Top 6 Bluetooth Vulnerabilities Thyrasec

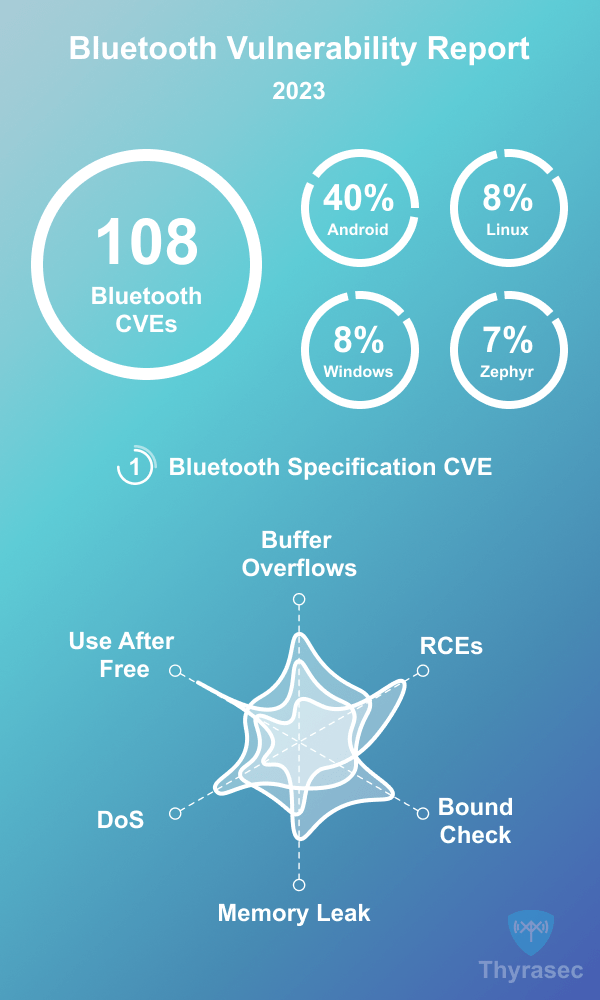
Top 6 Bluetooth Vulnerabilities Thyrasec Let’s go over the top bluetooth vulnerabilities you should consider in your product. are your devices vulnerable?. To give us a better understanding of the landscape of bluetooth security, we’ve compiled data about all the vulnerabilities found in 2023. here’s the breakdown of the top bluetooth vulnerabilities that were reported in 2023: there’s a lot of nuance with cve vulnerability data.

Vulnerabilities Found In Bluetooth Low Energy Gives Hackers Access To Explore the latest vulnerabilities and security issues of bluetooth in the cve database. Track the latest bluetooth vulnerabilities and their associated exploits, patches, cvss and epss scores, proof of concept, links to malware, threat actors, and mitre att&ck ttp information. Discover the most critical bluetooth low energy (ble) cybersecurity vulnerabilities in this comprehensive guide. It may take a day or so for new bluetooth vulnerabilities to show up in the stats or in the list of recent security vulnerabilities. additionally vulnerabilities may be tagged under a different product or component name.

Thyrasec Discover the most critical bluetooth low energy (ble) cybersecurity vulnerabilities in this comprehensive guide. It may take a day or so for new bluetooth vulnerabilities to show up in the stats or in the list of recent security vulnerabilities. additionally vulnerabilities may be tagged under a different product or component name. Although it appears that the number of bluetooth vulnerabilities being discovered is rising again, we can take comfort that at least a vital protocol is being examined and improved upon. Bluetooth vulnerabilities in android, macos, ios, linux let attackers inject data 2024 has barely started, and a researcher has already publicly disclosed several vulnerabilities related to bluetooth …. Bluetooth technology, which facilitates wireless communication between billions of devices including smartphones, tablets, laptops, and internet of thing (iot). In this article we are going to discuss about some of the risks posed by bluetooth devices and some of the types of bluetooth device threats in our daily life and how the attack will work.

Thyrasec Although it appears that the number of bluetooth vulnerabilities being discovered is rising again, we can take comfort that at least a vital protocol is being examined and improved upon. Bluetooth vulnerabilities in android, macos, ios, linux let attackers inject data 2024 has barely started, and a researcher has already publicly disclosed several vulnerabilities related to bluetooth …. Bluetooth technology, which facilitates wireless communication between billions of devices including smartphones, tablets, laptops, and internet of thing (iot). In this article we are going to discuss about some of the risks posed by bluetooth devices and some of the types of bluetooth device threats in our daily life and how the attack will work.
Reviewing Ble And Bluetooth Vulnerabilities And Attacks Of 2023 Thyrasec Bluetooth technology, which facilitates wireless communication between billions of devices including smartphones, tablets, laptops, and internet of thing (iot). In this article we are going to discuss about some of the risks posed by bluetooth devices and some of the types of bluetooth device threats in our daily life and how the attack will work.
Comments are closed.