Tryhackme Cryptography Hashing Crypto101 Walkthrough By

Tryhackme Hashing And Cryptography 101 Tryhackme Hashing Crypto 101 A large part of ensuring that this communication is secure is done using cryptographic primitives. this module will explore core cryptographic topics that are used to secure communication over the internet and in machines servers. Hash functions are quite different from encryption. there is no key, and it’s meant to be impossible (or very very difficult) to go from the output back to the input. a hash function takes some input data of any size, and creates a summary or "digest" of that data. the output is a fixed size.
Tryhackme Hashing Crypto 101 Ctrl Alt Sec We covered different hashing concepts and its algorithms as well as the goal of hashing. this was part of the web fundamentals pathway from tryhackme. please watch the video at the bottom for full detailed explanation of the walkthrough. Hashing crypto 101 tryhackme 186 views 10 months ago hashing crypto 101 tryhackme more. To strengthen my fundamentals, i completed the tryhackme — encryption: crypto 101 room. this blog is a step by step walkthrough of how i solved each task, what i learned, and why it. Explore various symmetric and asymmetric encryption algorithms. discover the usage of hashing algorithms in everyday systems.
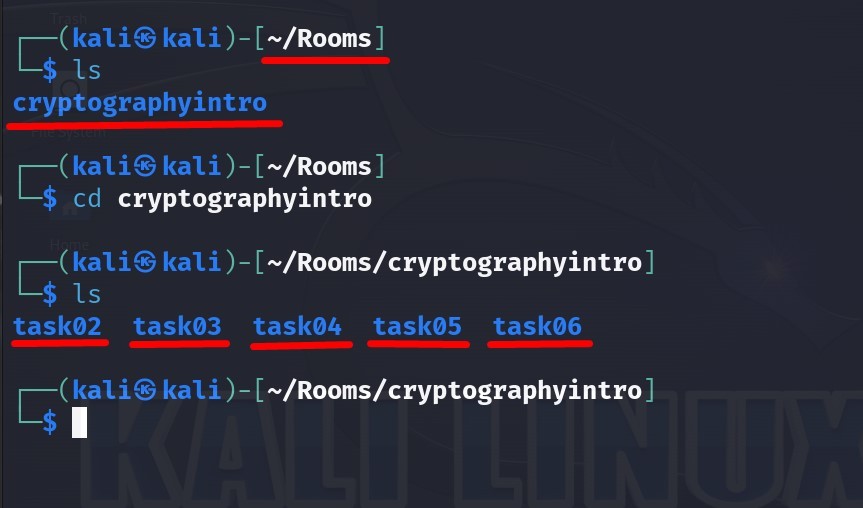
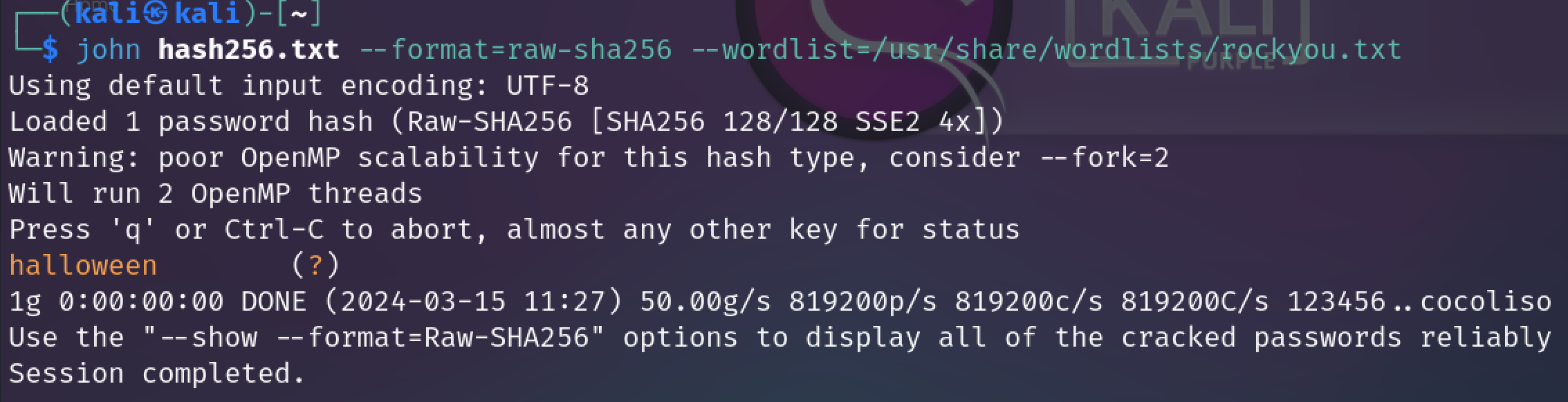
Introduction To Cryptography Tryhackme Room Walkthrough Hacklido To strengthen my fundamentals, i completed the tryhackme — encryption: crypto 101 room. this blog is a step by step walkthrough of how i solved each task, what i learned, and why it. Explore various symmetric and asymmetric encryption algorithms. discover the usage of hashing algorithms in everyday systems. Hash functions are quite different from encryption. there is no key, and it’s meant to be impossible (or very very difficult) to go from the output back to the input. a hash function takes some input data of any size, and creates a summary or "digest" of that data. the output is a fixed size. Hey, welcome back to my tryhackme walkthrough writeup! in this post, we will explore the hashing crypto101 room together!. Hmac is a method of using a cryptographic hashing function to verify the authenticity and integrity of data. the tryhackme vpn uses hmac sha512 for message authentication, which you can see in the terminal output. Dive into the crypto 101 room on tryhackme! this walkthrough covers the basics of cryptography, focusing on hashing—an essential concept in cybersecurity.
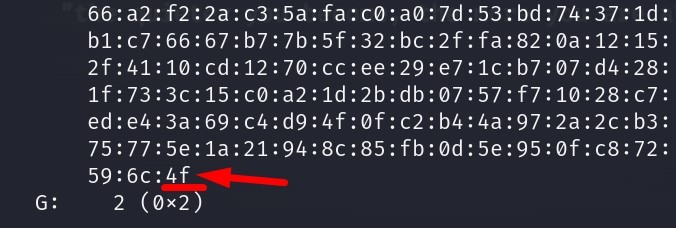
Introduction To Cryptography Tryhackme Room Walkthrough Hacklido Hash functions are quite different from encryption. there is no key, and it’s meant to be impossible (or very very difficult) to go from the output back to the input. a hash function takes some input data of any size, and creates a summary or "digest" of that data. the output is a fixed size. Hey, welcome back to my tryhackme walkthrough writeup! in this post, we will explore the hashing crypto101 room together!. Hmac is a method of using a cryptographic hashing function to verify the authenticity and integrity of data. the tryhackme vpn uses hmac sha512 for message authentication, which you can see in the terminal output. Dive into the crypto 101 room on tryhackme! this walkthrough covers the basics of cryptography, focusing on hashing—an essential concept in cybersecurity.

Hashing Basics Tryhackme Walkthrough By Orgeismail Medium Hmac is a method of using a cryptographic hashing function to verify the authenticity and integrity of data. the tryhackme vpn uses hmac sha512 for message authentication, which you can see in the terminal output. Dive into the crypto 101 room on tryhackme! this walkthrough covers the basics of cryptography, focusing on hashing—an essential concept in cybersecurity.

Tryhackme Cryptography Hashing Crypto101 Walkthrough By
Comments are closed.