Unauthenticated Vs Unencrypted Protocols In Ot

Guarding The Gates Strategies To Secure Unencrypted Ot Protocols Audio tracks for some languages were automatically generated. learn more. As cyberattacks targeting ot environments grow more sophisticated, securing these unencrypted protocols has never been more urgent. in this article, we’ll explore the key strategies for protecting ot systems without disrupting their core operations.

Guarding The Gates Strategies To Secure Unencrypted Ot Protocols Unsecured ot protocols are a goldmine for attackers. while encryption adds overhead, the risks of unencrypted traffic—sabotage, espionage, or physical damage—far outweigh the costs. As the convergence of it and ot networks continues and cyber threats evolve, there is a growing recognition of the need to enhance security measures, including encryption, in ot environments. however, implementing these changes requires careful consideration to avoid disrupting critical operations. to encrypt or not to encrypt. The combination of all four, maintained through operational discipline, is what produces a defensible ot network despite the inherent insecurity of the protocols it carries. All comments are subject to release under the freedom of information act (foia). this document provides guidance on how to secure operational technology (ot) while addressing their unique performance, reliability, and safety requirements.

Ot Protocols Ot Protocols Ot Protocolspptx Pptx The combination of all four, maintained through operational discipline, is what produces a defensible ot network despite the inherent insecurity of the protocols it carries. All comments are subject to release under the freedom of information act (foia). this document provides guidance on how to secure operational technology (ot) while addressing their unique performance, reliability, and safety requirements. The report focuses on the gap between what secure protocols can technically provide and what operators can realistically deploy and maintain across ot environments. For years, ot security professionals have said, “it and ot are different.” in it, a breach results in data loss. in ot, it results in production outages, safety incidents, and sometimes. Based on interviews with ot asset owners and operators, cisa found strong demand for secure, authenticated communications but persistent barriers tied to cost, complexity, and legacy design of industrial protocols. But ot communication is traditionally unauthenticated, and protocols are unencrypted in transit. there is a great deal of potential to employ encryption in ot protocols like secure modbus, open platform communication unified architecture (opc ua), and generic object oriented substation event (goose).
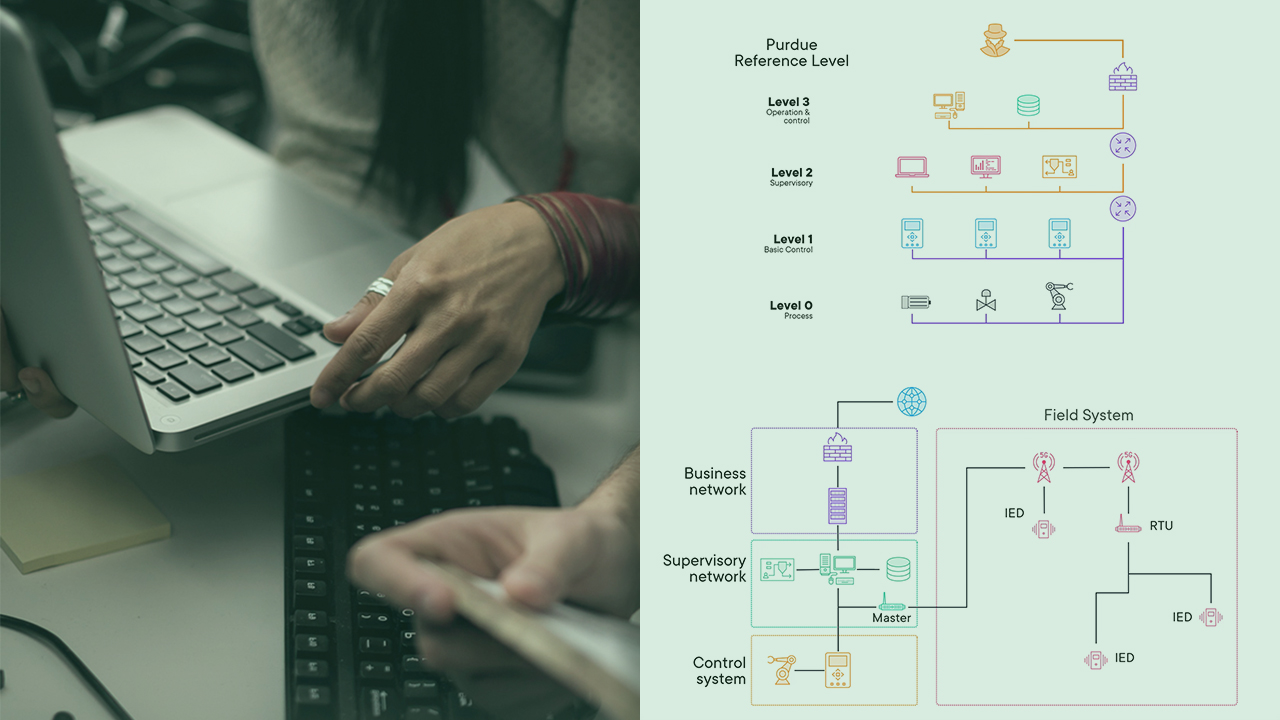
Fundamentals Of Ot Protocols The report focuses on the gap between what secure protocols can technically provide and what operators can realistically deploy and maintain across ot environments. For years, ot security professionals have said, “it and ot are different.” in it, a breach results in data loss. in ot, it results in production outages, safety incidents, and sometimes. Based on interviews with ot asset owners and operators, cisa found strong demand for secure, authenticated communications but persistent barriers tied to cost, complexity, and legacy design of industrial protocols. But ot communication is traditionally unauthenticated, and protocols are unencrypted in transit. there is a great deal of potential to employ encryption in ot protocols like secure modbus, open platform communication unified architecture (opc ua), and generic object oriented substation event (goose).

Ot Protocols Ppt Based on interviews with ot asset owners and operators, cisa found strong demand for secure, authenticated communications but persistent barriers tied to cost, complexity, and legacy design of industrial protocols. But ot communication is traditionally unauthenticated, and protocols are unencrypted in transit. there is a great deal of potential to employ encryption in ot protocols like secure modbus, open platform communication unified architecture (opc ua), and generic object oriented substation event (goose).
Comments are closed.