Understanding System Security Authentication Access Control Course
Authentication And Access Control Course Description V2 Pdf Access In this course, we will examine the business of controlling how our systems, services, resources and data can be safely accessed only by those authorized to do so. we will discuss authentication methods, trust, the identity management life cycle and access control models. Enroll in udacity's introduction to system security course and learn how to implement authentication and authorization as a means to protect access to data and services.

Access Control And Authentication Pdf This course provides a solid understanding of identity and access management concepts and real world application. the explanations are clear, the instructor is knowledgeable, and the examples make complex topics easy to grasp. Explore authentication methods, trust, identity management, and access control models to ensure secure system and data access for authorized users only. An access control system is a fundamental aspect of cybersecurity, granting and restricting access to different levels of users. learn about access controls with courses delivered through edx. Explore the essential differences between authentication and authorization in system design. learn how to implement strong user verification and access control using methods like multi factor authentication, token based systems, oauth, and access models such as rbac and abac.

Understanding System Security Authentication Access Control Course An access control system is a fundamental aspect of cybersecurity, granting and restricting access to different levels of users. learn about access controls with courses delivered through edx. Explore the essential differences between authentication and authorization in system design. learn how to implement strong user verification and access control using methods like multi factor authentication, token based systems, oauth, and access models such as rbac and abac. Learners will gain a solid understanding of different authentication techniques, from simple passwords to more advanced multi factor authentication. the course also sheds light on how trust is established and maintained in distributed systems, a crucial aspect of modern it infrastructure. Single sign on and associated technologies and protocols aim to reduce the proliferation of ids and passwords to better control the security of access control mechanisms. In this mooc, we learn rbac and abac access control to facilitate the specification and management of access policies. we learn examples of how rbac is supported by modern systems such as docker and aws iam. In information security, authentication and access control are two fundamental concepts that ensure that only authorized users have access to systems and data. in this chapter, we'll explore these two concepts in detail.

Security In Operating System Complete Guide To Access Control And Learners will gain a solid understanding of different authentication techniques, from simple passwords to more advanced multi factor authentication. the course also sheds light on how trust is established and maintained in distributed systems, a crucial aspect of modern it infrastructure. Single sign on and associated technologies and protocols aim to reduce the proliferation of ids and passwords to better control the security of access control mechanisms. In this mooc, we learn rbac and abac access control to facilitate the specification and management of access policies. we learn examples of how rbac is supported by modern systems such as docker and aws iam. In information security, authentication and access control are two fundamental concepts that ensure that only authorized users have access to systems and data. in this chapter, we'll explore these two concepts in detail.
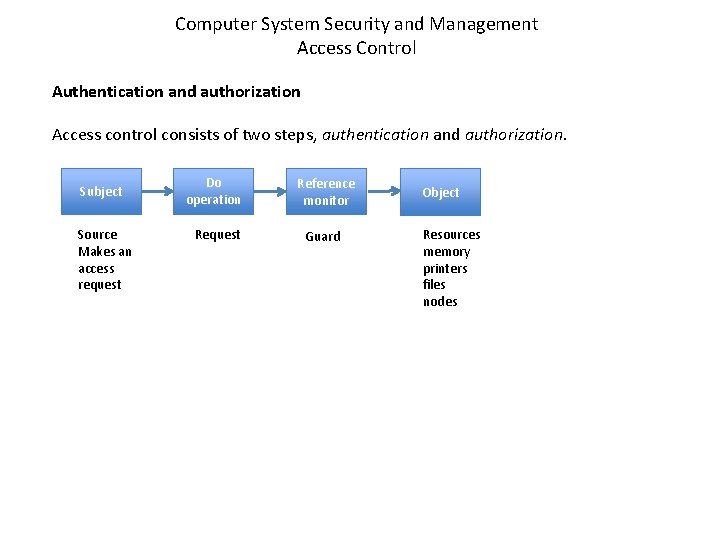
Computer System Security And Management Access Control Authentication In this mooc, we learn rbac and abac access control to facilitate the specification and management of access policies. we learn examples of how rbac is supported by modern systems such as docker and aws iam. In information security, authentication and access control are two fundamental concepts that ensure that only authorized users have access to systems and data. in this chapter, we'll explore these two concepts in detail.
Comments are closed.