Transposition Cipher Pdf Computers

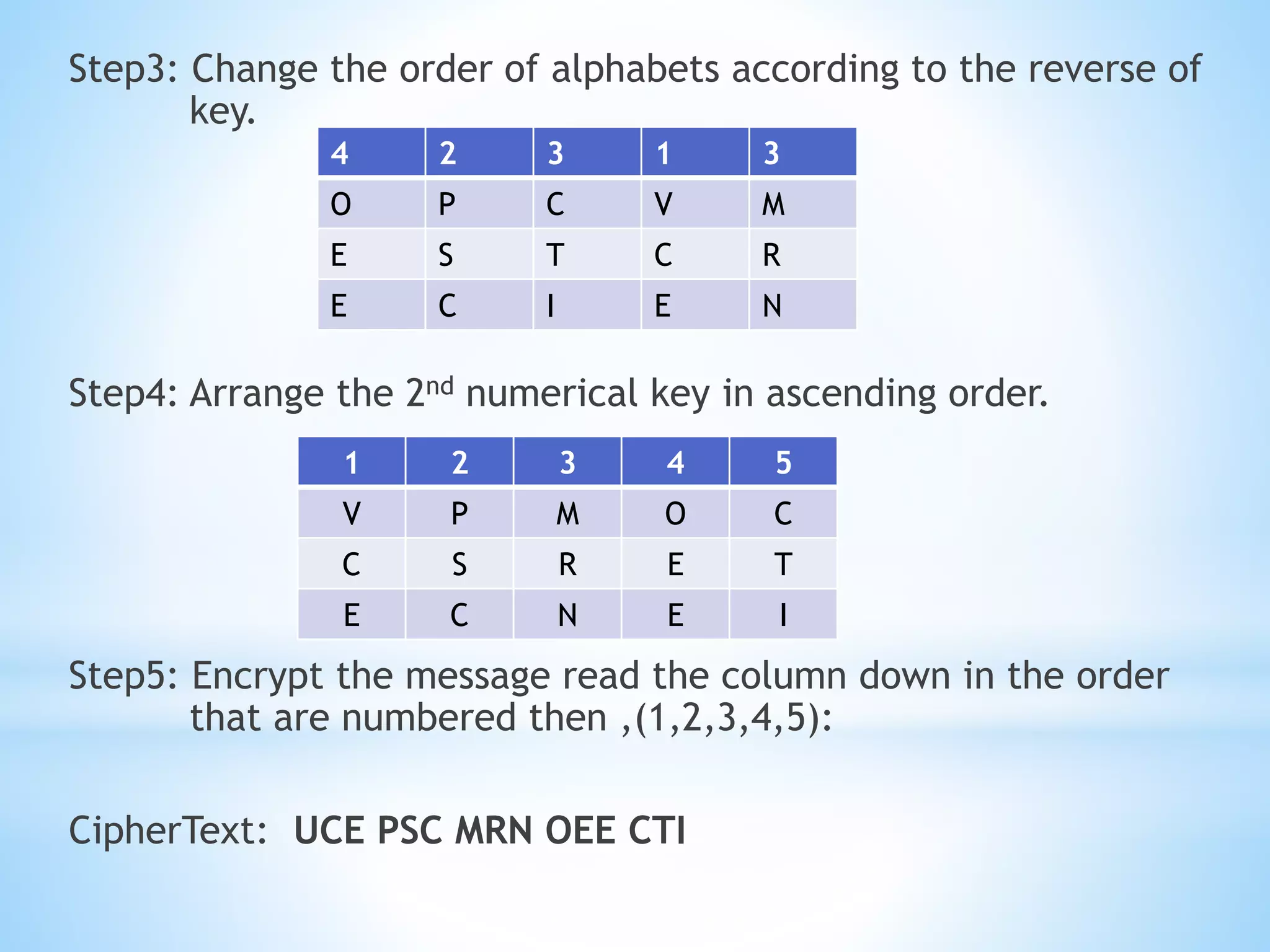
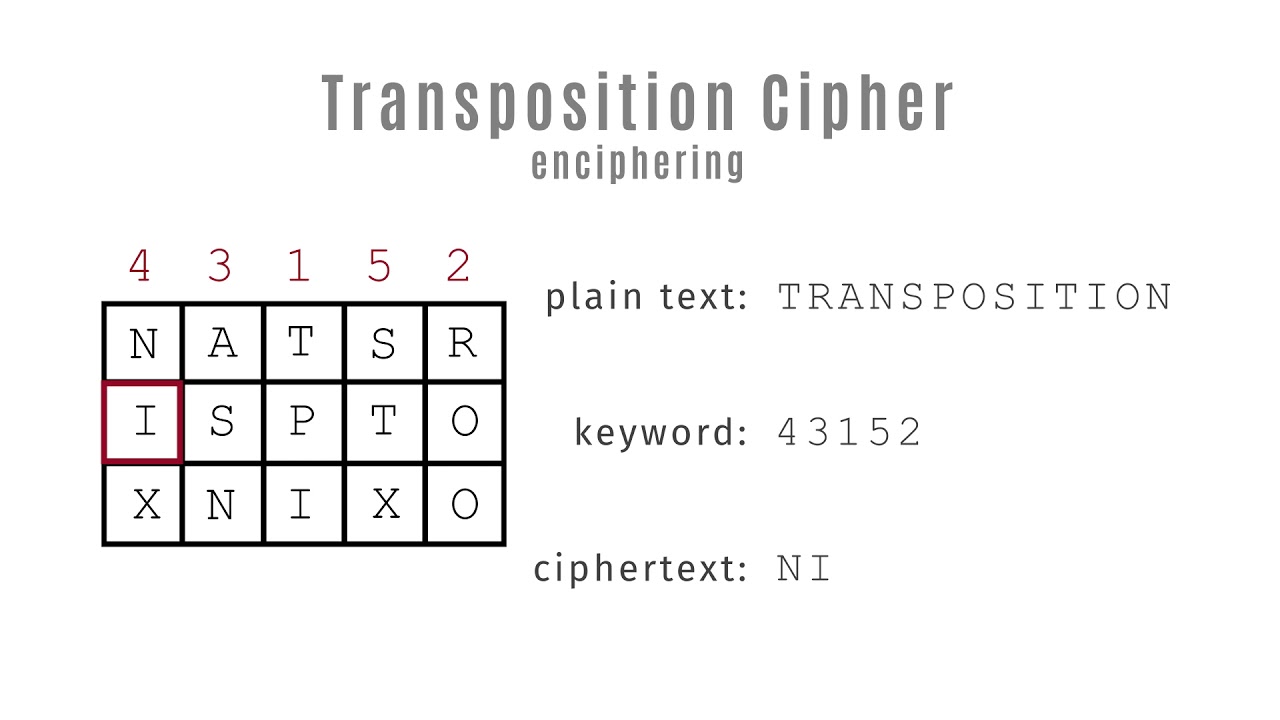
Transposition Cipher Pdf Computers Transposition is another important building block for encryption. a product cipher is the combination of two or more encryption steps. A column permutation cipher is very similar to the generic transposition cipher described in the introduction. you write down the message in a grid, and then read off the cipher text in columns instead of rows.
Transposition Cipher Techniques Pptx Cryptology: transposition ciphers. dr. chuckrocca [email protected]. sites.wcsu.edu cryptology c.f.roccajr. (wcsu) transposition 1 13. definitions. table of contents. 1definitions. 2middleages(ca. 600 1400ce) 3johnfalconer(ca. 1680) 4laterexamples. 5summary. c.f.roccajr. (wcsu) transposition 2 13. definitions. transposition cipher. Transposition cipher free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses different types of transposition ciphers including rail fence cipher and columnar transposition cipher. The observant cryptanalyst looks for telltale patterns in substitution and transposition ciphers. the cryptanalyst uses persistence and best guesses, look ing for any clue to ferret out patterns. in chapter 2, we show how a cryptanalyst uses letter frequency patterns. What we see characterizes ciphertext that has been encrypted using a transposition cipher. up to this point, the ciphers we have seen have been substitution ciphers. plaintext frequencies are transferred to, likely different, ciphertext letters or blocks.
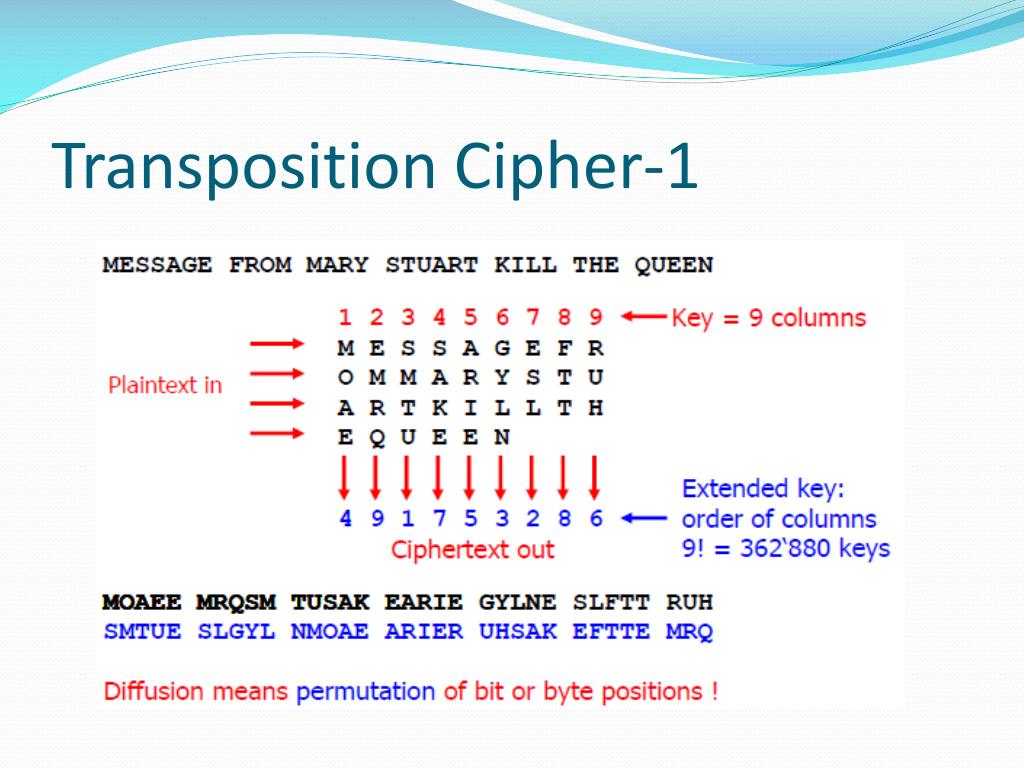
Ppt Terminology And Classical Cryptology Powerpoint Presentation The observant cryptanalyst looks for telltale patterns in substitution and transposition ciphers. the cryptanalyst uses persistence and best guesses, look ing for any clue to ferret out patterns. in chapter 2, we show how a cryptanalyst uses letter frequency patterns. What we see characterizes ciphertext that has been encrypted using a transposition cipher. up to this point, the ciphers we have seen have been substitution ciphers. plaintext frequencies are transferred to, likely different, ciphertext letters or blocks. Pdf | this paper explores classical encryption techniques used for secure communication, focusing on substitution and transposition methods. Phase 2: write cipher out using column row route (off by route). we’ll depend on column direction to get ciphertext. note : the key will be here the route of writing the message into specified block. In this lab you are going to examine some ciphertexts that have been enciphered using transposition ciphers. you may also use the internet to look at common methods of transpositions. When caesar cipher substitution and rail fence transposition techniques are used individually, cipher text obtained is easy to crack. this talk will present a perspective on combination of techniques substitution and transposition.

Columnar Transposition Cipher Pdf Secrecy Cyberwarfare Pdf | this paper explores classical encryption techniques used for secure communication, focusing on substitution and transposition methods. Phase 2: write cipher out using column row route (off by route). we’ll depend on column direction to get ciphertext. note : the key will be here the route of writing the message into specified block. In this lab you are going to examine some ciphertexts that have been enciphered using transposition ciphers. you may also use the internet to look at common methods of transpositions. When caesar cipher substitution and rail fence transposition techniques are used individually, cipher text obtained is easy to crack. this talk will present a perspective on combination of techniques substitution and transposition.

Lecture 10 Transposition Cipher Pdf Espionage Techniques In this lab you are going to examine some ciphertexts that have been enciphered using transposition ciphers. you may also use the internet to look at common methods of transpositions. When caesar cipher substitution and rail fence transposition techniques are used individually, cipher text obtained is easy to crack. this talk will present a perspective on combination of techniques substitution and transposition.
Transposition Cipher Youtube
Comments are closed.