Using Oidc With Github Actions And Terraform
Github Samiselim Github Actions Oidc Terraform In a production environment, we mostly use terraform to deploy the oidc provider for github action. let me show how you can set up the oidc provider with the help of terraform and how to allow more than one repository. Set up oidc authentication between github actions and cloud providers to run terraform without storing long lived credentials, covering aws, azure, and gcp configurations.
Github Terraform Oidc Ci Cd Github The module configures federation with your aws account using github actions as an open id connect (oidc) identity provider. this allows you to assume an iam role within your account with short lived credentials, removing the need for secrets management. Implementing openid connect (oidc) between github actions and aws represents a significant security upgrade over traditional credential based authentication methods. I figured that if i had already logged in via oidc, then i could just start running terraform commands using the run step. however, the challenge comes into how terraform itself authenticates when you have a backend stored in an azure storage account. With microsoft and github both emphasising identity based access, using oidc for terraform deployments isn’t just secure. it will become the new norm. oidc authentication eliminates the need for storing long lived cloud secrets in your github repositories.
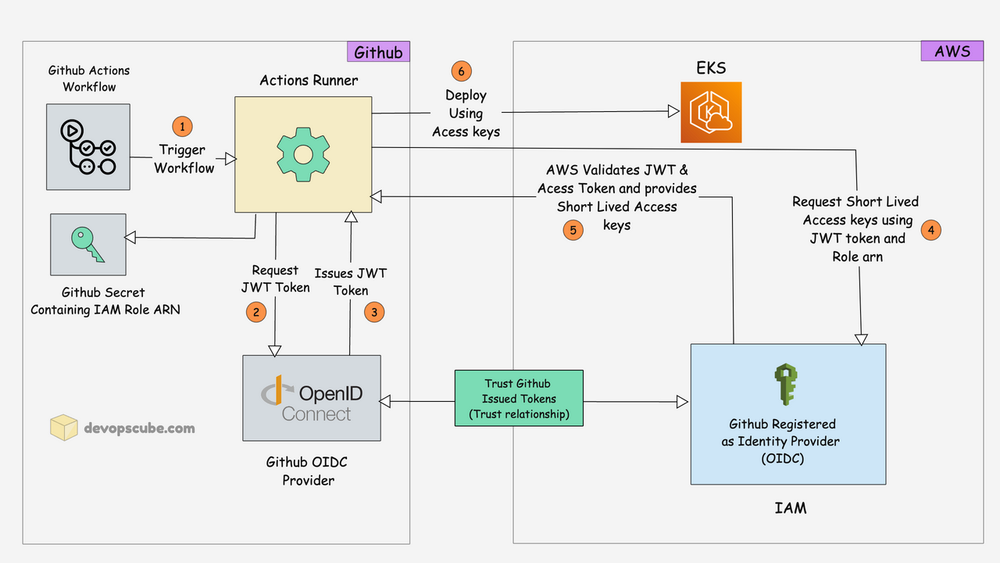
How To Configure Github Actions Oidc With Aws Easy Tutorial I figured that if i had already logged in via oidc, then i could just start running terraform commands using the run step. however, the challenge comes into how terraform itself authenticates when you have a backend stored in an azure storage account. With microsoft and github both emphasising identity based access, using oidc for terraform deployments isn’t just secure. it will become the new norm. oidc authentication eliminates the need for storing long lived cloud secrets in your github repositories. Using terraform to connect github actions and aws with oidc typically, individuals utilize an api key secret key combination, which functions effectively. however, these long standing. The complete solution combines aws iam, github actions, and terraform to create a secure, automated pipeline that maintains security while enabling continuous deployment. A sample showing how to configure github workload identity federation (oidc) connection to azure with terraform and then use that configuration to deploy resources with terraform. This module allows you to create a github oidc provider and the associated iam roles, that will help github actions to securely authenticate against the aws api using an iam role.
Comments are closed.