Understanding Security Risks In Pdf Files
Understanding Security Threats And Risks Pdf Security Computer When recipients receive a pdf file, they often assume it’s a legitimate document, making them more likely to open it without suspicion. attackers leverage the familiarity of pdfs to conduct social engineering attacks. Discover the top cyber vulnerabilities in pdf files, real attack examples, and proven protection strategies to keep your documents and data secure.

Security Risk Management Seminar Pdf Risk Risk Assessment Can pdfs contain viruses? learn about pdf malware risks, javascript attacks, embedded files, and how to stay safe. Pdfs often slip past filters, look clean to antivirus tools, and don’t raise alarms until it’s too late. that’s why malicious pdfs have become one of the most effective entry points for attackers, and one of the hardest for analysts to spot early. Pdf files and attachments are often perceived as safe, but they are one of the most common channels for phishing and scam attacks. opening a single file can trigger malicious processes in the background. Explore how attackers hide malware in pdf annotations and embedded javascript to bypass security. learn attack examples, detection techniques, and defense strategies to protect your organization.

Identify Cybersecurity Risks Pdf Computer Security Security Pdf files and attachments are often perceived as safe, but they are one of the most common channels for phishing and scam attacks. opening a single file can trigger malicious processes in the background. Explore how attackers hide malware in pdf annotations and embedded javascript to bypass security. learn attack examples, detection techniques, and defense strategies to protect your organization. Learn about key security features in adobe acrobat pro for protecting pdf content and controlling access to sensitive information. Like other files that can come as attachments or links in an email, pdf files have received their fair share of attention from threat actors, too. in this post, we’ll take you on a tour of the technical aspects behind malicious pdf files: what they are, how they work, and how we can protect ourselves from them. Explore the hidden dangers in pdf files. learn how to detect, prevent, and remove embedded malware to protect your data. By understanding the typical attack vectors, adopting robust preventive controls, and maintaining vigilant user practices, individuals and organizations can markedly reduce the risk of a malware attack through pdfs.
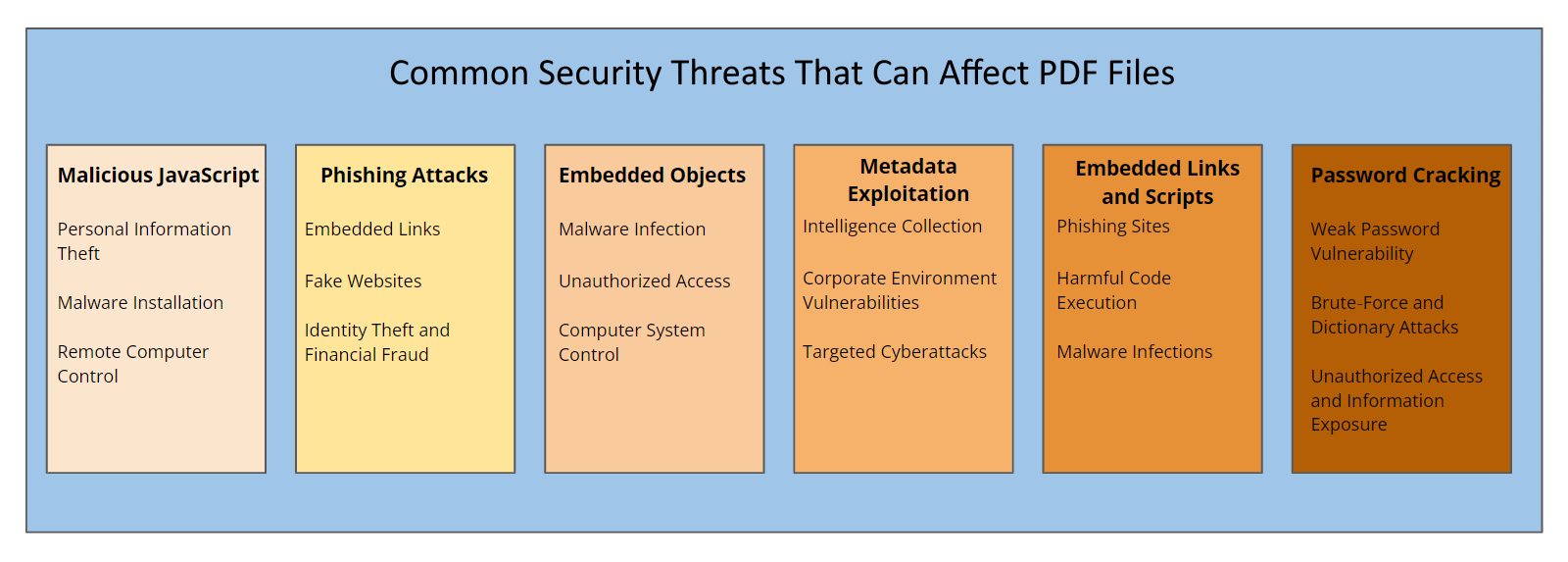
Essential Security Measures For Pdf Documents Learn about key security features in adobe acrobat pro for protecting pdf content and controlling access to sensitive information. Like other files that can come as attachments or links in an email, pdf files have received their fair share of attention from threat actors, too. in this post, we’ll take you on a tour of the technical aspects behind malicious pdf files: what they are, how they work, and how we can protect ourselves from them. Explore the hidden dangers in pdf files. learn how to detect, prevent, and remove embedded malware to protect your data. By understanding the typical attack vectors, adopting robust preventive controls, and maintaining vigilant user practices, individuals and organizations can markedly reduce the risk of a malware attack through pdfs.
Comments are closed.