Owasp Api Security Top10 2 Tryhackme Walkthrough

Tryhackme Owasp Api Security Top 10 2 Secure api development requires continuous attention to authentication authorization and configuration. by applying best practices and learning from owasp guidelines developers can. Learn the basic concepts for secure api development (part 2).
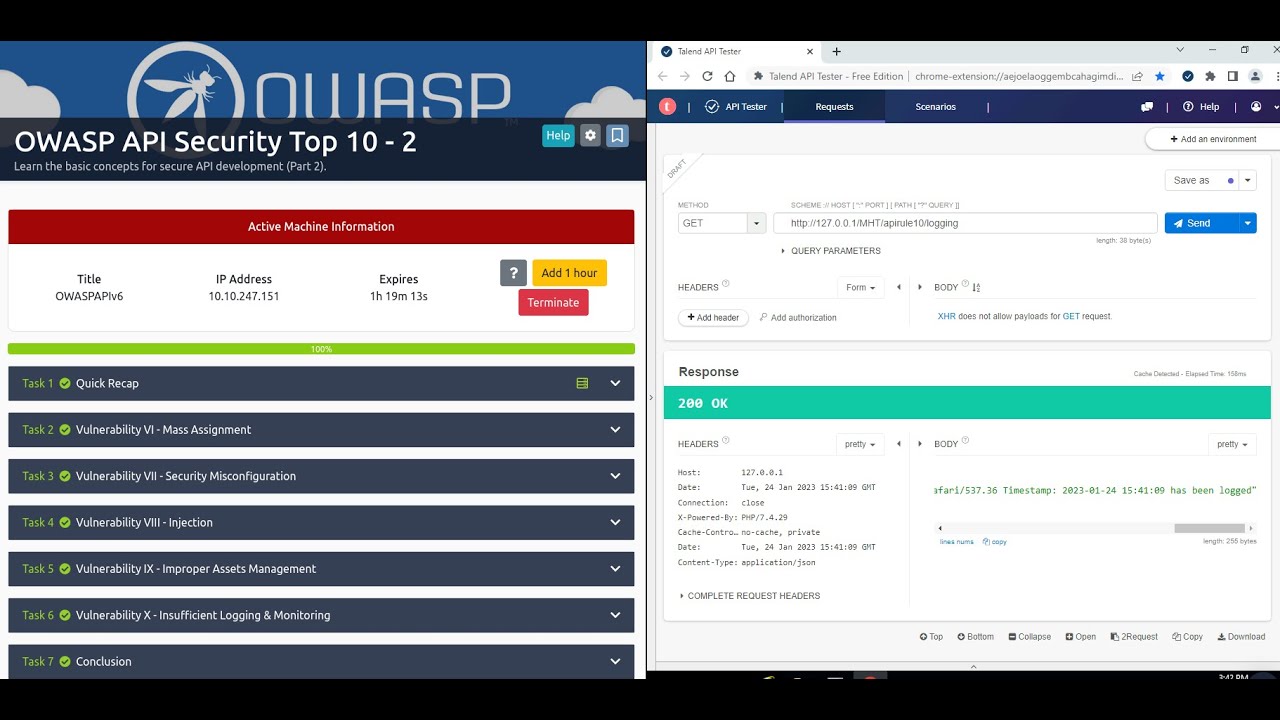
Tryhackme Owasp Api Security Top 10 2 Answers for the tryhackme owasp api security top 10 – 2 room the owasp api security top 10 – 2 is a subscriber only room which part of the security engineer learning path from tryhackme. Learn the basic concepts for secure api development (part 2). tryhackme room owaspapisecuritytop10d0. Explore the owasp top 10 in this detailed tryhackme walkthrough by jasper, covering critical web security vulnerabilities. Jobskillshare community 2.1k [walkthroughs] tryhackme room "owasp api security top 10 1" writeup cyberwar 770.
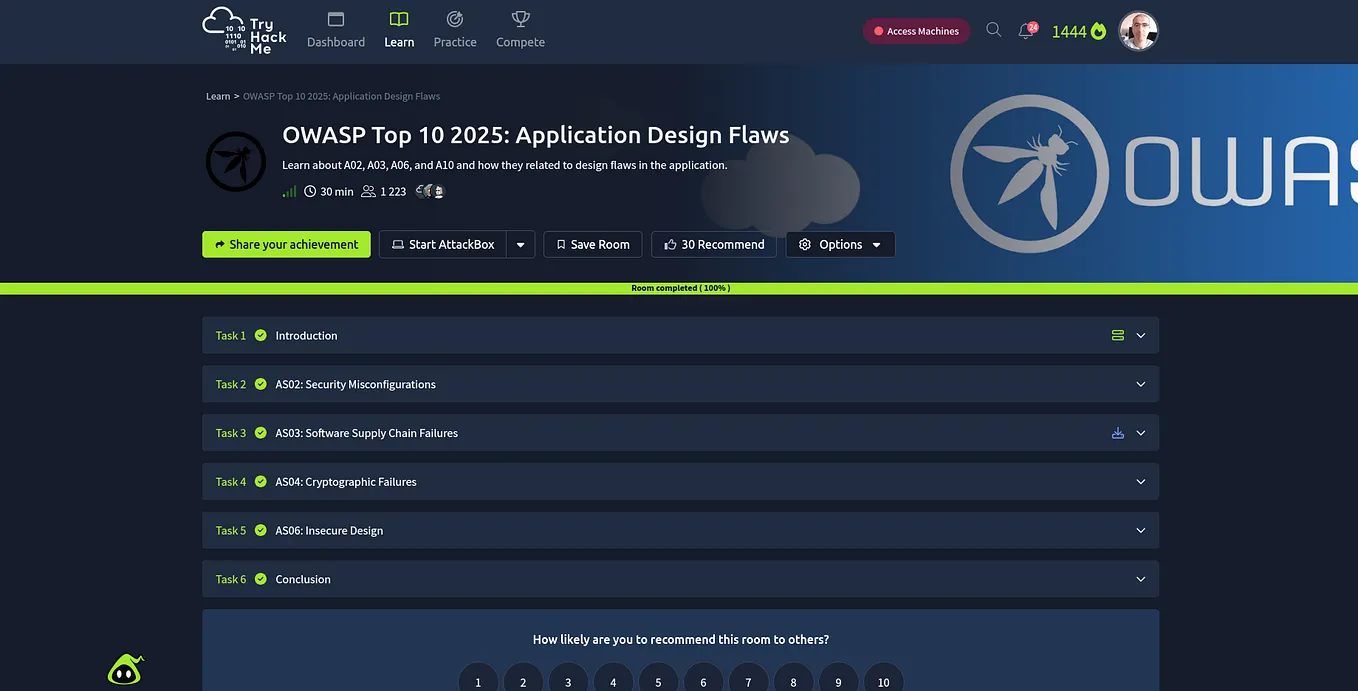
Owasp Api Security Top 10 1 Tryhackme Walkthrough By Rich Medium Explore the owasp top 10 in this detailed tryhackme walkthrough by jasper, covering critical web security vulnerabilities. Jobskillshare community 2.1k [walkthroughs] tryhackme room "owasp api security top 10 1" writeup cyberwar 770. Most commonly, api systems are hacked because of failure in authorisation and authentication mechanisms and security misconfigurations. in a nutshell, api developers must safeguard apis in line. Now that we understand the threat and the damage caused due to non adherence to mitigation measures — let’s discuss developing a secure api through owasp api security top 10 principles. In the previous room, we studied the first five principles of owasp api security. now in this room, we will briefly discuss the remaining principles and their potential impact and mitigation measures. 🛡️ owasp api top 10 — tryhackme walkthrough (part 2) hands on exploitation and mitigation of advanced api vulnerabilities with real world scenarios. 🔗 references & previous part before ….

Owasp Api Security Top 10 2 Tryhackme Walkthrough By Yogesh Mishra Most commonly, api systems are hacked because of failure in authorisation and authentication mechanisms and security misconfigurations. in a nutshell, api developers must safeguard apis in line. Now that we understand the threat and the damage caused due to non adherence to mitigation measures — let’s discuss developing a secure api through owasp api security top 10 principles. In the previous room, we studied the first five principles of owasp api security. now in this room, we will briefly discuss the remaining principles and their potential impact and mitigation measures. 🛡️ owasp api top 10 — tryhackme walkthrough (part 2) hands on exploitation and mitigation of advanced api vulnerabilities with real world scenarios. 🔗 references & previous part before ….

Tryhackme Owasp Api Security Top 10 2 Walkthrough By Sonia Garcia In the previous room, we studied the first five principles of owasp api security. now in this room, we will briefly discuss the remaining principles and their potential impact and mitigation measures. 🛡️ owasp api top 10 — tryhackme walkthrough (part 2) hands on exploitation and mitigation of advanced api vulnerabilities with real world scenarios. 🔗 references & previous part before ….

Tryhackme Owasp Api Security Top 10 2 Walkthrough By Sonia Garcia
Comments are closed.