Tutorial Get Started With Threatsync

Threatsync By Watchguard Youtube In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint. This topic describes the general steps to set up and configure threatsync in watchguard cloud.

Tutorial Get Started With Threatsync Youtube This video tutorial will help you get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and security products. In this video tutorial, you’ll learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr). In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint security products, in particular, we will show you. In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint security products.

Xdr Dolos In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint security products, in particular, we will show you. In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint security products. In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint. For information about how to get started with threatsync, go to: this topic describes the threatsync service in watchguard cloud. In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint security products, in particular, we will show you:. Threatsync ndr is a cloud based, network centric threat detection and response solution that helps organizations identify, detect, and respond to network based cyberattacks through an advanced, layered approach.
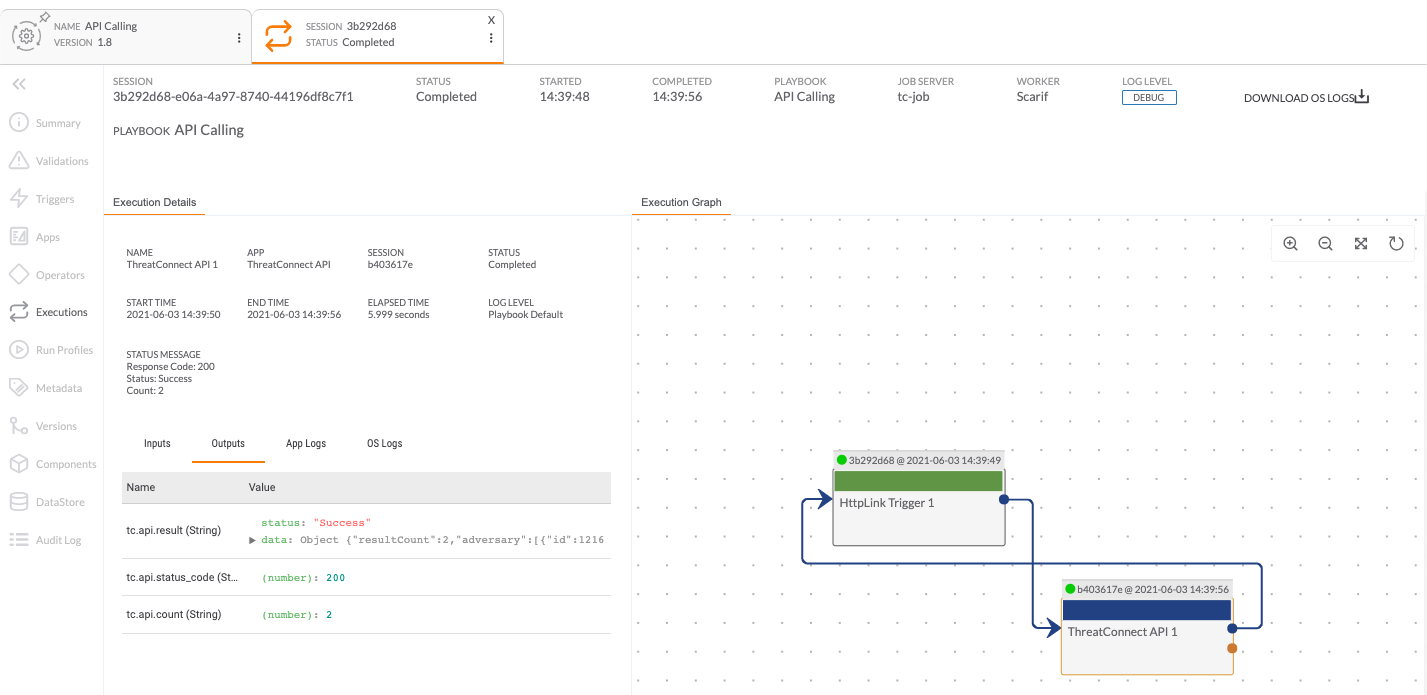
Settings Knowledge Base Article Threatconnect In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint. For information about how to get started with threatsync, go to: this topic describes the threatsync service in watchguard cloud. In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint security products, in particular, we will show you:. Threatsync ndr is a cloud based, network centric threat detection and response solution that helps organizations identify, detect, and respond to network based cyberattacks through an advanced, layered approach.

Product And Support News Watchguard Technologies In this video, you will learn how to get started with threatsync, a watchguard cloud service that provides extended detection and response (xdr) technology for watchguard network and endpoint security products, in particular, we will show you:. Threatsync ndr is a cloud based, network centric threat detection and response solution that helps organizations identify, detect, and respond to network based cyberattacks through an advanced, layered approach.
Comments are closed.