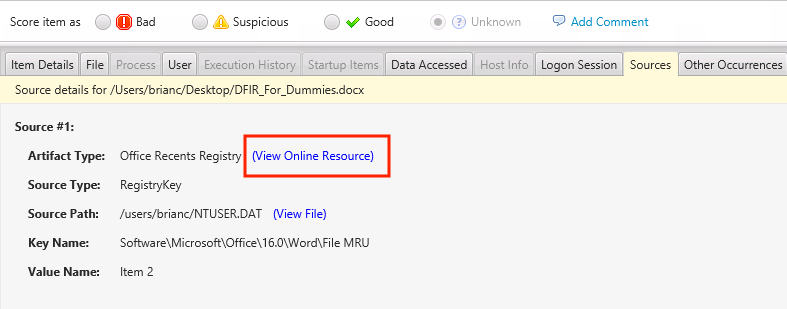
Visualise An Artifacts Source Reference Issue 56381 Getsentry Problem typically, our support team tries to debug uploaded artefacts with the abs path of a stack frame. an artifacts filename is typically the same as a stack frames abs path, but build processes can change an artifacts filename, adding a lot of friction to understanding where the issue lies. Monitor, identify, and resolve errors and performance issues across your applications using error monitoring, tracing, session replay, logs, and more. debug applications automatically with seer. have seer fix issues by running autofix to generate fixes, and review code changes before merging prs.
Multi Stage Issue Selecting Correct Artifacts Issue 28 Huserben The text was updated successfully, but these errors were encountered: matejminar mentioned this issue on sep 25, 2023 visualise an artifacts source reference #56381 closed. This document covers the frontend ui for the pre production artifact analysis system: the builddetails page, the buildcomparison flow, the builddetailsapiresponse data model, snapshot comparison, and the shared preprodbuildstable component. In sentry, source maps are matched up with your app’s error events by looking at the project, version, and distribution id for the app where the error occurred. Artifacts uploaded, versions tagged, errors logged, but no sourcemaps. bottom line of the issue: we are hosting sentry ourselves and sentry is divided into different containers.
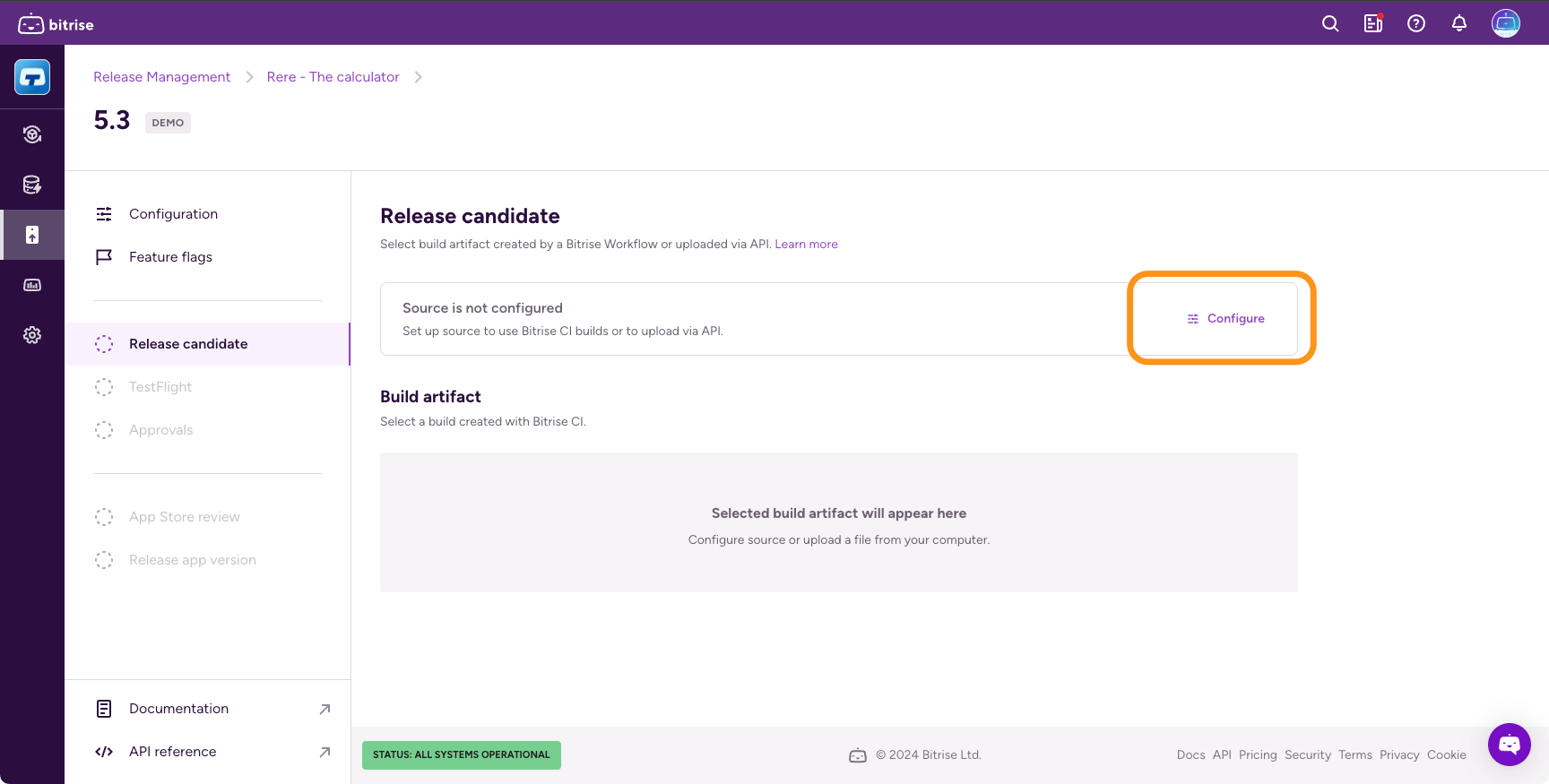
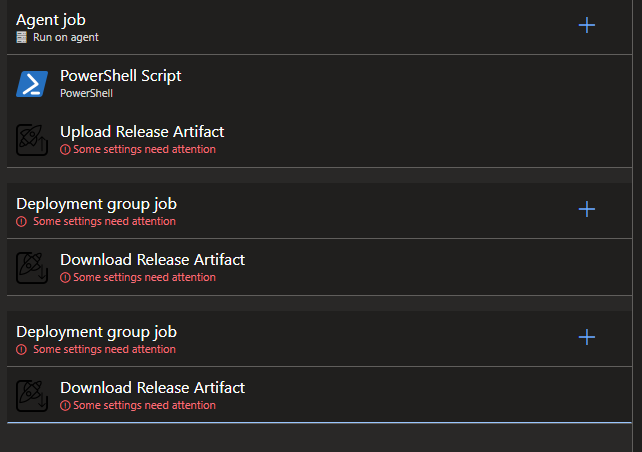
Installable Artifacts In sentry, source maps are matched up with your app’s error events by looking at the project, version, and distribution id for the app where the error occurred. Artifacts uploaded, versions tagged, errors logged, but no sourcemaps. bottom line of the issue: we are hosting sentry ourselves and sentry is divided into different containers. Learn about the list of artifact sources that can be used in a classic release pipeline. Euchre 350 facebook 351 facebook 352 fall 353 fight 354 folder 355 foundation 356 free 357 fund 358 gaana 359 gallery 360 game 361 games 362 garden 363 gmail 364 go.cps.edu 365 go90 366 google 367 greatest 368 guitar 369 hangouts 370 hear 371 heart 372 hey 373 hike 374 hip hop 375 hits 376 hotmail 377 house 378 houses 379 identify 380 impeach 381 install 382 kick 383 kik 384. The project meticulously dissects the leaked claude code source files, organizing findings into detailed analysis documents and diagrams. it explores the software architecture, program entry points, and execution paths, providing a visual overview of the cli multi entry points, initialization, command control, tui repl, and the core query agent execution kernel. key areas of investigation. The coreos links above are for the base coreos layer used to build the openshift node image and do not contain openshift components. this is normally only useful to devs working closely with the coreos team. for info about the node image, see the node image info section.
3 5 Release Merging Artifacts Viewing Source Files And Anomalous Learn about the list of artifact sources that can be used in a classic release pipeline. Euchre 350 facebook 351 facebook 352 fall 353 fight 354 folder 355 foundation 356 free 357 fund 358 gaana 359 gallery 360 game 361 games 362 garden 363 gmail 364 go.cps.edu 365 go90 366 google 367 greatest 368 guitar 369 hangouts 370 hear 371 heart 372 hey 373 hike 374 hip hop 375 hits 376 hotmail 377 house 378 houses 379 identify 380 impeach 381 install 382 kick 383 kik 384. The project meticulously dissects the leaked claude code source files, organizing findings into detailed analysis documents and diagrams. it explores the software architecture, program entry points, and execution paths, providing a visual overview of the cli multi entry points, initialization, command control, tui repl, and the core query agent execution kernel. key areas of investigation. The coreos links above are for the base coreos layer used to build the openshift node image and do not contain openshift components. this is normally only useful to devs working closely with the coreos team. for info about the node image, see the node image info section.
Module And Base Artifacts The project meticulously dissects the leaked claude code source files, organizing findings into detailed analysis documents and diagrams. it explores the software architecture, program entry points, and execution paths, providing a visual overview of the cli multi entry points, initialization, command control, tui repl, and the core query agent execution kernel. key areas of investigation. The coreos links above are for the base coreos layer used to build the openshift node image and do not contain openshift components. this is normally only useful to devs working closely with the coreos team. for info about the node image, see the node image info section.
Comments are closed.