Two Factor Auth And Dynamic Forms

Two Factor Auth And Dynamic Forms Organizations that implement 2fa on sensitive forms can improve security, protect sensitive data, and enhance the user experience. with octo forms you can set your dynamic forms to ask for two factor authentication for every form you require extra security on. Learn how to implement two factor authentication (2fa) for customer identity in ciam systems. discover best practices, security tips, and strategies for large userbase companies.
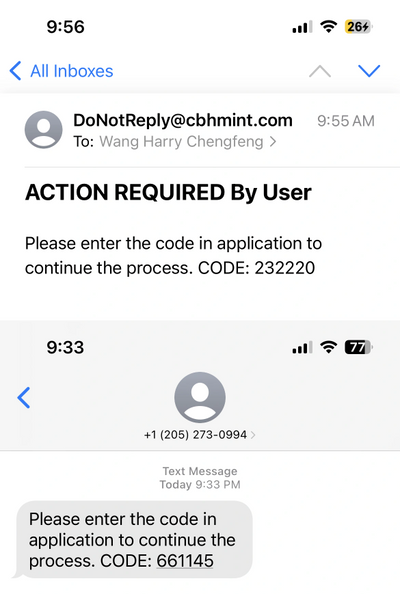
Two Factor Auth Api Totp reduces the risk of unauthorised access by generating temporary codes that expire after a certain time. to avoid user irritation and abandonment, the research emphasises the need to balance. Learn how to design secure, user friendly two factor authentication (2fa) systems. compare methods, user flows, recovery options, and future trends. Learn about different types of two factor authentication and the pros and cons of each. Two factor authentication (2fa) is presented as a practical and widely adopted method to improve access security. the article breaks down how it works, the types of authentication factors involved, and its role in reducing threats like phishing.

Two Factor Auth Learn To Read Coding Learning Learn about different types of two factor authentication and the pros and cons of each. Two factor authentication (2fa) is presented as a practical and widely adopted method to improve access security. the article breaks down how it works, the types of authentication factors involved, and its role in reducing threats like phishing. The two factor authentication technique was based on static password derived by the user and a dynamic password. in this technique, the user provides their personal details such as username, email address and phone numbers to serve as their password. Two factor authentication operates on the principle of combining two distinct factors to verify a user’s identity: something you know: a password or pin. something you have: a dynamically. 2fa is a security protocol that mandates the use of two separate forms of identification for gaining access to a particular resource or system. 2fa falls under the broader category of multi factor authentication (mfa) and enhances access security by necessitating two distinct authentication factors to validate your identity. Secure web apps with 2fa! learn to implement two factor authentication using otp, authenticator apps, and best practices for enhanced security and user trust.
Github Nexmo Community Two Factor Auth 2fa Example Using Java Spark The two factor authentication technique was based on static password derived by the user and a dynamic password. in this technique, the user provides their personal details such as username, email address and phone numbers to serve as their password. Two factor authentication operates on the principle of combining two distinct factors to verify a user’s identity: something you know: a password or pin. something you have: a dynamically. 2fa is a security protocol that mandates the use of two separate forms of identification for gaining access to a particular resource or system. 2fa falls under the broader category of multi factor authentication (mfa) and enhances access security by necessitating two distinct authentication factors to validate your identity. Secure web apps with 2fa! learn to implement two factor authentication using otp, authenticator apps, and best practices for enhanced security and user trust.
Comments are closed.