Understanding Cryptanalytic Attacks Cryptography Fundamentals

Understanding Cryptography Pdf Cryptography Encryption This attacks are called cryptanalytic attacks. the attacks rely on nature of the algorithm and also knowledge of the general characteristics of the plaintext, i.e., plaintext can be a regular document written in english or it can be a code written in java. In this section, we'll explore various cryptographic attacks that hackers use to breach security, along with the cryptanalysis methods that make these attacks possible.
Chapter Two Fundamentals Of Cryptography Pdf Cryptography Cryptanalysis and attacks form the backbone of understanding cybersecurity vulnerabilities. this unit covers key concepts, historical context, and various attack types, from brute force to side channel attacks. Researchers may create attack strategies that fully overcome an encryption method, making it possible to decrypt ciphertext that has been encrypted using that algorithm without requiring the encryption key. Learn the fundamentals of cryptanalysis, its importance in cryptography, and the different types of attacks used to compromise secure data. In this article we will enrich our understanding of how cryptanalysis attacks are classified and how they stack up against each other in terms of evidencing a particular encryption scheme's resilience.

Cryptography 1 Ciphers And Fundamentals Pdf Key Cryptography Learn the fundamentals of cryptanalysis, its importance in cryptography, and the different types of attacks used to compromise secure data. In this article we will enrich our understanding of how cryptanalysis attacks are classified and how they stack up against each other in terms of evidencing a particular encryption scheme's resilience. In this discussion, we will explore various cryptanalysis methods, how attackers leverage them, and the different cryptographic attacks commonly employed. understanding these approaches is crucial for cybersecurity professionals aiming to build stronger defenses and anticipate emerging threats. Classification of cryptanalytics attacks this section discusses the types of attacks against cipher algorithms, cryptographic keys, authentication protocols, systems themselves, and hardware attacks. Timing. a timing attack is a type of side channel attack where we analyse the amount of time it takes a processor to execute encryption and decryption operations. if we are precise enough with our measurements, we can determine the contents of those operations. This document discusses various types of attacks on cryptosystems, including cryptanalytic attacks and implementation attacks. it describes ciphertext only attacks, known plaintext attacks, chosen plaintext attacks, and chosen ciphertext attacks.

Cryptanalytic Attacks And Cryptography Lifecycle Mrcissp In this discussion, we will explore various cryptanalysis methods, how attackers leverage them, and the different cryptographic attacks commonly employed. understanding these approaches is crucial for cybersecurity professionals aiming to build stronger defenses and anticipate emerging threats. Classification of cryptanalytics attacks this section discusses the types of attacks against cipher algorithms, cryptographic keys, authentication protocols, systems themselves, and hardware attacks. Timing. a timing attack is a type of side channel attack where we analyse the amount of time it takes a processor to execute encryption and decryption operations. if we are precise enough with our measurements, we can determine the contents of those operations. This document discusses various types of attacks on cryptosystems, including cryptanalytic attacks and implementation attacks. it describes ciphertext only attacks, known plaintext attacks, chosen plaintext attacks, and chosen ciphertext attacks.
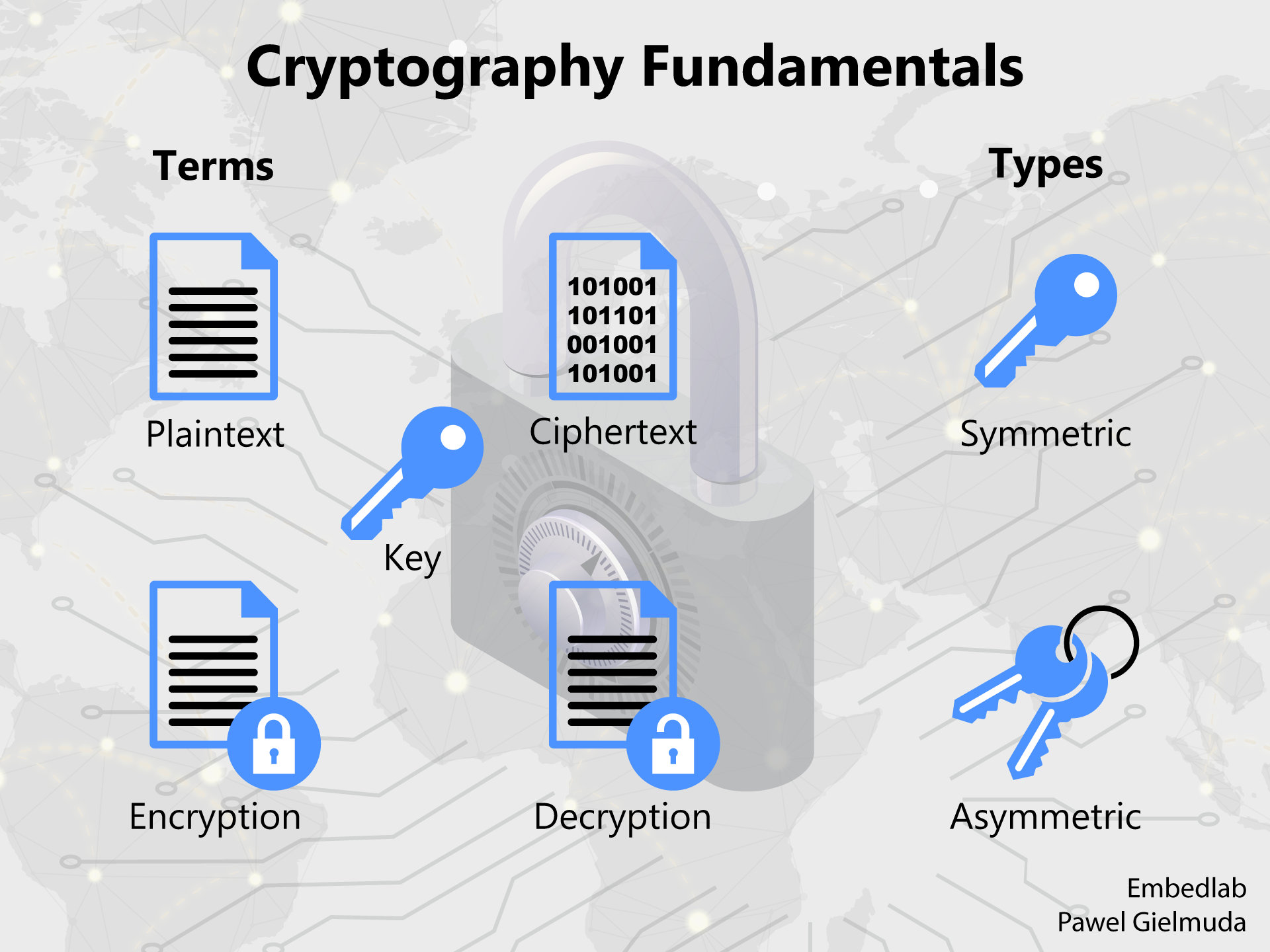
Cryptography Fundamentals Paka Team Timing. a timing attack is a type of side channel attack where we analyse the amount of time it takes a processor to execute encryption and decryption operations. if we are precise enough with our measurements, we can determine the contents of those operations. This document discusses various types of attacks on cryptosystems, including cryptanalytic attacks and implementation attacks. it describes ciphertext only attacks, known plaintext attacks, chosen plaintext attacks, and chosen ciphertext attacks.
Comments are closed.