Tryhackme Owasp Api Security Top 10 2
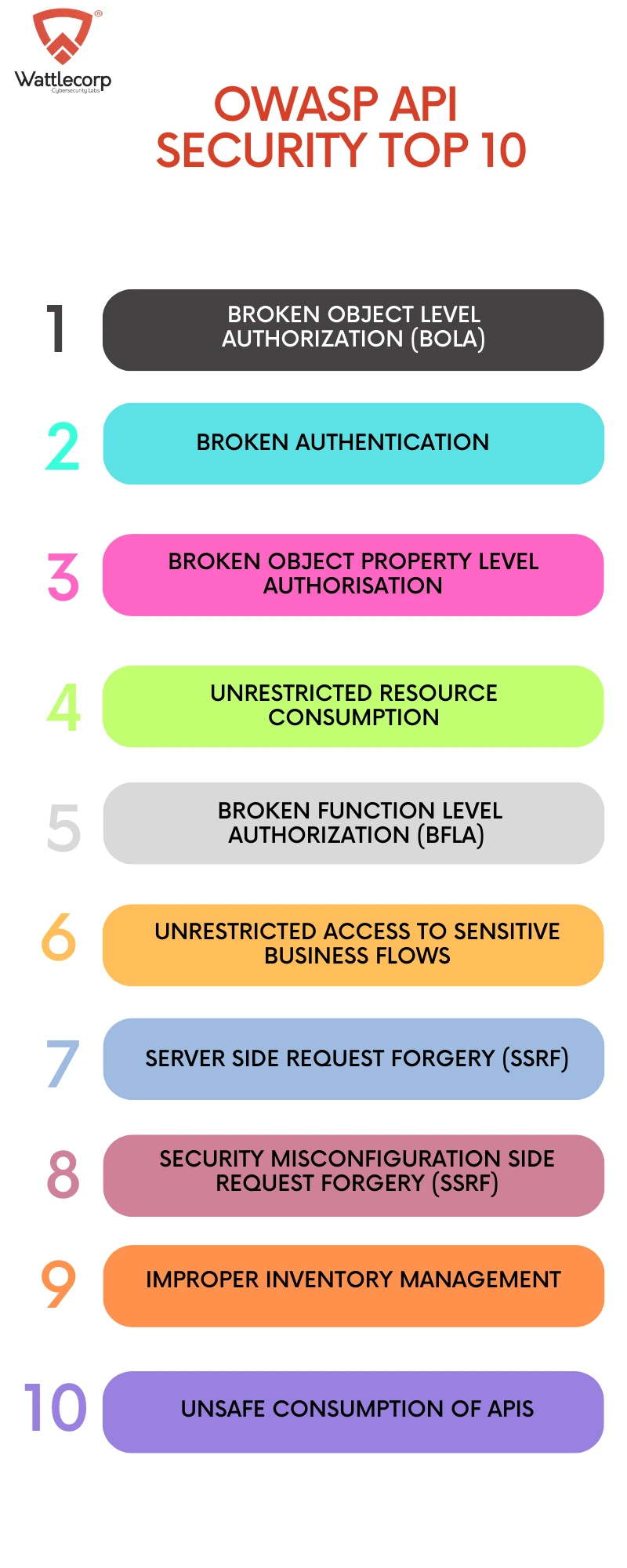
Owasp Api Security Top 10 Wattlecorp Cybersecurity Labs A large portion of the owasp api security top 10 focuses on authorization authentication and security misconfigurations. these areas remain the most common reasons apis are compromised in. Ready to learn cyber security? the owasp api security top 10 2 room is only available for premium users. signup now to access more than 500 free rooms and learn cyber security through a fun, interactive learning environment.
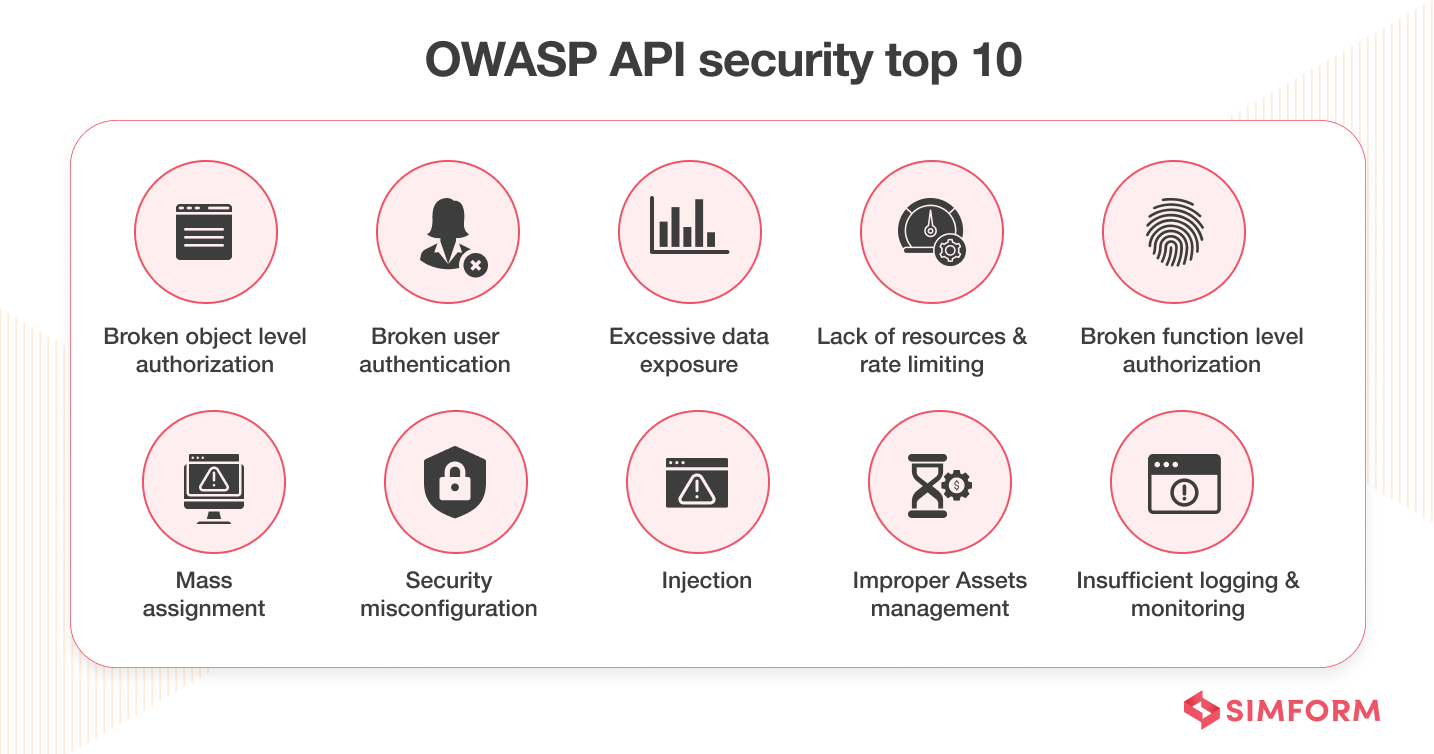
Api Security Best Practices To Protect Data The owasp api security top 10 – 2 is a subscriber only room which part of the security engineer learning path from tryhackme. the room is available at: tryhackme r room owaspapisecuritytop10d0. Most commonly, api systems are hacked because of failure in authorisation and authentication mechanisms and security misconfigurations. in a nutshell, api developers must safeguard apis in line. While the code is focused, press alt f1 for a menu of operations. contribute to thmrevenant tryhackme development by creating an account on github. The objective is to understand how these issues arise in real world apis, exploit them in a controlled lab environment, and learn how to mitigate them effectively.
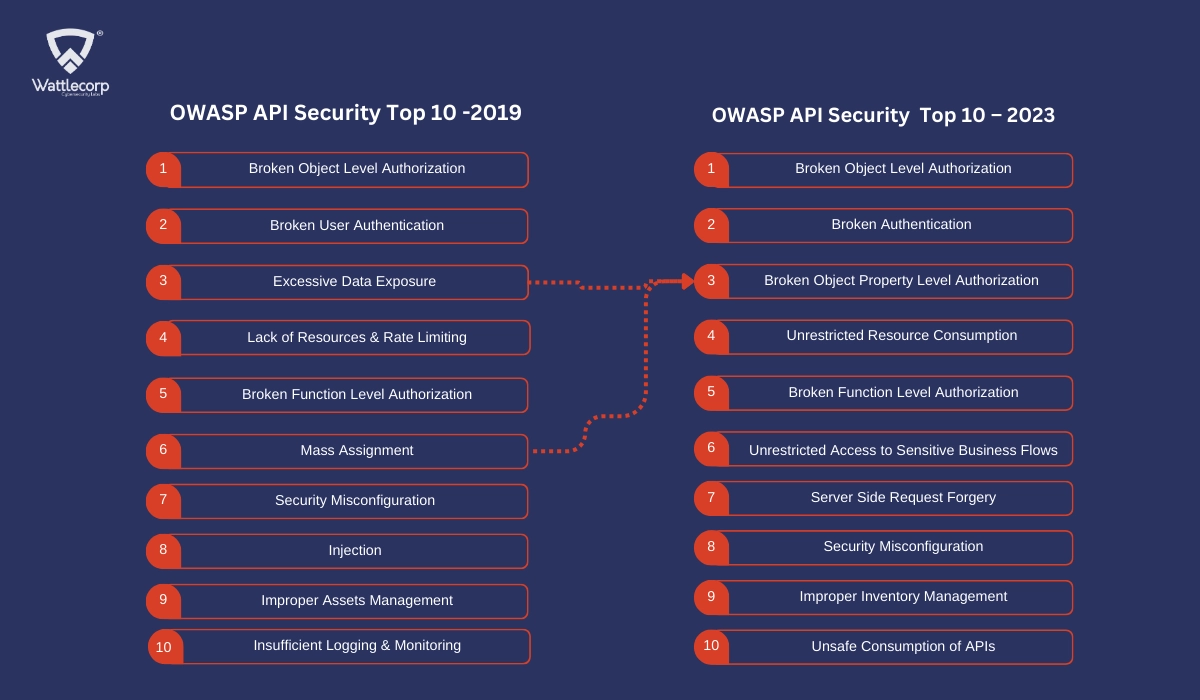
Owasp Api Security Top 10 Wattlecorp Cybersecurity Labs While the code is focused, press alt f1 for a menu of operations. contribute to thmrevenant tryhackme development by creating an account on github. The objective is to understand how these issues arise in real world apis, exploit them in a controlled lab environment, and learn how to mitigate them effectively. The owasp api security top 10 is a standard awareness document for developers and security professionals that identifies the most critical security risks specifically facing application. Owasp api security top 10–2 tl;dr walkthrough of tryhackme’s owasp api security top 10 part 2 room. a full list of our tryhackme walkthroughs and cheatsheets is here. In order to facilitate this goal, the owasp api security project will create and maintain a top 10 api security risks document, as well as a documentation portal for best practices when creating or assessing apis. In the previous room, we studied the first five principles of owasp api security. now in this room, we will briefly discuss the remaining principles and their potential impact and mitigation measures.
Comments are closed.