Transposition Cipher Wrapatila

Transposition Cipher Code Updted Date 10 4 2012 Pdf Cipher Transposition cipher is an encryption method that rearranges the characters in a message into another order arrangement defined by a transposition key (or permutation key). Rail fence cipher adalah salah satu jenis transposition cipher, yang menggunakan prinsip seperti rel kereta api yang terdapat dua buah jalur besi dan kayu jembatan ditengah tengahnya.
Transposition Cipher Wrapatila Transposition ciphers are an essential part of cryptography that uses systematic shuffling of plain text characters or bits to secure data by altering their positions based on some defined way or algorithm. In cryptography, a transposition cipher (also known as a permutation cipher) is a method of encryption which scrambles the positions of characters (transposition) without changing the characters themselves. Penelitian ini merupakan penelitian deskriptif dengan pendekatan rekayasa perangkat lunak. dengan menggunakan metode prototype, penelitian ini merancang aplikasi kriptografi algoritma cipher transposition yang dapat menjamin keamanan suatu pesan data. A detailed guide to transposition ciphers: what they are, how they work, how to encode decode, how to detect them using frequency clues, and how to break common types like rail fence and columnar.
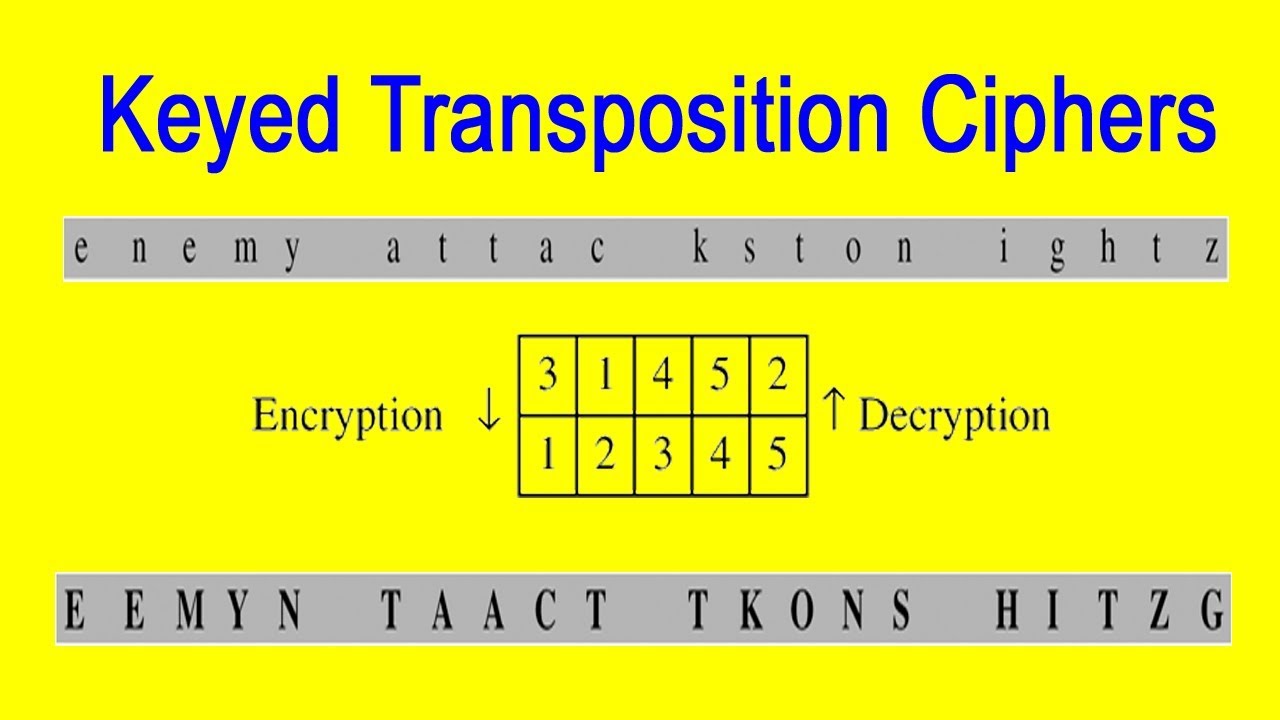
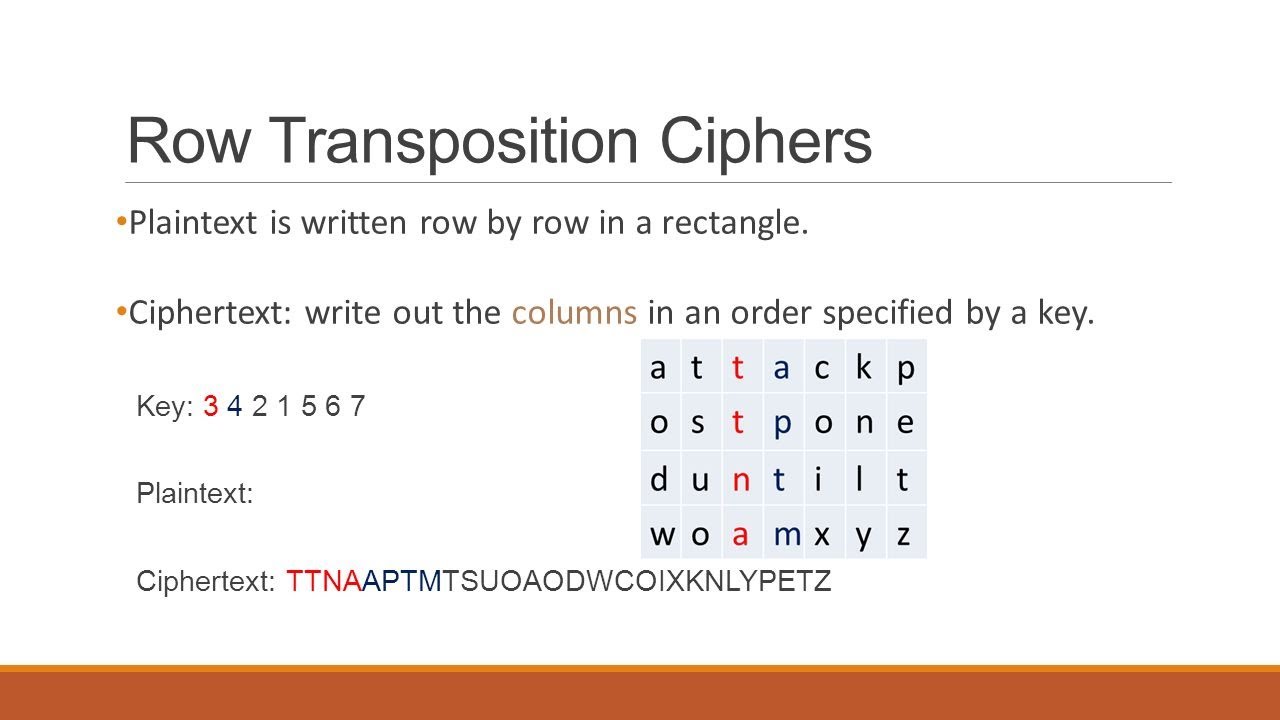
Transposition Cipher Wrapatila Penelitian ini merupakan penelitian deskriptif dengan pendekatan rekayasa perangkat lunak. dengan menggunakan metode prototype, penelitian ini merancang aplikasi kriptografi algoritma cipher transposition yang dapat menjamin keamanan suatu pesan data. A detailed guide to transposition ciphers: what they are, how they work, how to encode decode, how to detect them using frequency clues, and how to break common types like rail fence and columnar. Utilising patterns of language to connect word fragments and arrange them to build a word is a more effective strategy. in this chapter, we will see different types of transposition cipher algorithms, their working principles, and their implementation in different ways. Cipher substitusi homofonik (homophonic substitution cipher) setiap huruf plainteks diganti dengan salah satu huruf atau pasangan huruf cipherteks yang mungkin. Unlike substitution ciphers, which change the content of the plaintext, transposition ciphers change the order of units in the plaintext but leave the values unchanged. There are many different types of transposition ciphers, including the rail fence cipher, route cipher, myszkowski transposition cipher, and disrupted transposition cipher. this chapter covers a simple transposition cipher called the columnar transposition cipher.
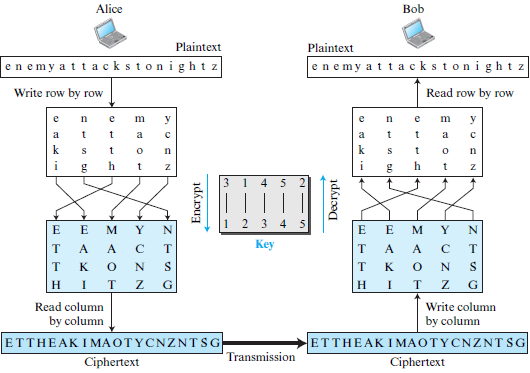
Transposition Cipher Wrapatila Utilising patterns of language to connect word fragments and arrange them to build a word is a more effective strategy. in this chapter, we will see different types of transposition cipher algorithms, their working principles, and their implementation in different ways. Cipher substitusi homofonik (homophonic substitution cipher) setiap huruf plainteks diganti dengan salah satu huruf atau pasangan huruf cipherteks yang mungkin. Unlike substitution ciphers, which change the content of the plaintext, transposition ciphers change the order of units in the plaintext but leave the values unchanged. There are many different types of transposition ciphers, including the rail fence cipher, route cipher, myszkowski transposition cipher, and disrupted transposition cipher. this chapter covers a simple transposition cipher called the columnar transposition cipher.
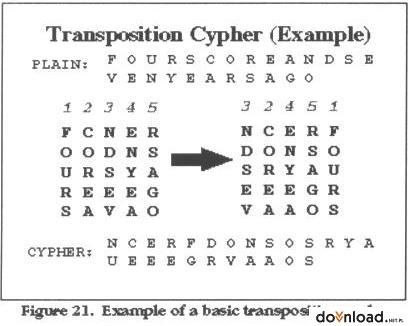
Transposition Cipher Crack The Codes Unlike substitution ciphers, which change the content of the plaintext, transposition ciphers change the order of units in the plaintext but leave the values unchanged. There are many different types of transposition ciphers, including the rail fence cipher, route cipher, myszkowski transposition cipher, and disrupted transposition cipher. this chapter covers a simple transposition cipher called the columnar transposition cipher.

Lecture 3 Transposition Ciphers Pdf Cipher Secure Communication
Comments are closed.