Transition To Post Quantum Cryptography

Irma International Org Pre Quantum To Post Quantum Cryptography This report describes nist’s expected approach to transitioning from quantum vulnerable cryptographic algorithms to post quantum digital signature algorithms and key establishment schemes. The eu member states, supported by the commission, issued a roadmap and timeline to start using a more complex form of cybersecurity, the so called post quantum cryptography (pqc).
Post Quantum Cryptography The Future Of Secure Computing Klizos Breakthroughs in the race to develop advanced quantum computing threaten our current systems which secure communications, ensure authenticity, and protect sensitive data at rest and in transit, necessitating the migration to post quantum cryptography (pqc). The transition to post quantum cryptography (pqc) has gained momentum amid advancements like nist’s standardization of quantum resistant algorithms. key developments include addressing implementation challenges, enhancing crypto agility, and exploring hybrid approaches. Nist finalized its first post quantum cryptography (pqc) standards in august 2024, triggering mandatory transition timelines for federal agencies and cascading compliance obligations across industries that rely on fips approved algorithms. This report describes nist’s expected approach to transitioning from quantum vulnerable cryptographic algorithms to post quantum digital signature algorithms and key establishment schemes.
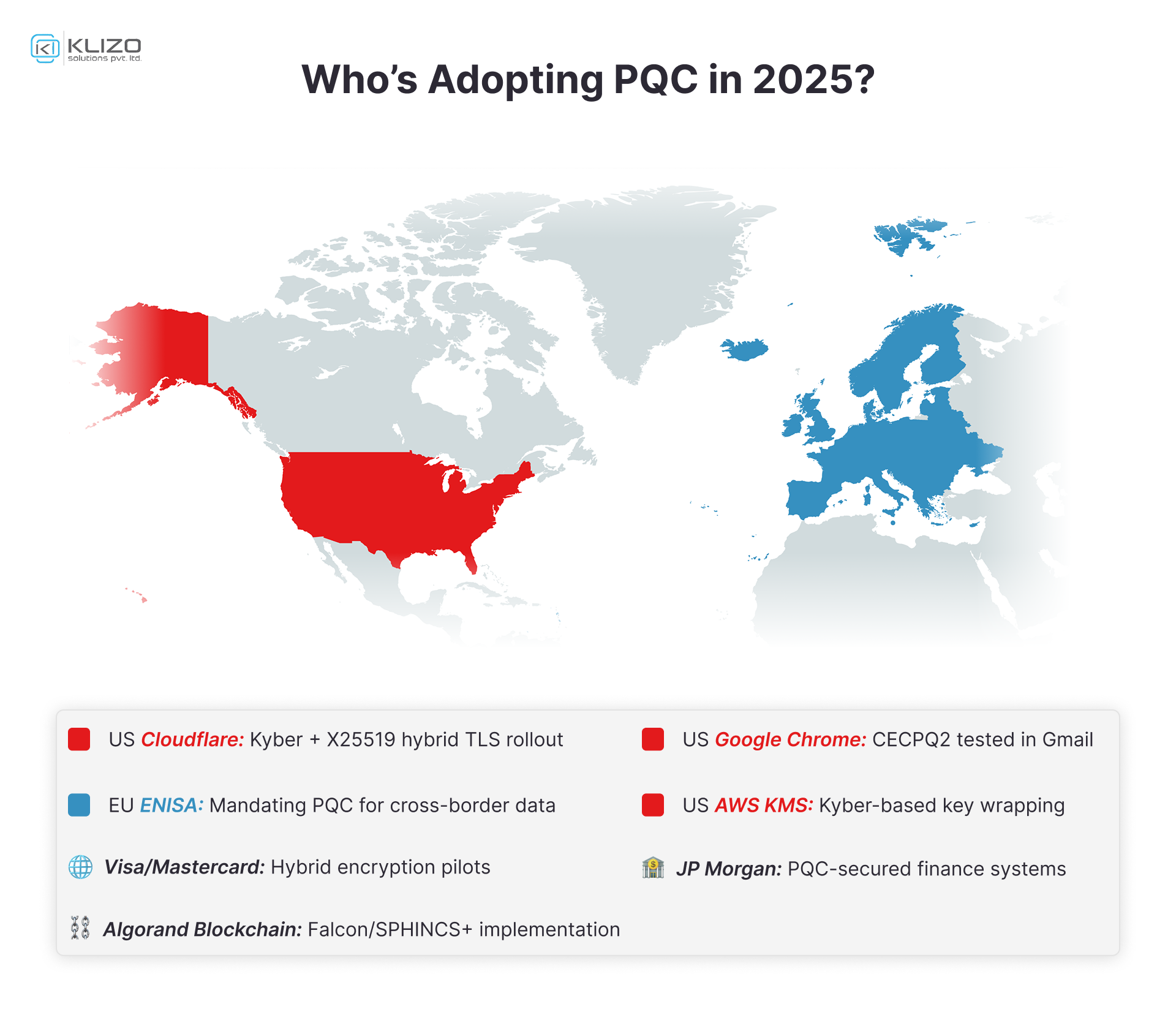
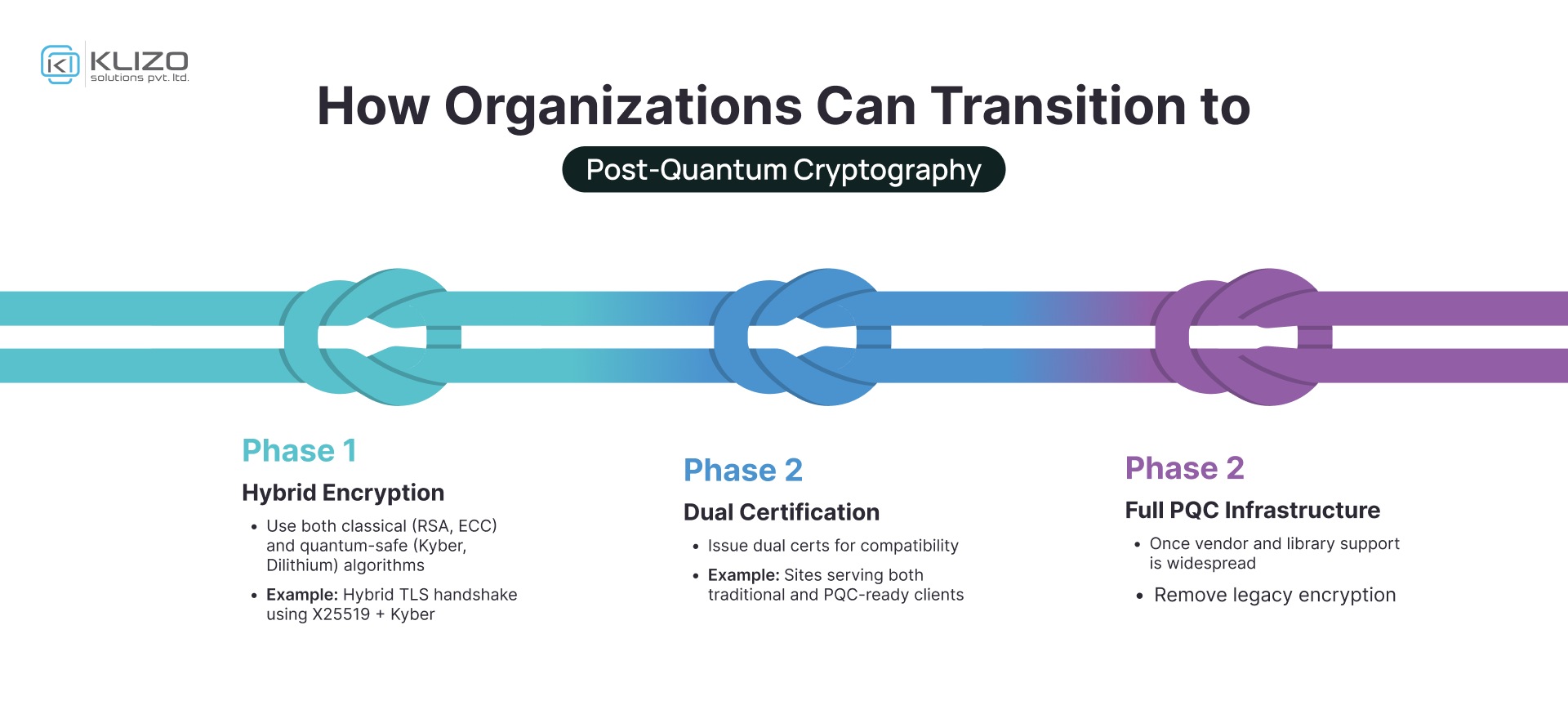
Post Quantum Cryptography The Future Of Secure Computing Klizos Nist finalized its first post quantum cryptography (pqc) standards in august 2024, triggering mandatory transition timelines for federal agencies and cascading compliance obligations across industries that rely on fips approved algorithms. This report describes nist’s expected approach to transitioning from quantum vulnerable cryptographic algorithms to post quantum digital signature algorithms and key establishment schemes. Post quantum cryptography (pqc) offers mathematically secure alternatives, but migration is a complex, multi year undertaking. unlike past transitions (aes, sha 2, tls 1.3), pqc migration requires larger parameter sizes, hybrid cryptographic schemes, and unprecedented ecosystem coordination. Some service providers and vendors have begun their transition to pqc, with some offering pqc only solutions and products. the shift to pqc will happen at different speeds and will depend on factors such as cost, dependent technology updates and legacy interoperability. The transition to post quantum cryptography does not solve the fundamental problem of cryptographic vulnerability to computational advances. it simply postpones the problem. within decades, new. Quantum computers can break traditional algorithms that have been in use for the last 20 years, making it critical to begin transitioning to new quantum resistant algorithms to protect sensitive data now and in the future. explore recent and upcoming windows changes in certificates, cryptography, and tls apis relevant to post quantum cryptography.
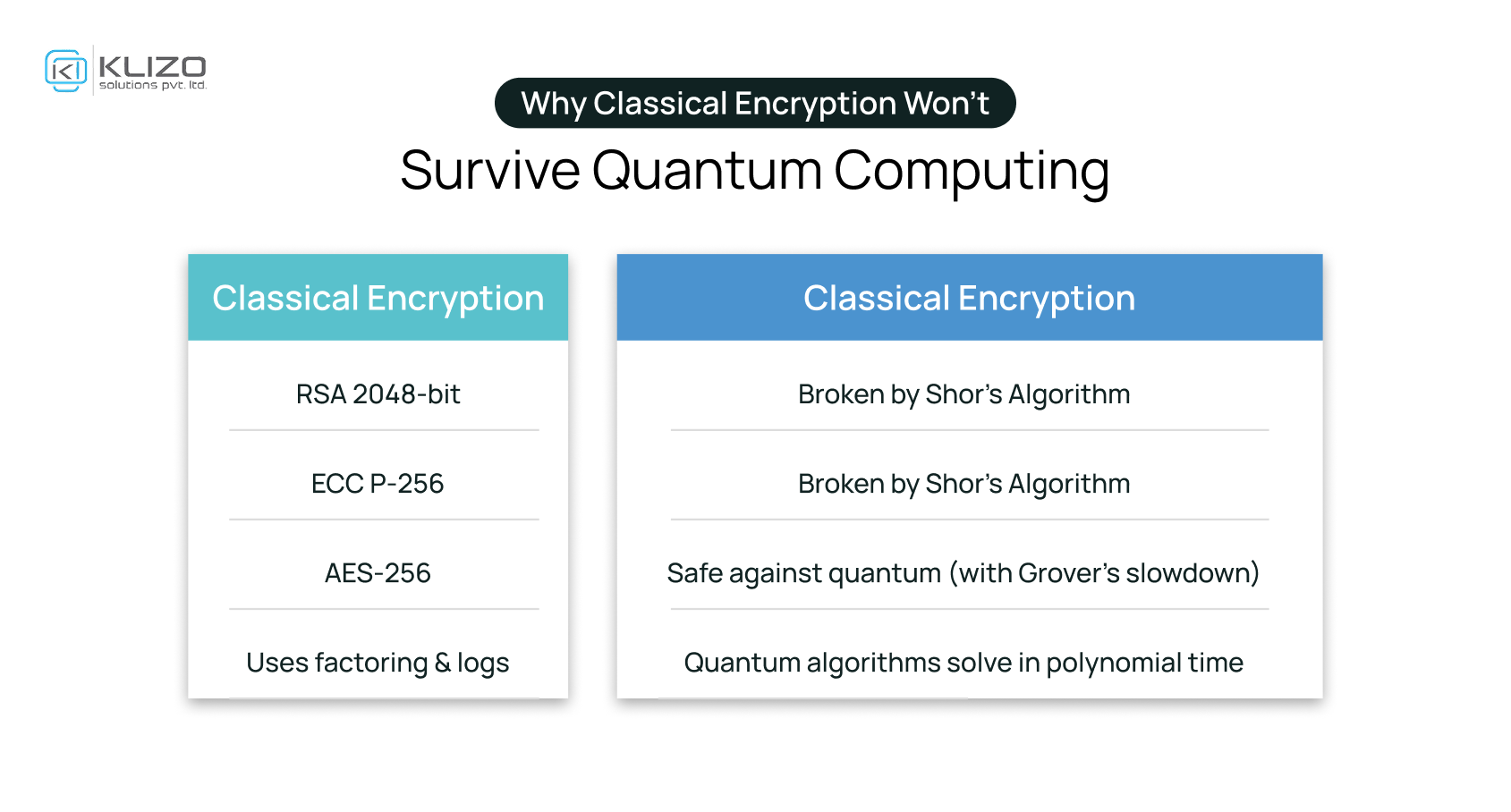
Post Quantum Cryptography The Future Of Secure Computing Klizos Post quantum cryptography (pqc) offers mathematically secure alternatives, but migration is a complex, multi year undertaking. unlike past transitions (aes, sha 2, tls 1.3), pqc migration requires larger parameter sizes, hybrid cryptographic schemes, and unprecedented ecosystem coordination. Some service providers and vendors have begun their transition to pqc, with some offering pqc only solutions and products. the shift to pqc will happen at different speeds and will depend on factors such as cost, dependent technology updates and legacy interoperability. The transition to post quantum cryptography does not solve the fundamental problem of cryptographic vulnerability to computational advances. it simply postpones the problem. within decades, new. Quantum computers can break traditional algorithms that have been in use for the last 20 years, making it critical to begin transitioning to new quantum resistant algorithms to protect sensitive data now and in the future. explore recent and upcoming windows changes in certificates, cryptography, and tls apis relevant to post quantum cryptography.
Comments are closed.