Unit 1 Classical Encryption Techniques Pdf Cryptanalysis
Classical Encryption Techniques Pdf Cryptography Cipher Unit 1 classical encryption techniques free download as pdf file (.pdf), text file (.txt) or read online for free. the document outlines the fundamentals of cryptography and cyber security, focusing on symmetric encryption, including definitions of plaintext, ciphertext, encryption, and decryption. A study of these techniques enables us to illustrate the basic approaches to symmetric encryption used today and the types of cryptanalytic attacks that must be anticipated.

Classical Encryption Techniques M Odeo Lecturer Pdf Public Key The simplest such cipher is the rail fence technique, in which the plaintext is written down as a sequence of diagonals and then read off as a sequence of rows. The document provides an overview of cryptography and cybersecurity fundamentals, focusing on symmetric encryption models, the processes of encryption and decryption, and various cipher techniques such as substitution and transposition. Given the algorithm and ciphertext, an attacker cannot obtain the key or plaintext. sender and receiver have knowledge of the secret key (and keep it secret). ciphertext does not contain enough information to derive plaintext or key (even if attacker had all the time in the world!) cipher: vhfxulwbdqgfubswrjudskd plain: ?. Selected letters of printed or typewritten text are overwritten in pencil. a number of substances can be used for writing but leave no visible. small pin punctures on selected letters are ordinarily not.
Unit 1 Classical Encryption Techniques Pdf Given the algorithm and ciphertext, an attacker cannot obtain the key or plaintext. sender and receiver have knowledge of the secret key (and keep it secret). ciphertext does not contain enough information to derive plaintext or key (even if attacker had all the time in the world!) cipher: vhfxulwbdqgfubswrjudskd plain: ?. Selected letters of printed or typewritten text are overwritten in pencil. a number of substances can be used for writing but leave no visible. small pin punctures on selected letters are ordinarily not. Objectives: the objectives of this unit is to present an overview of the main concepts of cryptography, understand the threats & attacks, understand ethical hacking. Encrypting and decrypting plaintext encrypted two letters at a time: if a pair is a repeated letter, insert a filler like 'x', eg. "balloon" encrypts as "ba lx lo on" if both letters fall in the same row, replace each with letter to right (wrapping back to start from end), eg. “ar" encrypts as "rm". Present an overview of the main concepts of symmetric cryptography. explain the difference between cryptanalysis and brute force attack. understand the operation of a monoalphabetic substitution cipher. understand the operation of a polyalphabetic cipher. present an overview of the hill cipher. The two types of attack on an encryption algorithm are cryptanalysis, based on properties of the encryption algorithm, and brute force, which involves trying all possible keys.
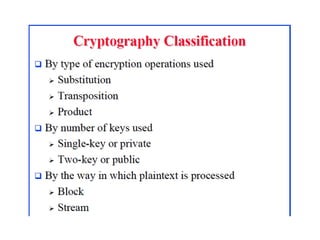
Classical Encryption Techniques Pdf Objectives: the objectives of this unit is to present an overview of the main concepts of cryptography, understand the threats & attacks, understand ethical hacking. Encrypting and decrypting plaintext encrypted two letters at a time: if a pair is a repeated letter, insert a filler like 'x', eg. "balloon" encrypts as "ba lx lo on" if both letters fall in the same row, replace each with letter to right (wrapping back to start from end), eg. “ar" encrypts as "rm". Present an overview of the main concepts of symmetric cryptography. explain the difference between cryptanalysis and brute force attack. understand the operation of a monoalphabetic substitution cipher. understand the operation of a polyalphabetic cipher. present an overview of the hill cipher. The two types of attack on an encryption algorithm are cryptanalysis, based on properties of the encryption algorithm, and brute force, which involves trying all possible keys.

Classical Cryptography Pdf Cipher Encryption Present an overview of the main concepts of symmetric cryptography. explain the difference between cryptanalysis and brute force attack. understand the operation of a monoalphabetic substitution cipher. understand the operation of a polyalphabetic cipher. present an overview of the hill cipher. The two types of attack on an encryption algorithm are cryptanalysis, based on properties of the encryption algorithm, and brute force, which involves trying all possible keys.
Comments are closed.