Unit 4 Notes1 Pdf Cryptography Key Cryptography
Unit 2 Public Key Cryptography Pdf Unit 4 notes free download as pdf file (.pdf), text file (.txt) or read online for free. To preserve the integrity of the message, the message is passed through an algorithm called a cryptographic hash function. the function creates a compressed image of the message that can be used like a fingerprint. figure 11 shows the message, cryptographic hash function, and message digest.

Unit 4 Pdf Key Cryptography Computer File Public key encryption provides confidentiality but not authentication. the source (a) uses the public key ub of the destination (b) to encrypt m. because only b has the corresponding private key krb, only b can decrypt the message. thi some internal structure to the plaintext so that the receiver can distinguish between well fo. Self prepared notes. contribute to vineethchivukula cryptography development by creating an account on github. The early sections of this chapter, namely "a short history of cryptology,"principles of cryptography,” and "cryptography tools," provide some background on cryptology and general definitions of the key concepts of cryptography, and discuss the usage of common cryptographic tools. Symmetric key cryptography, where a single key is used for encryption and decryption, is comparatively efficient and faster than asymmetric key cryptography (public key cryptography).

Unit 4 Notes1 Pdf Cryptography Key Cryptography The early sections of this chapter, namely "a short history of cryptology,"principles of cryptography,” and "cryptography tools," provide some background on cryptology and general definitions of the key concepts of cryptography, and discuss the usage of common cryptographic tools. Symmetric key cryptography, where a single key is used for encryption and decryption, is comparatively efficient and faster than asymmetric key cryptography (public key cryptography). – finding the key by cryptanalysis can exploit statistical irregularities in the ciphertext. – to prevent cryptanalysis, the bit patterns characters in the ciphertext should have a uniform even distribution, that is, all bit patterns characters should be equally likely. A set of policies, processes, server platforms, software and workstations used for the purpose of administering certificates and public private key pairs, including the ability to issue, maintain, and revoke public key certificates. Obtain b’s public key securely. the directory entry for each ca includes two types of certificates: forward certificates: certificates of x generated by other cas reverse certificates: certificates generated by x that are the certificates of other cas. The key table is a 5×5 grid of alphabets that acts as the key for encrypting the plaintext. each of the 25 alphabets must be unique and one letter of the alphabet (usually j) is omitted from the table as we need only 25 alphabets instead of 26.
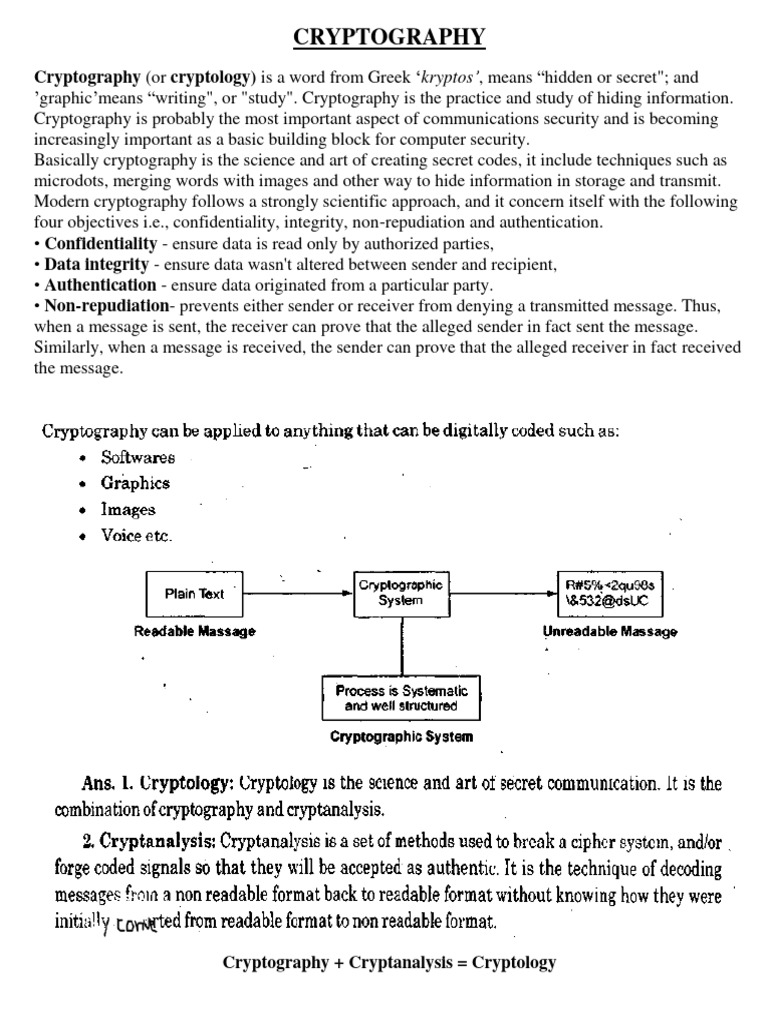
Unit 2 Part4 Pdf Public Key Cryptography Cryptography – finding the key by cryptanalysis can exploit statistical irregularities in the ciphertext. – to prevent cryptanalysis, the bit patterns characters in the ciphertext should have a uniform even distribution, that is, all bit patterns characters should be equally likely. A set of policies, processes, server platforms, software and workstations used for the purpose of administering certificates and public private key pairs, including the ability to issue, maintain, and revoke public key certificates. Obtain b’s public key securely. the directory entry for each ca includes two types of certificates: forward certificates: certificates of x generated by other cas reverse certificates: certificates generated by x that are the certificates of other cas. The key table is a 5×5 grid of alphabets that acts as the key for encrypting the plaintext. each of the 25 alphabets must be unique and one letter of the alphabet (usually j) is omitted from the table as we need only 25 alphabets instead of 26.

Unit 4 Cryptography Pdf Cryptography Cipher Obtain b’s public key securely. the directory entry for each ca includes two types of certificates: forward certificates: certificates of x generated by other cas reverse certificates: certificates generated by x that are the certificates of other cas. The key table is a 5×5 grid of alphabets that acts as the key for encrypting the plaintext. each of the 25 alphabets must be unique and one letter of the alphabet (usually j) is omitted from the table as we need only 25 alphabets instead of 26.
Comments are closed.