Understanding Vulnerability

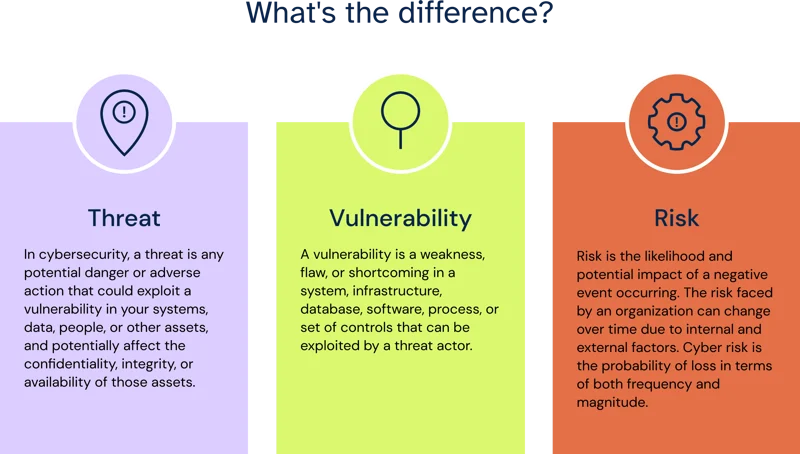
Understanding Vulnerability Vulnerability refers to the characteristics and circumstances of a community, system, or asset that make it susceptible to the damaging effects of a hazard. A vulnerability is a weakness in an it system that can be exploited by an attacker to deliver a successful attack. they can occur through flaws, features or user error, and attackers will look to.
Implementing A Risk Based Approach To Vulnerability Management Despite some divergence over the meaning of vulnerability, most experts agree that understanding vulnerability requires more than analysing the direct impacts of a hazard. This chapter draws on the vulnerability literature to present an overarching framework for the book. We provide a critical view on the evolution of vulnerability, tracing its shift from a static measure of an element’s capacity to be harmed by hazards, to a multifaceted, dynamic concept. we explore various vulnerability definitions, cross disciplinary approaches, models that integrate vulnerability, global patterns, and assessment tools. Vulnerability, especially the political vulnerability brought on by conflict, which can force people to flee their homes, can both cause and result in migration.
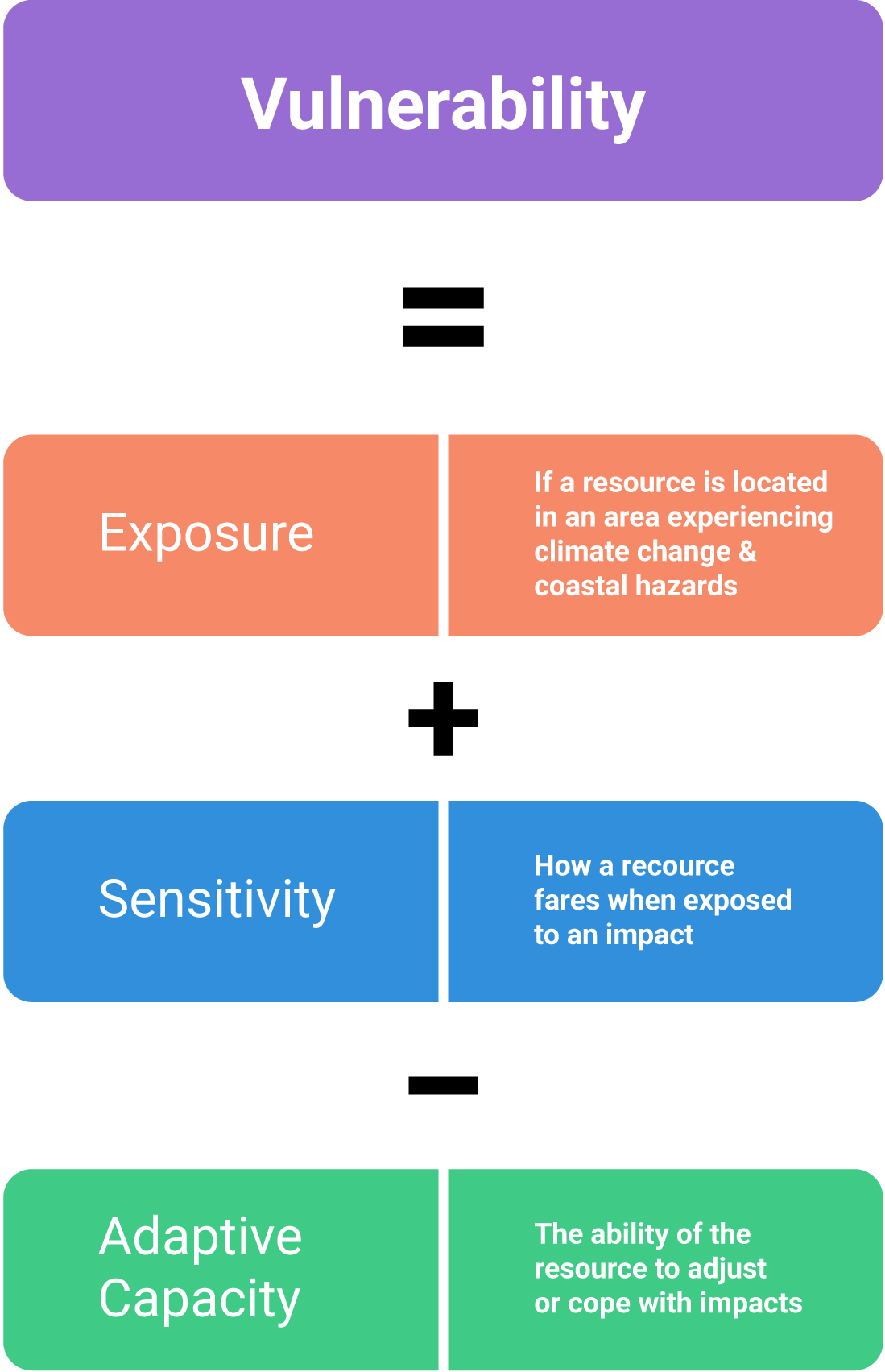
Module 2 The Basics Of Vulnerability And Climate Change Adaptation We provide a critical view on the evolution of vulnerability, tracing its shift from a static measure of an element’s capacity to be harmed by hazards, to a multifaceted, dynamic concept. we explore various vulnerability definitions, cross disciplinary approaches, models that integrate vulnerability, global patterns, and assessment tools. Vulnerability, especially the political vulnerability brought on by conflict, which can force people to flee their homes, can both cause and result in migration. Understanding vulnerability goes beyond identifying who might be at risk during disasters. it requires systematic frameworks that help us analyze why certain communities are vulnerable, how vulnerability manifests, and what can be done to reduce it. For cybersecurity professionals, understanding vulnerabilities isn't just academic; it’s the linchpin of keeping organizations safeguarded in an era of constant digital threat. this guide breaks down what vulnerabilities are, their different types, real world case studies, and actionable strategies to manage them. This article will answer the question “what is vulnerability?” in detail. it included sections on different types of vulnerabilities and more. Learn what vulnerability in cybersecurity, their types, causes, and how to detect and mitigate them. protect your systems with expert tips and authoritative resources.

Embracing Advanced Frameworks For Effective Vulnerability Management Understanding vulnerability goes beyond identifying who might be at risk during disasters. it requires systematic frameworks that help us analyze why certain communities are vulnerable, how vulnerability manifests, and what can be done to reduce it. For cybersecurity professionals, understanding vulnerabilities isn't just academic; it’s the linchpin of keeping organizations safeguarded in an era of constant digital threat. this guide breaks down what vulnerabilities are, their different types, real world case studies, and actionable strategies to manage them. This article will answer the question “what is vulnerability?” in detail. it included sections on different types of vulnerabilities and more. Learn what vulnerability in cybersecurity, their types, causes, and how to detect and mitigate them. protect your systems with expert tips and authoritative resources.
Comments are closed.