Understanding A Malwares On Demand Polymorphic Code

Protect Your Business From Polymorphic Metamorphic Malware This article provides a comprehensive guide to understanding and combating polymorphic malware. it begins by defining polymorphic malware and its evolution from early encrypted viruses to. Discover what polymorphic malware is, how it evades detection, examples, challenges & how to prevent polymorphic viruses in your systems with manageengine.
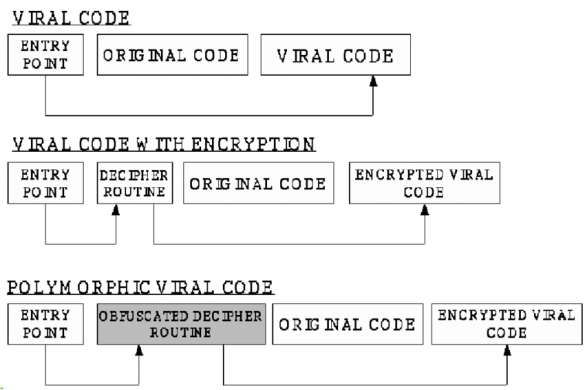
Polymorphic Code Various Kinds Of Polymorphism Ctr 2020 Polymorphic malware is a type of malicious software that changes its code and signature every time it replicates or infects a new system. it uses an encryption key to modify its appearance while maintaining the same core functions. What is polymorphic ai malware? polymorphic ai malware refers to a new class of malicious software. it leverages artificial intelligence models, such as gpt based language models, to dynamically generate, obfuscate, or modify its own code at runtime or build time. Polymorphic malware is a type of malicious software that constantly changes its code to evade detection by traditional antivirus or security software. it achieves this by altering its appearance while maintaining its core functionality. The methods currently used to analyse polymorphic malware are thoroughly reviewed in this survey, with an emphasis on their advantages, disadvantages, and room for development.
What Is Polymorphic Code Undetectable Malware Evolution Polymorphic malware is a type of malicious software that constantly changes its code to evade detection by traditional antivirus or security software. it achieves this by altering its appearance while maintaining its core functionality. The methods currently used to analyse polymorphic malware are thoroughly reviewed in this survey, with an emphasis on their advantages, disadvantages, and room for development. In response to the evolution of second generation malwares, adept at circumventing traditional detection techniques, there has been an imperative and ever growing demand of advanced solutions for effective malware detection. this comprehensive review assesses and. Polymorphic malware is a type of malicious software that can change its code structure while maintaining its core functionality. the term “polymorphic” comes from the greek words “poly” (many) and “morph” (form), literally meaning “many forms.”. Polymorphic code is malware that continuously mutates its own binary structure while keeping its malicious function intact. think of it like this: the payload does the same evil thing every time. Discover how polymorphic viruses mutate to evade detection, real world examples, and how to detect and prevent these evolving malware threats.

Polymorphic Malware 101 Managed It And Cybersecurity Services For In response to the evolution of second generation malwares, adept at circumventing traditional detection techniques, there has been an imperative and ever growing demand of advanced solutions for effective malware detection. this comprehensive review assesses and. Polymorphic malware is a type of malicious software that can change its code structure while maintaining its core functionality. the term “polymorphic” comes from the greek words “poly” (many) and “morph” (form), literally meaning “many forms.”. Polymorphic code is malware that continuously mutates its own binary structure while keeping its malicious function intact. think of it like this: the payload does the same evil thing every time. Discover how polymorphic viruses mutate to evade detection, real world examples, and how to detect and prevent these evolving malware threats.
Comments are closed.