Unauthorized Data Interception Pdf

Unauthorized Data Interception Pdf Unauthorized data interception free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. explanation and more details about this cyber crime. This study examines technology solutions, personnel training, and policy enforcement as methods to prevent unauthorized data access.

Gsm Interception Pdf Gsm Telecommunications Standards In the event of a data breach, data confidentiality can be compromised via unauthorized exfiltration, leaking, or spills of data to unauthorized parties, including the general public. it is essential for an organization to identify and protect assets to prevent breaches. While not clear whether this pertains to data, it is argued that by intercepting a computer, the resulting effect is the automatic interception of data, whether intentional or otherwise. Where a state party due to limitations in its legislation in force at the time of the adoption of this convention, is not able to apply the measures referred to in article (real time collection of data) and article (interception of content data) to communications being transmitted within a computer system of a service provider, which system:. A person commits the criminal offense of interference with computer data when he or she damages, deletes, deteriorates, alters, or suppresses com puter data without right.

Wifi Interception Sp23 Pdf Internet Protocols Computer Network Where a state party due to limitations in its legislation in force at the time of the adoption of this convention, is not able to apply the measures referred to in article (real time collection of data) and article (interception of content data) to communications being transmitted within a computer system of a service provider, which system:. A person commits the criminal offense of interference with computer data when he or she damages, deletes, deteriorates, alters, or suppresses com puter data without right. A threat action whereby an unauthorized entity indirectly accesses sensitive data (but not necessarily the data contained in the communication) by reasoning from characteristics or byproducts of communications. In this chapter we consider the next layer of vulnerability: when the data leaves the computer and is communicated to others. the unauthorised uses to which such information may be put are as varied as the communications themselves, but include harassment, extortion, fraud or economic espionage. Unauthorized data access (uda) by an internal employee is a major threat to an organization. regardless of whether the individuals engaged in uda with malicious intent or not, real time identification of uda events and anomalous behaviors is extremely difficult. Kasus unauthorized access yang cukup mengguncang adalah insiden kebocoran d ata bpjs kesehatan pada mei 2021, yang mengakibatkan bocornya data pribadi sekitar 279 juta penduduk indonesia.
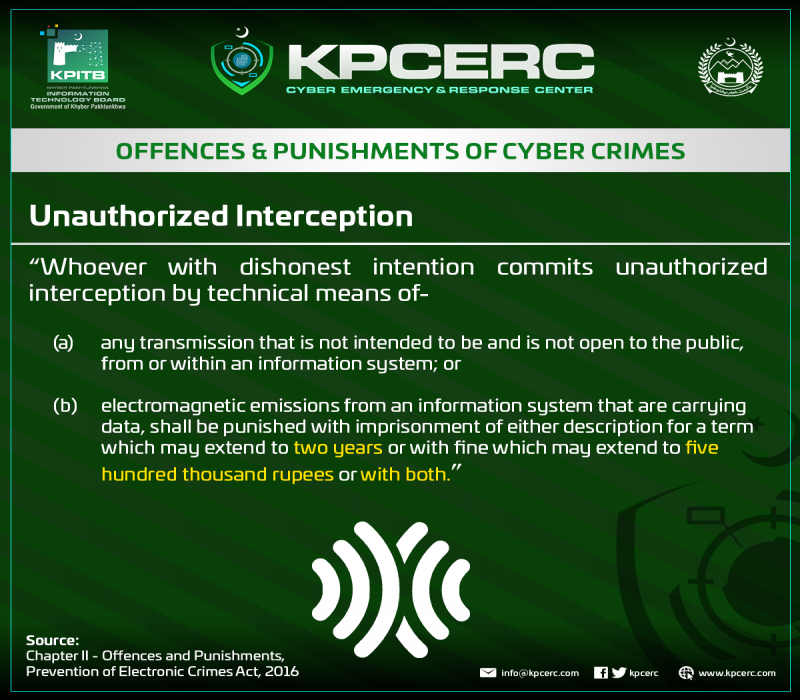
Unauthorized Interception Kpcerc A threat action whereby an unauthorized entity indirectly accesses sensitive data (but not necessarily the data contained in the communication) by reasoning from characteristics or byproducts of communications. In this chapter we consider the next layer of vulnerability: when the data leaves the computer and is communicated to others. the unauthorised uses to which such information may be put are as varied as the communications themselves, but include harassment, extortion, fraud or economic espionage. Unauthorized data access (uda) by an internal employee is a major threat to an organization. regardless of whether the individuals engaged in uda with malicious intent or not, real time identification of uda events and anomalous behaviors is extremely difficult. Kasus unauthorized access yang cukup mengguncang adalah insiden kebocoran d ata bpjs kesehatan pada mei 2021, yang mengakibatkan bocornya data pribadi sekitar 279 juta penduduk indonesia.
Data Interception Protection Dr Jonathan Francis Roscoe Unauthorized data access (uda) by an internal employee is a major threat to an organization. regardless of whether the individuals engaged in uda with malicious intent or not, real time identification of uda events and anomalous behaviors is extremely difficult. Kasus unauthorized access yang cukup mengguncang adalah insiden kebocoran d ata bpjs kesehatan pada mei 2021, yang mengakibatkan bocornya data pribadi sekitar 279 juta penduduk indonesia.

What Is Data Interception And Theft Definition And Meaning Stellastra
Comments are closed.