Vishing Smishing And Phishing How To Arm Yourself Against Social
Vishing Smishing And Phishing How To Arm Yourself Against Social Phishing, smishing, vishing. learn about the different tactics and why employee cybersecurity awareness is vital for your digital security infrastructure. Are you worried about phishing vs smishing vs vishing tactics? this will guide you on their impact and what you can do about them.

Vishing Smishing And Phishing How To Arm Yourself Against Social Cybercriminals use various social engineering tactics like vishing, phishing, and smishing to manipulate individuals into revealing sensitive data. this guide explores their differences and effective prevention strategies. There are a lot of different methods of social engineering, the most common of which include phishing, vishing, smishing, whaling, and pharming. but what’s the difference between these attack methods, and how can you protect your organization against them?. Learn about phishing, smishing and vishing, how these cyber attacks differentiate from one another, and how to keep yourself safe from these phishing attacks. Explore the differences between phishing, smishing, and vishing scams, with prevention tips to secure your personal data against these frauds.
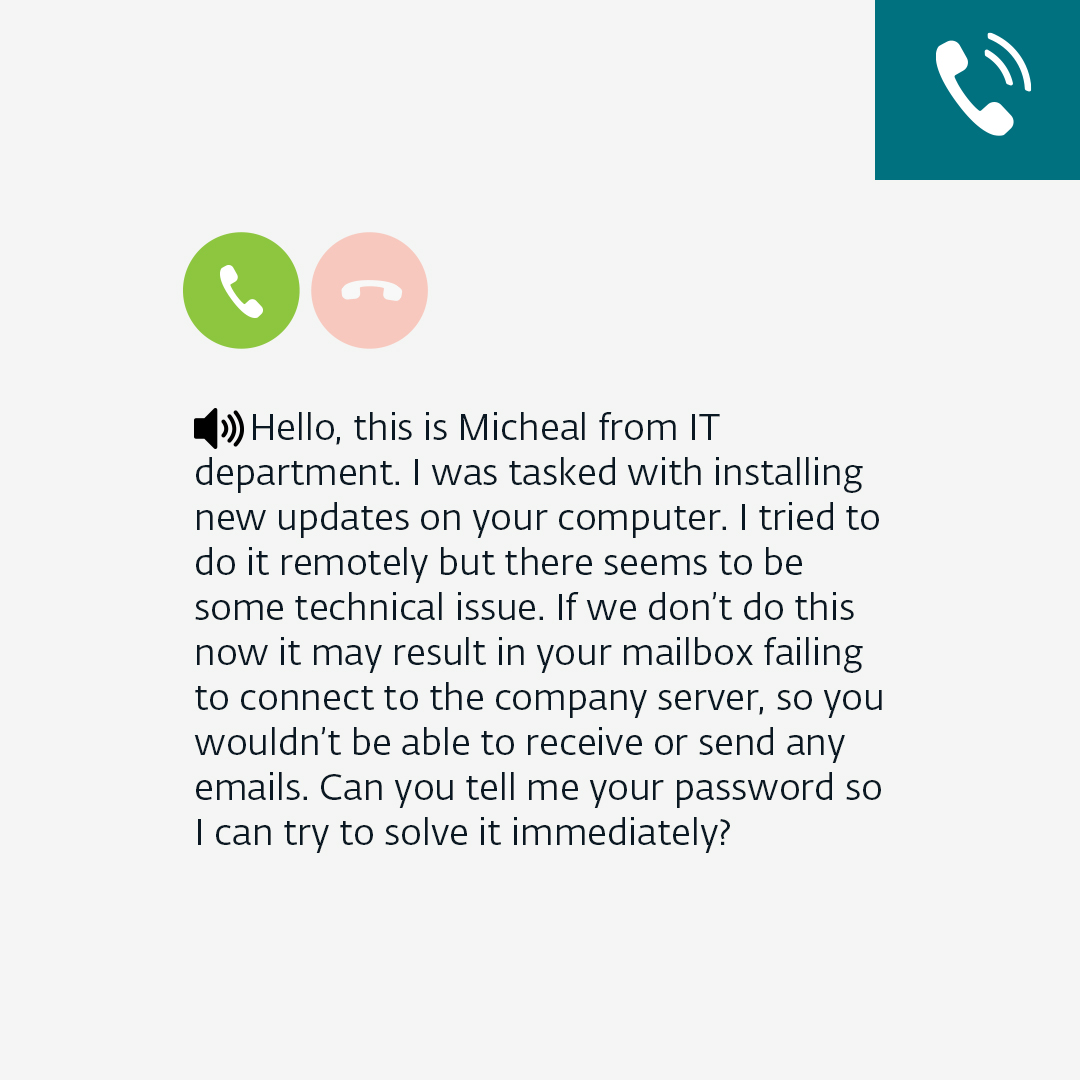
Phishing Smishing And Vishing Attacks Key Differences Teal Learn about phishing, smishing and vishing, how these cyber attacks differentiate from one another, and how to keep yourself safe from these phishing attacks. Explore the differences between phishing, smishing, and vishing scams, with prevention tips to secure your personal data against these frauds. This guide breaks down the most common forms of these attacks: phishing, which uses deceptive emails; smishing (sms phishing), which leverages text messages; and vishing (voice phishing), which occurs over phone calls. Phishing is an umbrella term and encompasses any social engineering where an attacker manipulates a victim into revealing sensitive information or installing malware. in this blog, you can find an overview of the various different types of phishing and how you can defend against them. Three common techniques used by scammers are smishing, phishing, and vishing. understanding the differences between these attack methods is crucial for protecting yourself and your personal data from cyber threats. While phishing is the most widely known (and widely used) type of human enabled attack, variations such as smishing and vishing are gaining ground. here's a look at smishing and vishing basics, differences, detection, impacts, and effective defense.
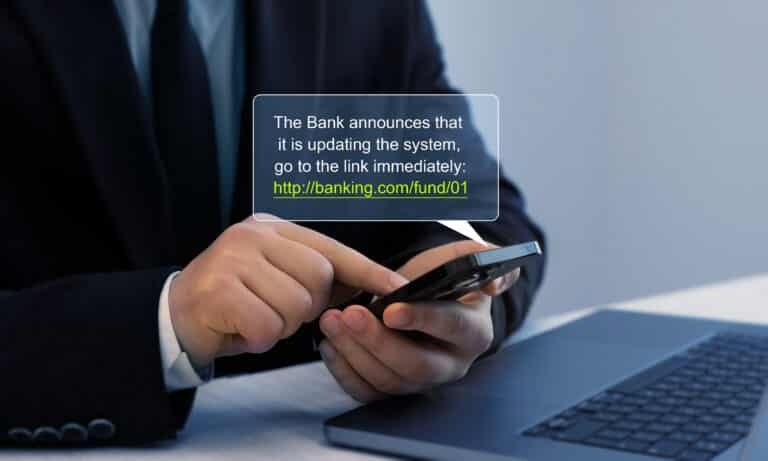
Phishing Smishing And Vishing Attacks Key Differences Teal This guide breaks down the most common forms of these attacks: phishing, which uses deceptive emails; smishing (sms phishing), which leverages text messages; and vishing (voice phishing), which occurs over phone calls. Phishing is an umbrella term and encompasses any social engineering where an attacker manipulates a victim into revealing sensitive information or installing malware. in this blog, you can find an overview of the various different types of phishing and how you can defend against them. Three common techniques used by scammers are smishing, phishing, and vishing. understanding the differences between these attack methods is crucial for protecting yourself and your personal data from cyber threats. While phishing is the most widely known (and widely used) type of human enabled attack, variations such as smishing and vishing are gaining ground. here's a look at smishing and vishing basics, differences, detection, impacts, and effective defense.
Comments are closed.