Unified Kill Chain Stop Cloud Attacks Across Every Stage

The Unified Kill Chain Pdf Security Cyberwarfare By breaking down the process of a cyberattack into in, through, and out, the ukc helps organizations increase their cyber resilience by stopping hacking attempts at multiple stages of an attack. The unified kill chain provides insights into the ordered arrangement of phases in attacks from their beginning to their completion, by uniting and extending existing models. the unified kill chain can be used to analyze, compare and defend against targeted and non targeted cyber attacks.

Unified Kill Chain Stop Cloud Attacks Across Every Stage Insider threats, supply chain compromises, cloud native attacks… these don’t fit the old perimeter focused model. this is where the unified kill chain comes in. this guide will teach you what it is, why it was created, and how it addresses the critical gaps left by its predecessor. Learn how the cyber kill chain helps you map controls, detect threats, and disrupt attacks across cloud and on prem environments. Master the cyber kill chain framework. learn all 7 stages, defense strategies, ai evolution, and how to break the chain in 2025. Cyber kill chain: originally created by lockheed martin, this model breaks down cyber attacks into stages like reconnaissance, weaponization, delivery, exploitation, installation, command and control, and actions on objectives.

Tryhackme Unified Kill Chain Master the cyber kill chain framework. learn all 7 stages, defense strategies, ai evolution, and how to break the chain in 2025. Cyber kill chain: originally created by lockheed martin, this model breaks down cyber attacks into stages like reconnaissance, weaponization, delivery, exploitation, installation, command and control, and actions on objectives. The unified kill chain (ukc) is a comprehensive framework designed to describe and analyze cyber attacks by mapping the entire lifecycle of an adversary’s operation. it merges key concepts from two popular models: the cyber kill chain (ckc) and mitre att&ck. Unlike the traditional 7 stage cyber kill chain, the unified kill chain includes 18 stages, grouped into three main phases: 1. initial foothold. 2. network propagation. 3. action on objectives. each phase connects attacker behavior with defensive detection opportunities. We will examine the elements of the unified kill chain in this post, as well as how it varies from previous models and why it is quickly becoming a vital resource for security teams across the globe. This comprehensive guide explores cti cyber kill chain integration across all phases, tools, real world examples, and 2026 best practices. enterprises adopting these strategies reduce mean time to detect (mttd) by up to 68% and fortify against advanced persistent threats (apts).
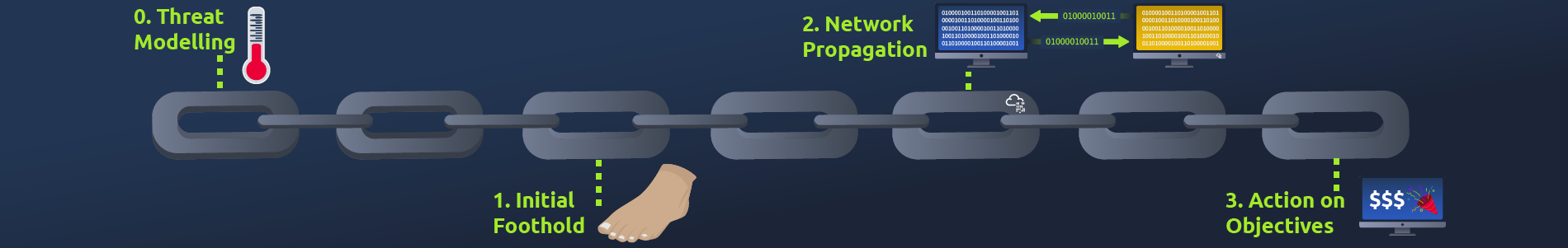
Tryhackme Unified Kill Chain The unified kill chain (ukc) is a comprehensive framework designed to describe and analyze cyber attacks by mapping the entire lifecycle of an adversary’s operation. it merges key concepts from two popular models: the cyber kill chain (ckc) and mitre att&ck. Unlike the traditional 7 stage cyber kill chain, the unified kill chain includes 18 stages, grouped into three main phases: 1. initial foothold. 2. network propagation. 3. action on objectives. each phase connects attacker behavior with defensive detection opportunities. We will examine the elements of the unified kill chain in this post, as well as how it varies from previous models and why it is quickly becoming a vital resource for security teams across the globe. This comprehensive guide explores cti cyber kill chain integration across all phases, tools, real world examples, and 2026 best practices. enterprises adopting these strategies reduce mean time to detect (mttd) by up to 68% and fortify against advanced persistent threats (apts).

Tryhackme Unified Kill Chain We will examine the elements of the unified kill chain in this post, as well as how it varies from previous models and why it is quickly becoming a vital resource for security teams across the globe. This comprehensive guide explores cti cyber kill chain integration across all phases, tools, real world examples, and 2026 best practices. enterprises adopting these strategies reduce mean time to detect (mttd) by up to 68% and fortify against advanced persistent threats (apts).
Comments are closed.